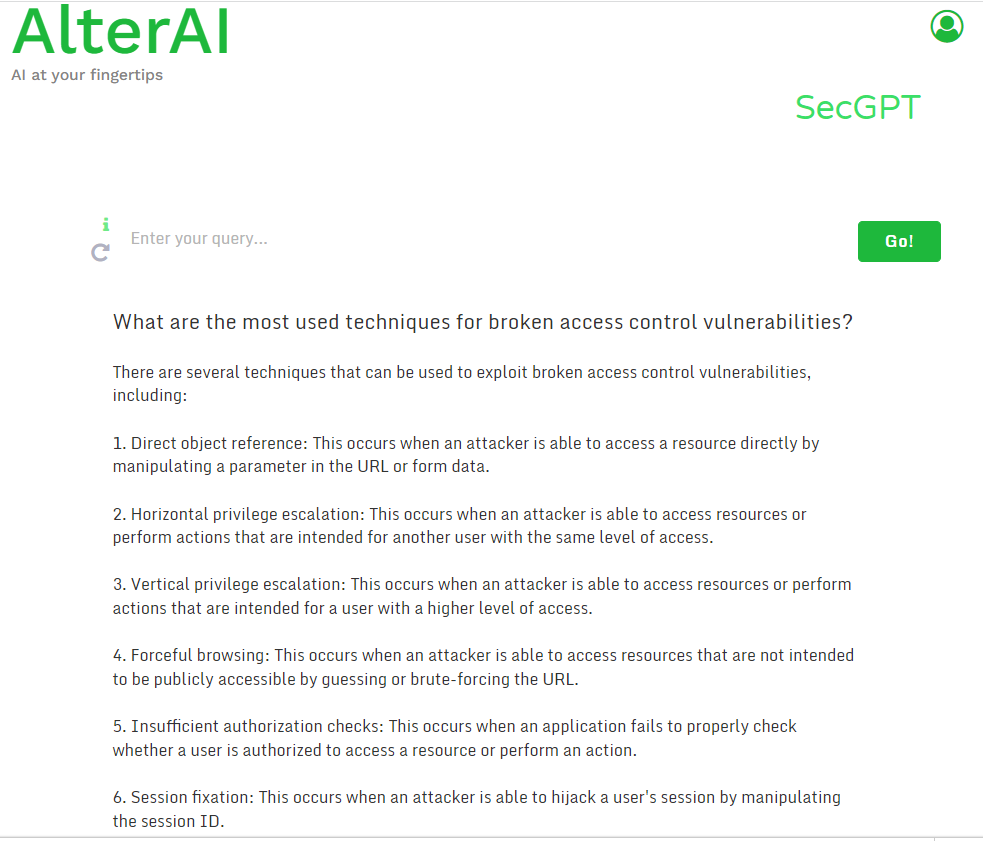
Broken Access Control attack vectors, by #ChatGPT4 👇 

1. IDOR
This occurs when an application exposes internal implementation objects, such as files, directories, or database keys, without proper authorization checks. Attackers can manipulate these references to gain unauthorized access to sensitive data.
This occurs when an application exposes internal implementation objects, such as files, directories, or database keys, without proper authorization checks. Attackers can manipulate these references to gain unauthorized access to sensitive data.
2. Privilege Escalation
An attacker could exploit insecure access controls to elevate their privileges within the application, allowing them to perform unauthorized actions or access sensitive data.
An attacker could exploit insecure access controls to elevate their privileges within the application, allowing them to perform unauthorized actions or access sensitive data.
3. Horizontal Privilege Escalation
This involves an attacker gaining unauthorized access to resources or functionalities meant for other users at the same privilege level, for example, accessing another user's account data.
This involves an attacker gaining unauthorized access to resources or functionalities meant for other users at the same privilege level, for example, accessing another user's account data.
4. Forced Browsing
An attacker could use forced browsing to access restricted areas or resources by manually manipulating URLs or directly requesting resources without proper authorization.
An attacker could use forced browsing to access restricted areas or resources by manually manipulating URLs or directly requesting resources without proper authorization.
5. Path Traversal
An attacker can exploit path traversal vulnerabilities to access sensitive files or directories outside of the intended scope by using "../" or similar patterns in user input fields.
An attacker can exploit path traversal vulnerabilities to access sensitive files or directories outside of the intended scope by using "../" or similar patterns in user input fields.
6. Missing Function Level Access Control
This occurs when the application does not enforce proper authorization checks on specific functions or features, allowing attackers to access them without the required permissions.
This occurs when the application does not enforce proper authorization checks on specific functions or features, allowing attackers to access them without the required permissions.
7. Token Hijacking
Attackers can intercept or manipulate authentication tokens, such as session cookies or JSON Web Tokens (JWTs), to impersonate other users or gain unauthorized access to resources.
Attackers can intercept or manipulate authentication tokens, such as session cookies or JSON Web Tokens (JWTs), to impersonate other users or gain unauthorized access to resources.
8. Insecure API Endpoints
APIs that do not enforce proper access controls can be exploited by attackers to perform unauthorized actions or access sensitive data.
APIs that do not enforce proper access controls can be exploited by attackers to perform unauthorized actions or access sensitive data.
9. Metadata Manipulation
Attackers can modify metadata, such as access control lists (ACLs) or object properties, to gain unauthorized access to resources.
Attackers can modify metadata, such as access control lists (ACLs) or object properties, to gain unauthorized access to resources.
10. Bypassing Access Control Checks
Attackers can exploit vulnerabilities in the access control implementation, such as logic flaws or insecure configurations, to bypass authorization checks and access restricted resources.
Attackers can exploit vulnerabilities in the access control implementation, such as logic flaws or insecure configurations, to bypass authorization checks and access restricted resources.
• • •
Missing some Tweet in this thread? You can try to
force a refresh