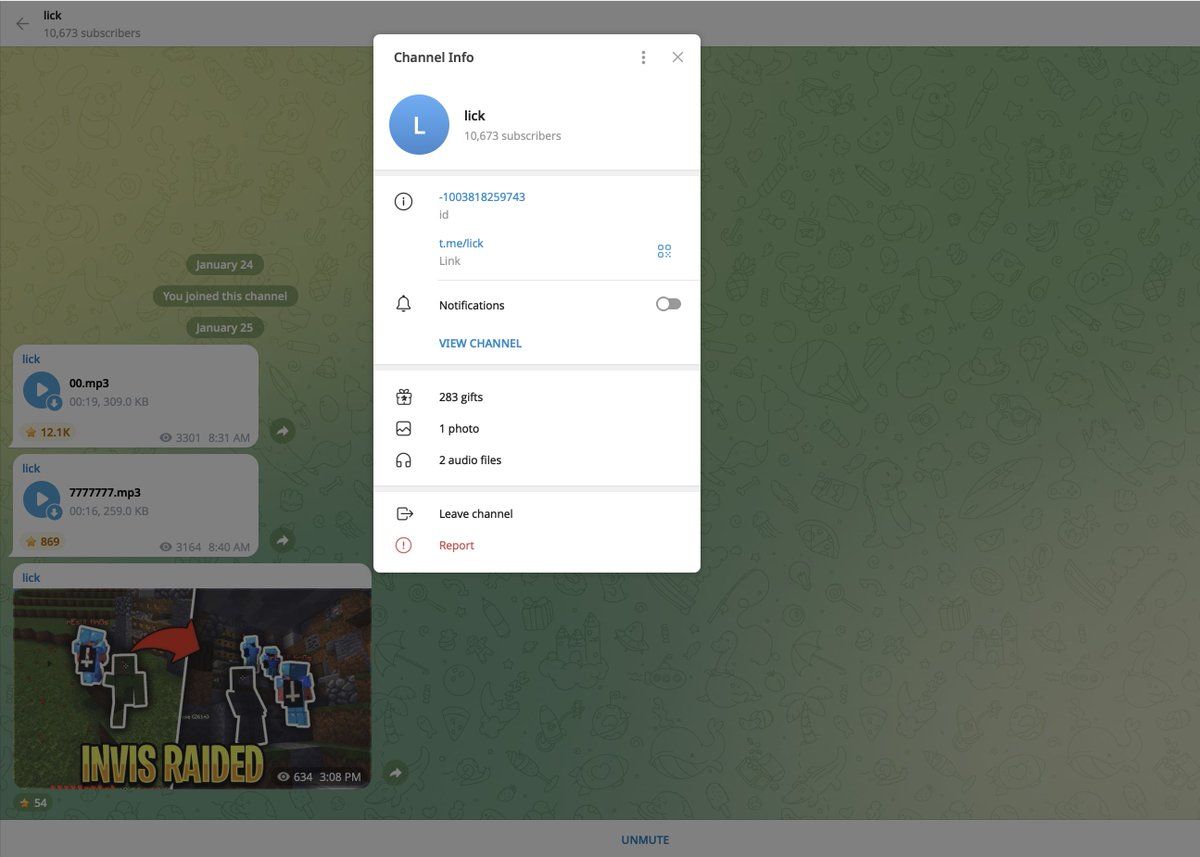
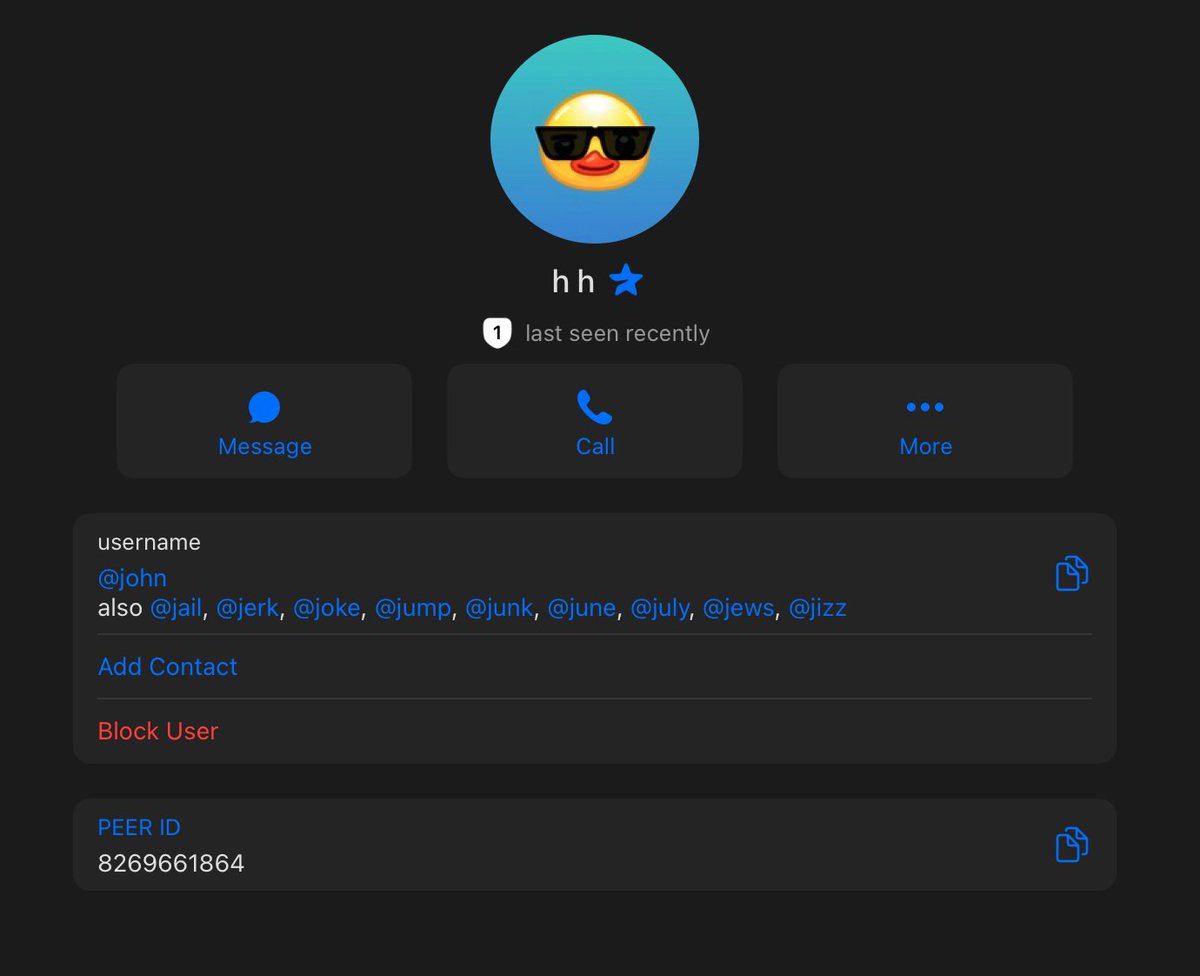
1/ An investigation into the YouTuber turned phishing scammer Blue (Jack) who has worked with Monkey Drainer and other drainer services to steal more than $1.5m






2/ Before Blue (Jack) began scamming in 2021 he amassed an audience of more than 122k subscribers by uploading gaming and trolling videos to YT.






3/ A leaked post from Blue’s personal Snapchat shows the ENS address cool-breeze.eth which purchased BAYC 8668 in October 2022.
0xC9a4Fe3DA7fb38e57fa14B273f05f190b535E395


0xC9a4Fe3DA7fb38e57fa14B273f05f190b535E395


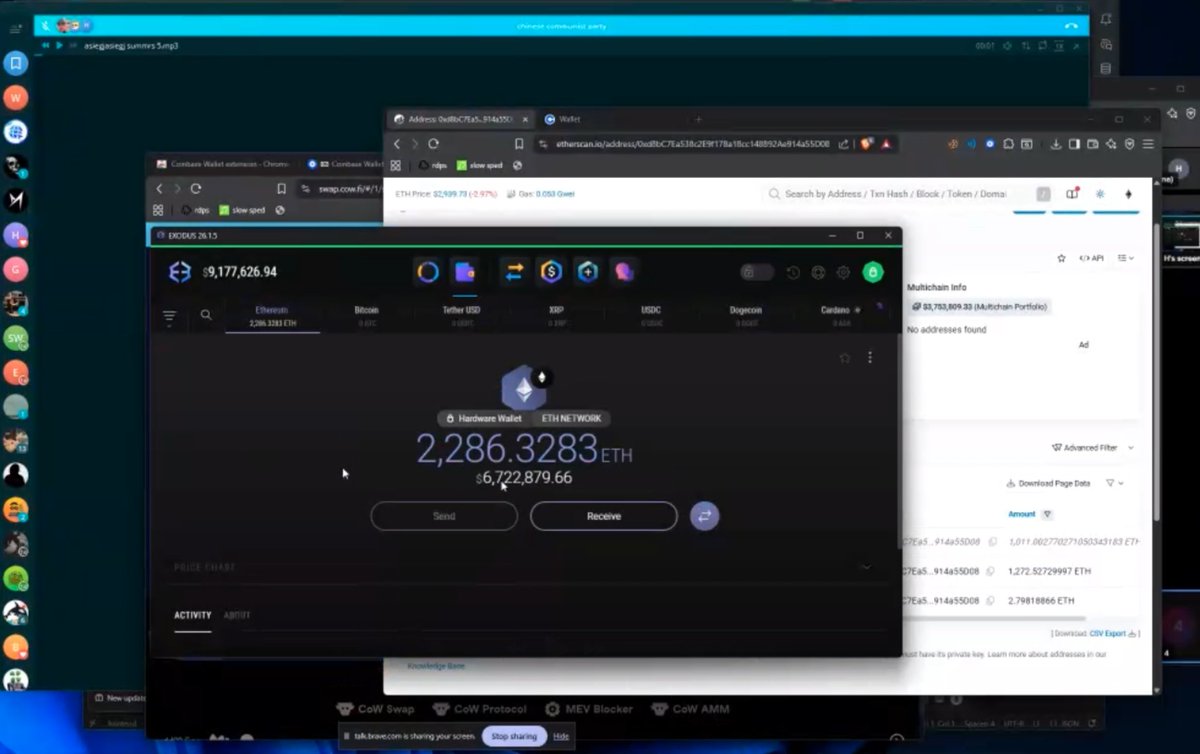
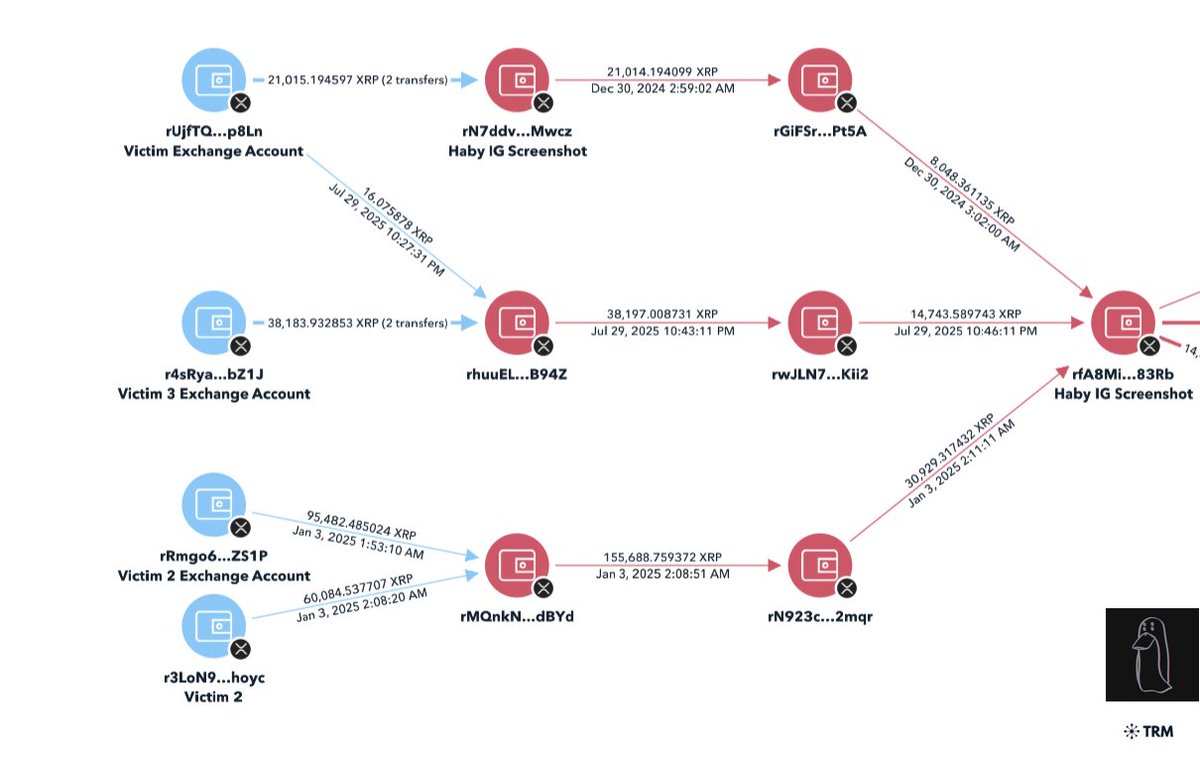
4/ Looking at the funding of this address is where things get interesting.
I observed inflows to cool-breeze.eth of more than 85 ETH (~1/3 of the stolen funds) directly from 8+ addresses involved with Monkey Drainer phishing scams.
Monkey is best known to have stolen $24m.


I observed inflows to cool-breeze.eth of more than 85 ETH (~1/3 of the stolen funds) directly from 8+ addresses involved with Monkey Drainer phishing scams.
Monkey is best known to have stolen $24m.


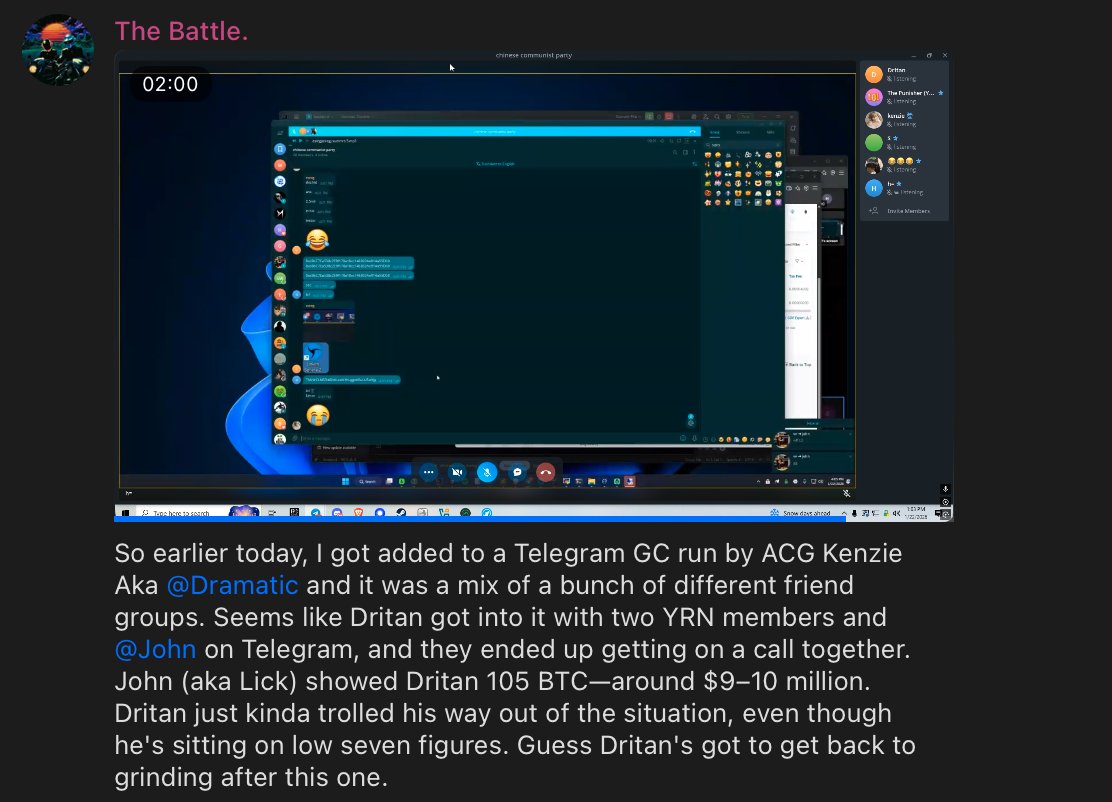
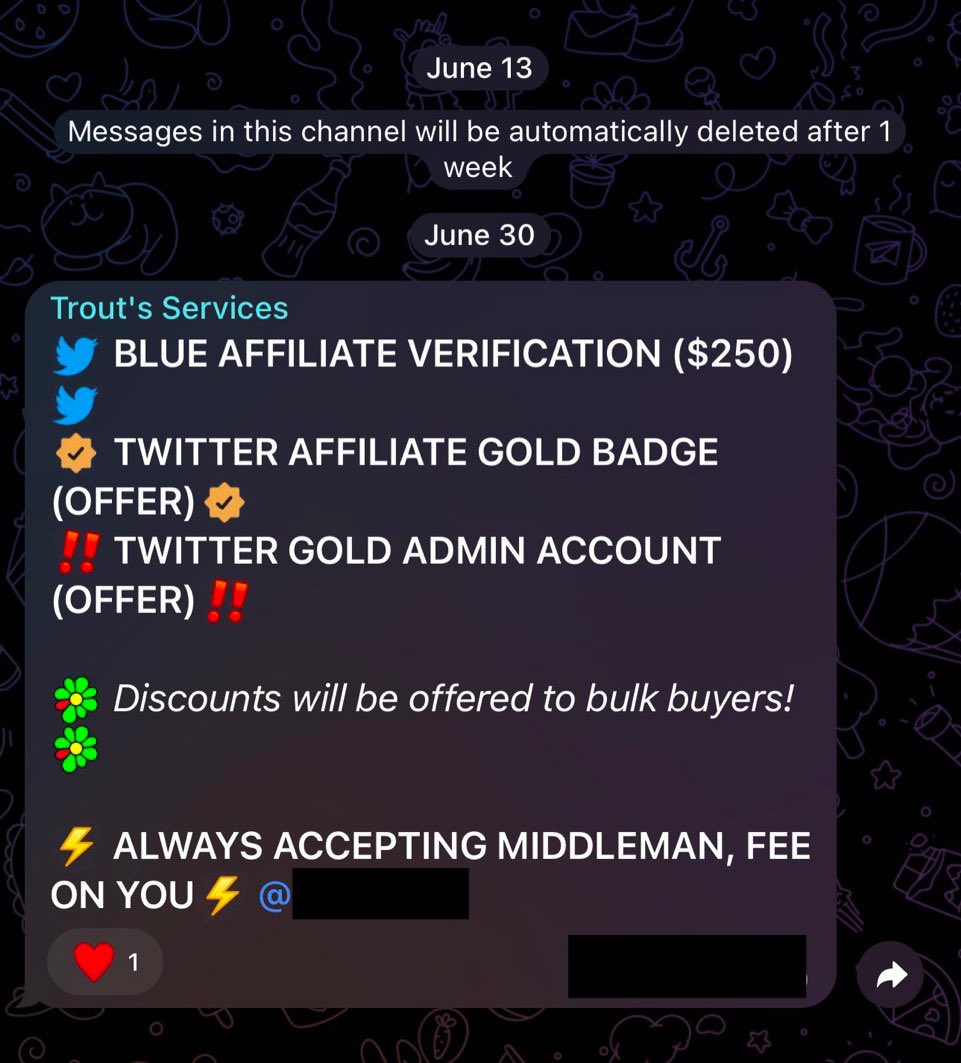
5/ On Discord Blue flexed his BAYC purchase and would share his methods scamming.
The second and third screenshot is from an internal Discord server where Blue would instruct his workers.



The second and third screenshot is from an internal Discord server where Blue would instruct his workers.



6/ Unfortunately Blue was robbed of his BAYC in late 2022 after allegedly scamming Monkey out of his cut from a phishing scam.
0x20428b7e16bdbe9b59478de05694d9aeb0d4393cfba65d46318e600581d7df55



0x20428b7e16bdbe9b59478de05694d9aeb0d4393cfba65d46318e600581d7df55


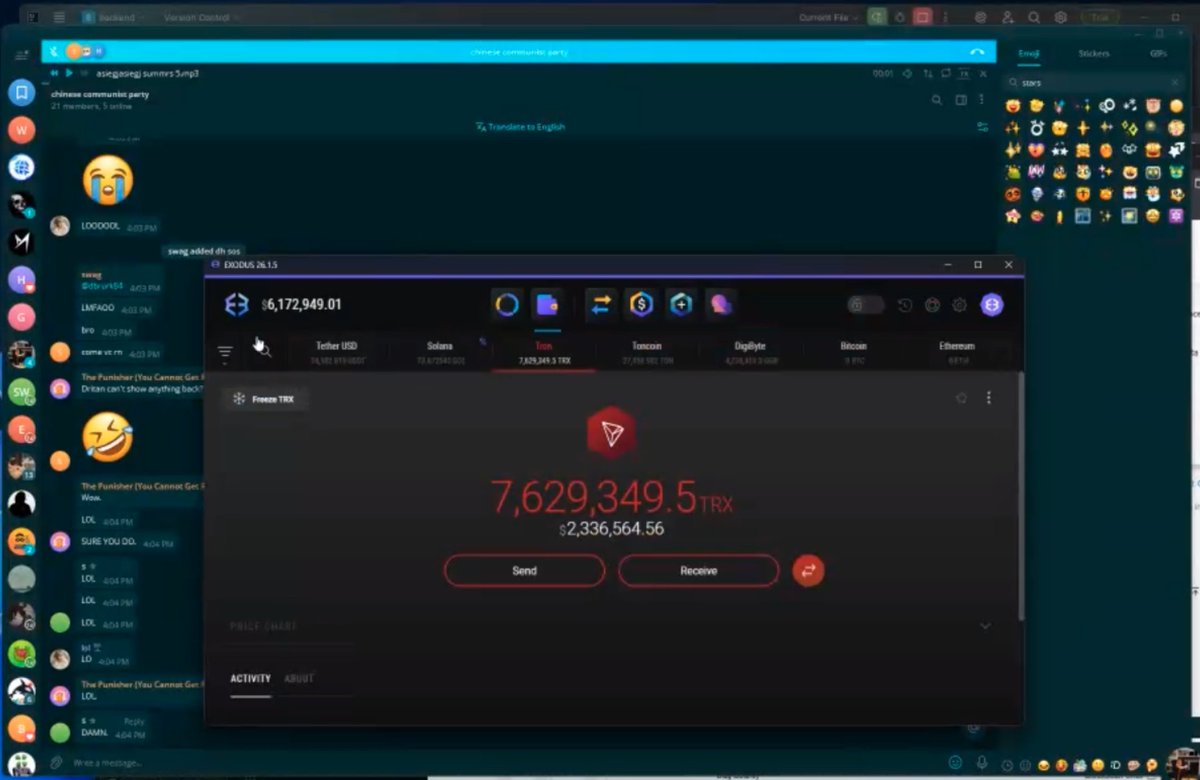
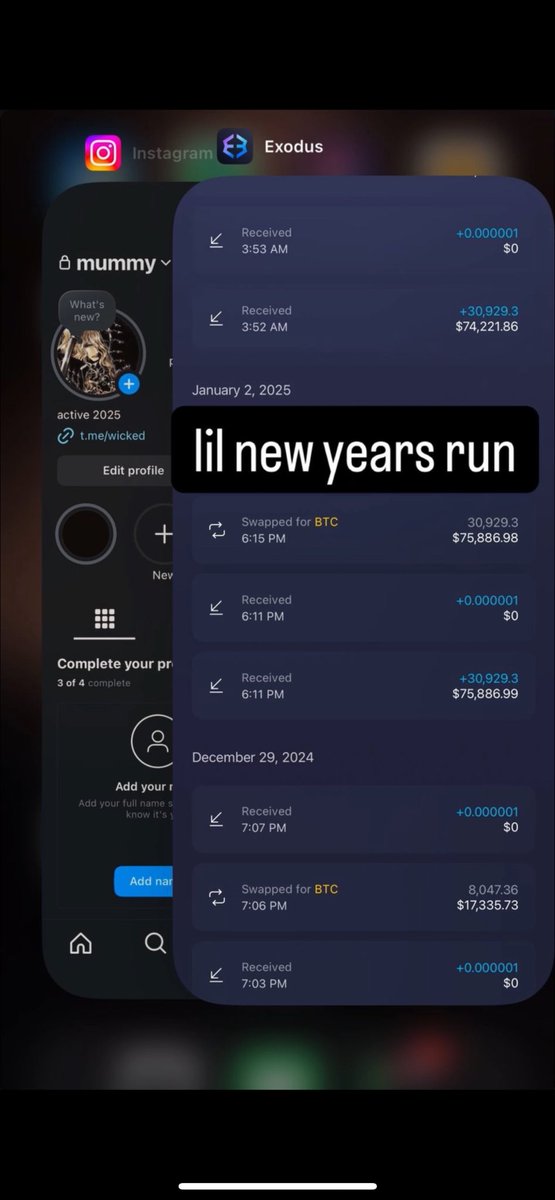
7/ This did not deter Blue as he soon began scamming again shortly after this setback with new ENS addresses.
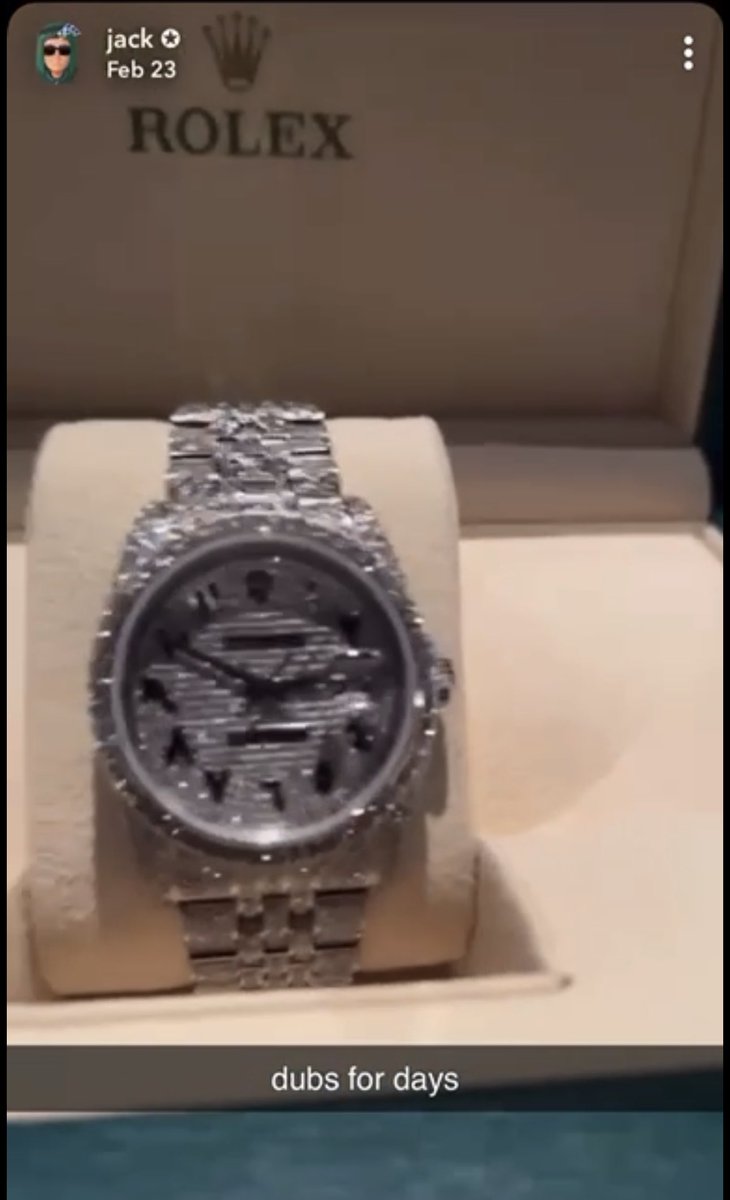
The stolen funds have been spent on luxury watch, car, shoes, Roblox items and gambling on Stake.
All this was flexed from his personal Snapchat.



The stolen funds have been spent on luxury watch, car, shoes, Roblox items and gambling on Stake.
All this was flexed from his personal Snapchat.


8/ Blue specializes in spamming on Twitter with verified accounts and two of his recent thefts include stolen assets from @g13m and @ystrickler while working with two different drainers. https://t.co/48ruH7mC9v



https://twitter.com/g13m/status/1675944577956474886
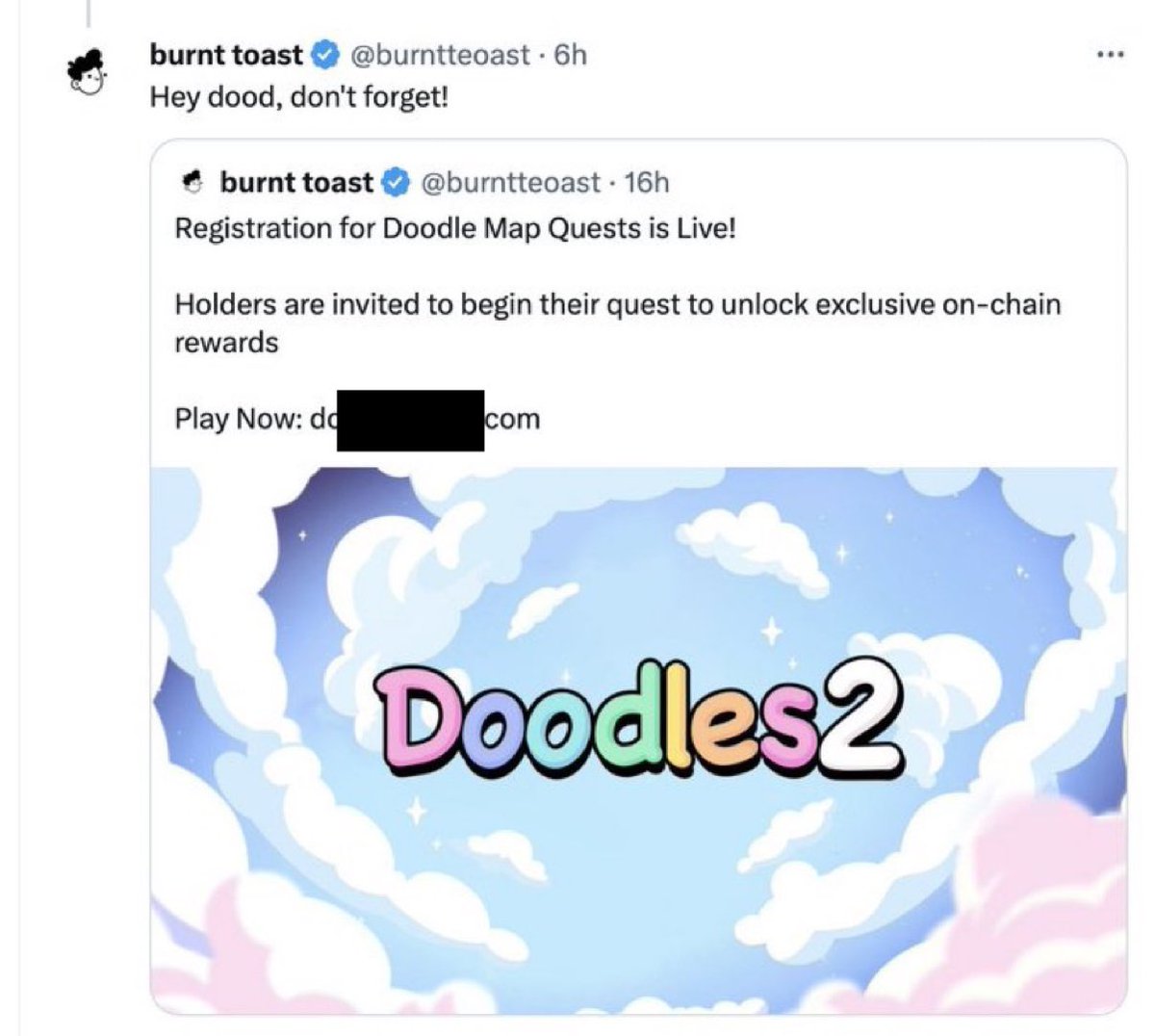

9/ July 3, 2023 @g13m was phished for 61.5 ETH and 93.3K USDT (~$213k) by a fake Doodles site.
Blue received 49 ETH and 74K USDT for himself after the drainer fee.
Blue’s address
0xa27b1d84b928059d78b7fdad9f7142d84e8689b4
Blue received 49 ETH and 74K USDT for himself after the drainer fee.
Blue’s address
0xa27b1d84b928059d78b7fdad9f7142d84e8689b4

10/ After Blue commissioned a video with his old BAYC and his other alias making fun of LoveMake losing his funds. 

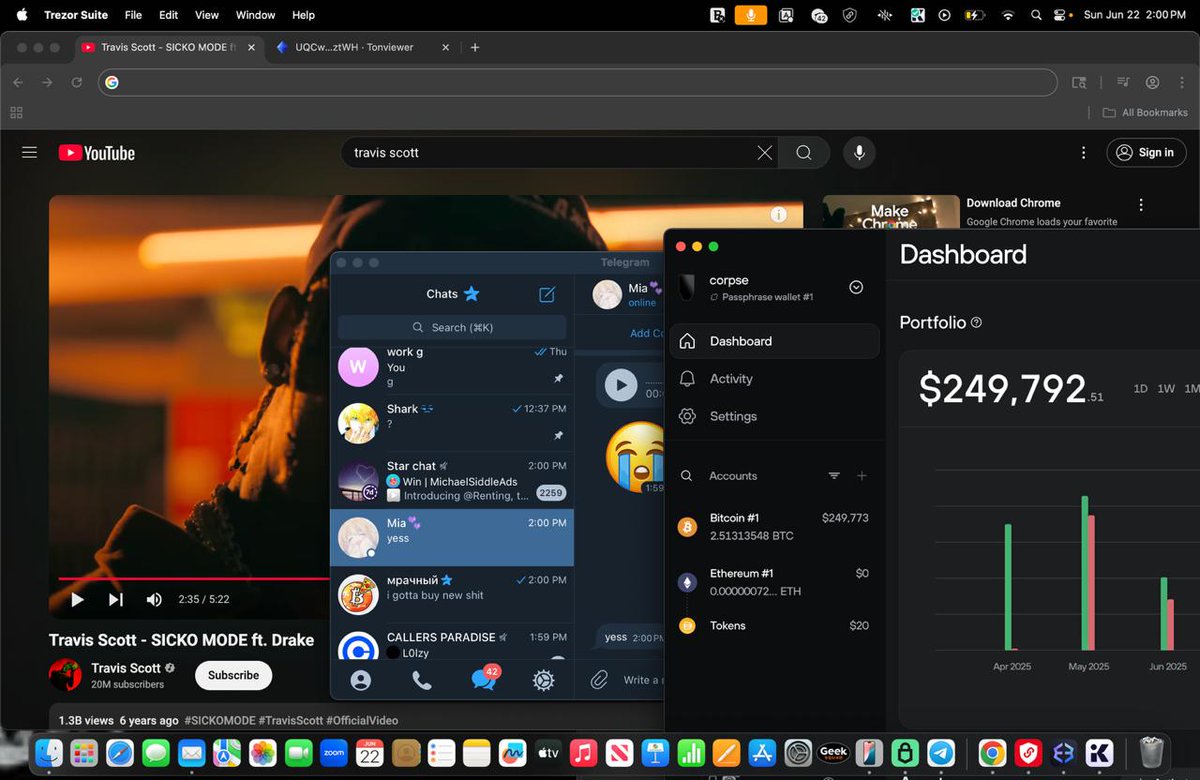
11/ Another recent theft includes yancey.eth who had a Milady & Squiggle phished (~12 ETH)
After the drainer fee Blue received 10.3 ETH to his ENS purplelobster.eth
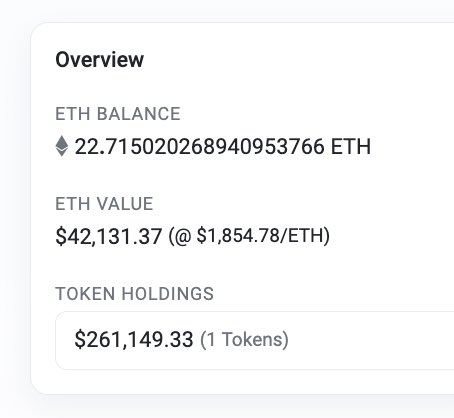
Blue moved the stolen funds to 0xad where $300k currently sits
0xad83776f97d956e4c9b33fd180e43910a8cb7db4



After the drainer fee Blue received 10.3 ETH to his ENS purplelobster.eth
Blue moved the stolen funds to 0xad where $300k currently sits
0xad83776f97d956e4c9b33fd180e43910a8cb7db4


12/ It’s disgusting to see these phishing scammers show zero remorse and spend the funds on tasteless items.
Additional information of Blue (Jack) has been shared with multiple of his victims to eventually help bring legal action.
Additional information of Blue (Jack) has been shared with multiple of his victims to eventually help bring legal action.
• • •
Missing some Tweet in this thread? You can try to
force a refresh