1/8: The #Rhadamanthys stealer uses Google Ads mimicking popular software such as AnyDesk, Zoom, and OBS to lure victims to their phishing sites to steal sensitive information.
Follow this thread as we discuss more about this threat. ⏬
Follow this thread as we discuss more about this threat. ⏬

2/8: Recently, we came across a new #Rhadamanthys variant that adds a payload bundle consisting of ransomware, a ClipBanker trojan, and a cryptocurrency miner, creating a more sophisticated threat. 

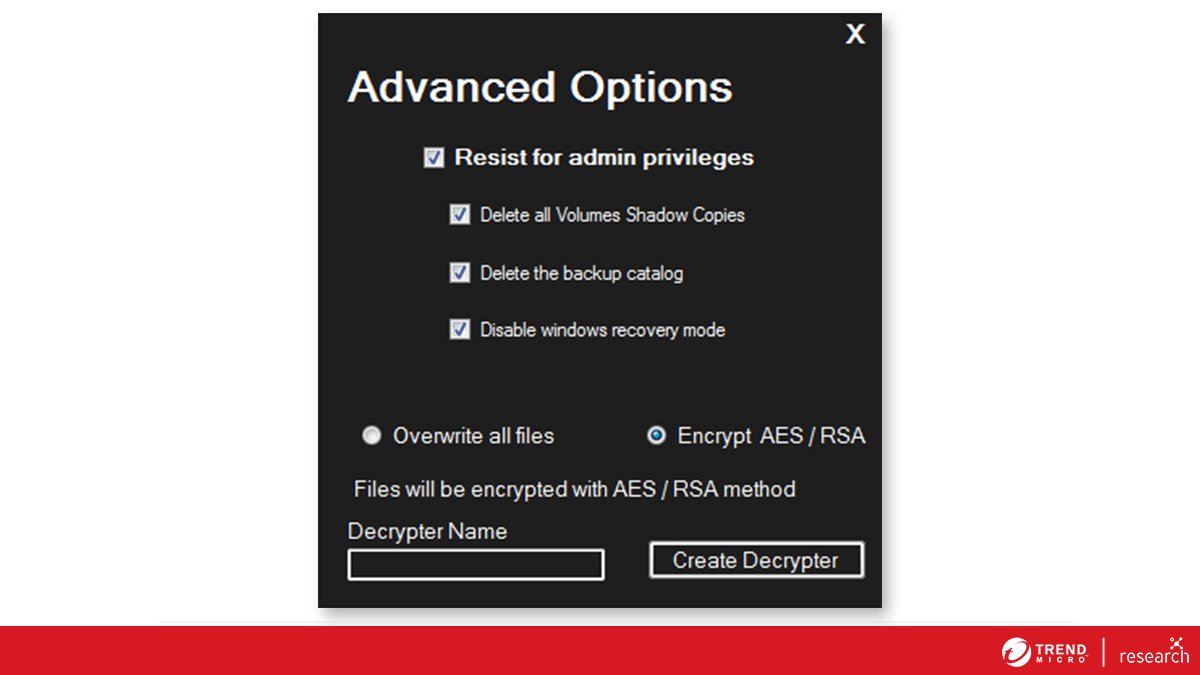
3/8: We identified the ransomware portion of the bundle as a leaked #LockBit Black payload, which seems to be from a group adopting the moniker "Flamingo.” Interestingly, the group demands a relatively modest ransom of US $90. 

4/8: The #ransomware payload is downloaded from an IP address (hxxp://5.255.107.172/forum/images/159[.]exe) that’s connected to other malware families such as Lumma Stealer, an information stealer that is delivered via SmokeLoader.
5/8: Given this connection, it’s possible that the #Rhadamanthys sample we analyzed was also delivered via SmokeLoader.
6/8: The threat actors added a combination of an information stealer and a #LockBit ransomware variant in a single #Rhadamanthys bundle, possibly indicating the continued evolution of the malware.
7/8: Access to the leaked #LockBit build has reduced the required skill level for potential threat actors to enter the field, leading to instances where individual attackers are able to employ #ransomware typically designed for larger-scale attacks against ordinary users.
8/8: Please refer to the following document for the list of indicators of compromise: documents.trendmicro.com/assets/txt/ioc…


• • •
Missing some Tweet in this thread? You can try to
force a refresh

 Read on Twitter
Read on Twitter