1/ How Lazarus Group laundered $200M from 25+ crypto hacks to fiat from 2020 - 2023
zachxbt.mirror.xyz/B0-UJtxN41cJhp…
zachxbt.mirror.xyz/B0-UJtxN41cJhp…
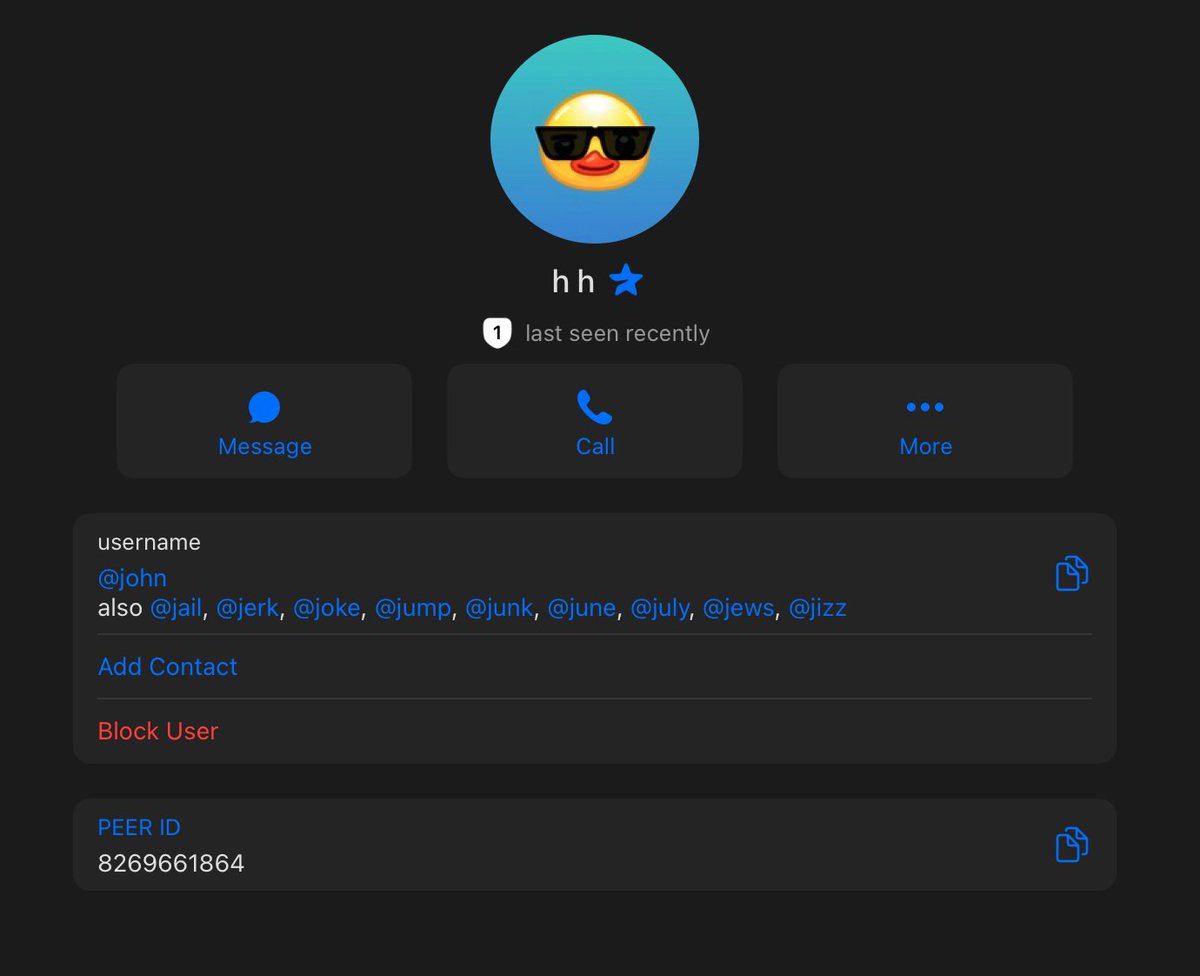
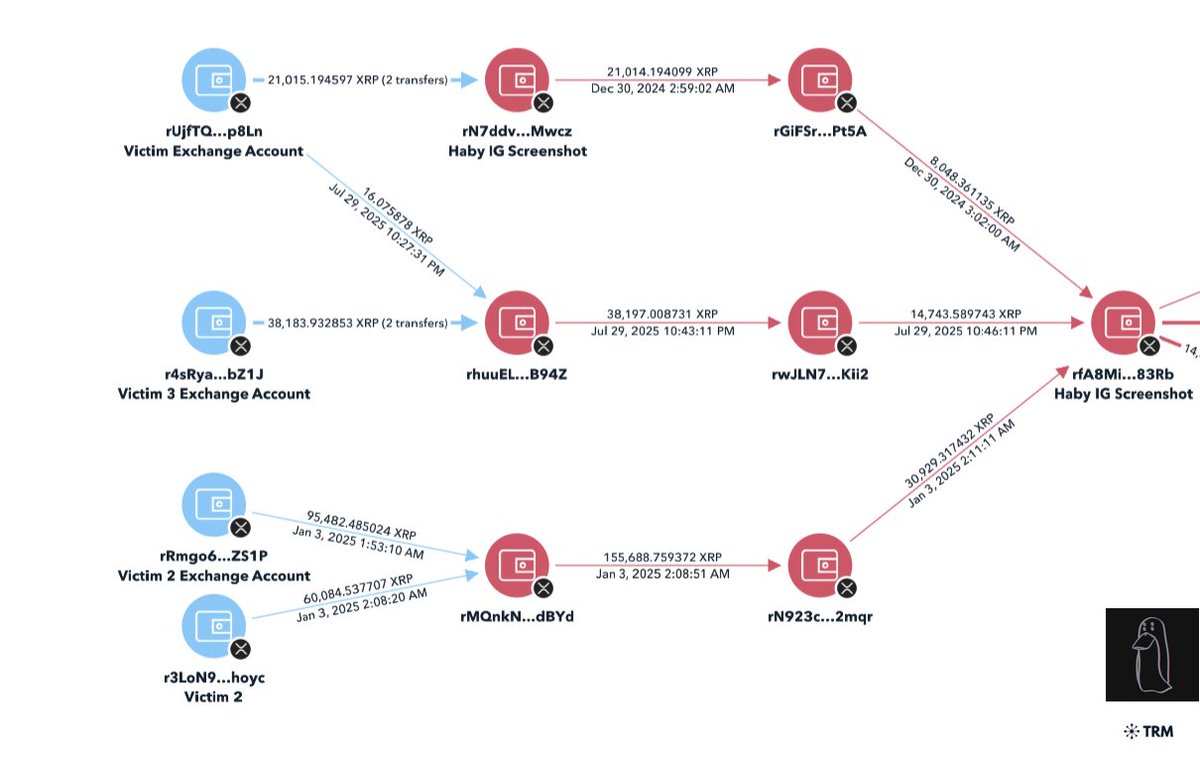
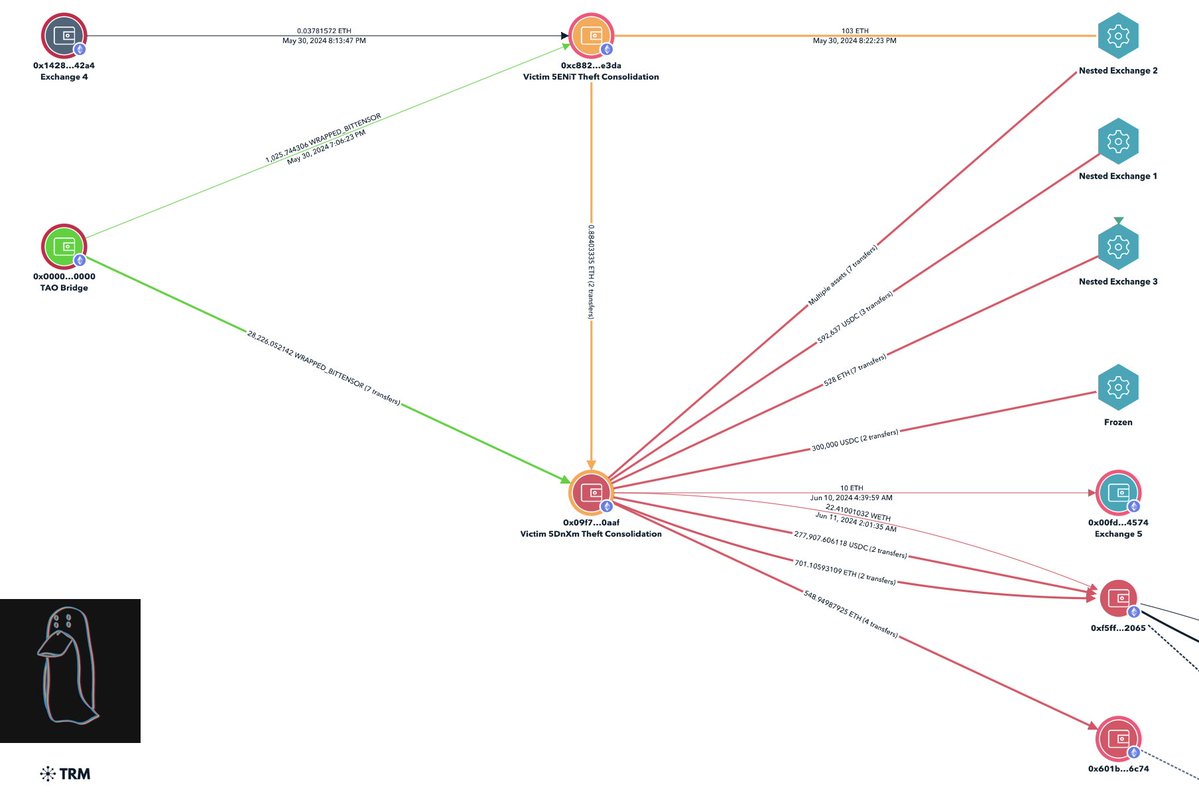
2/ Traced 25+ connected hacks across multiple blockchains and through mixers to centralized exchanges.



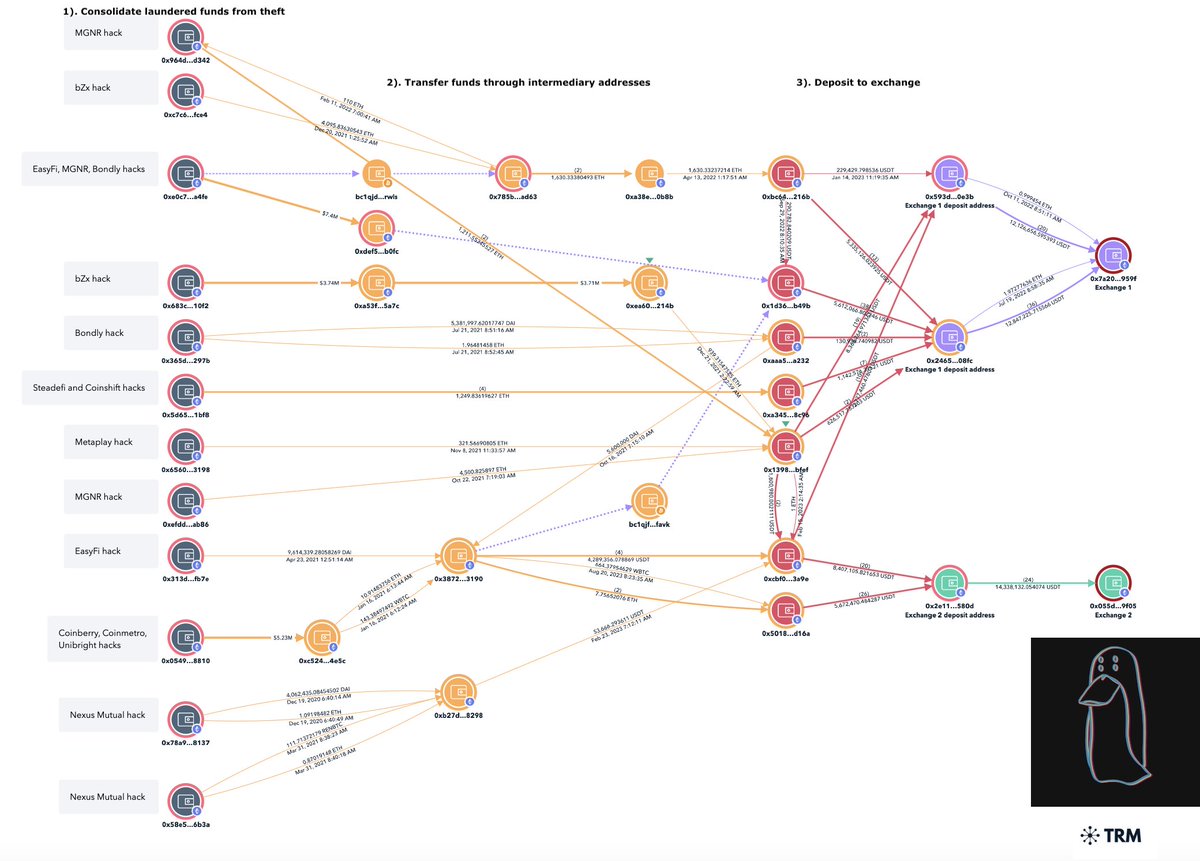
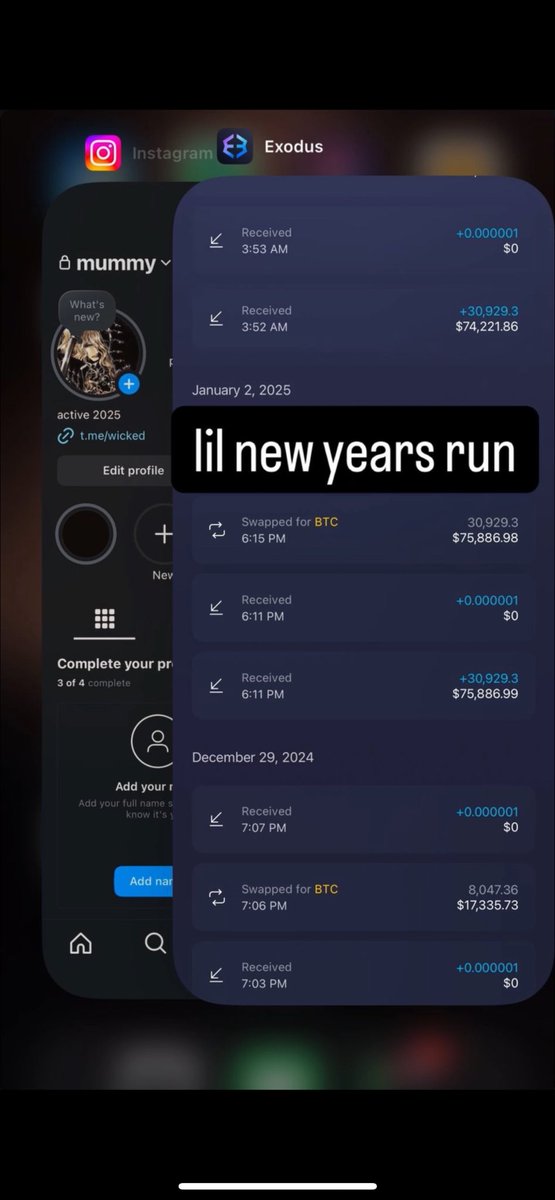
3/ Identified accounts at Noones and Paxful (P2P marketplaces) that received funds from the hacks and were used to convert crypto to fiat.


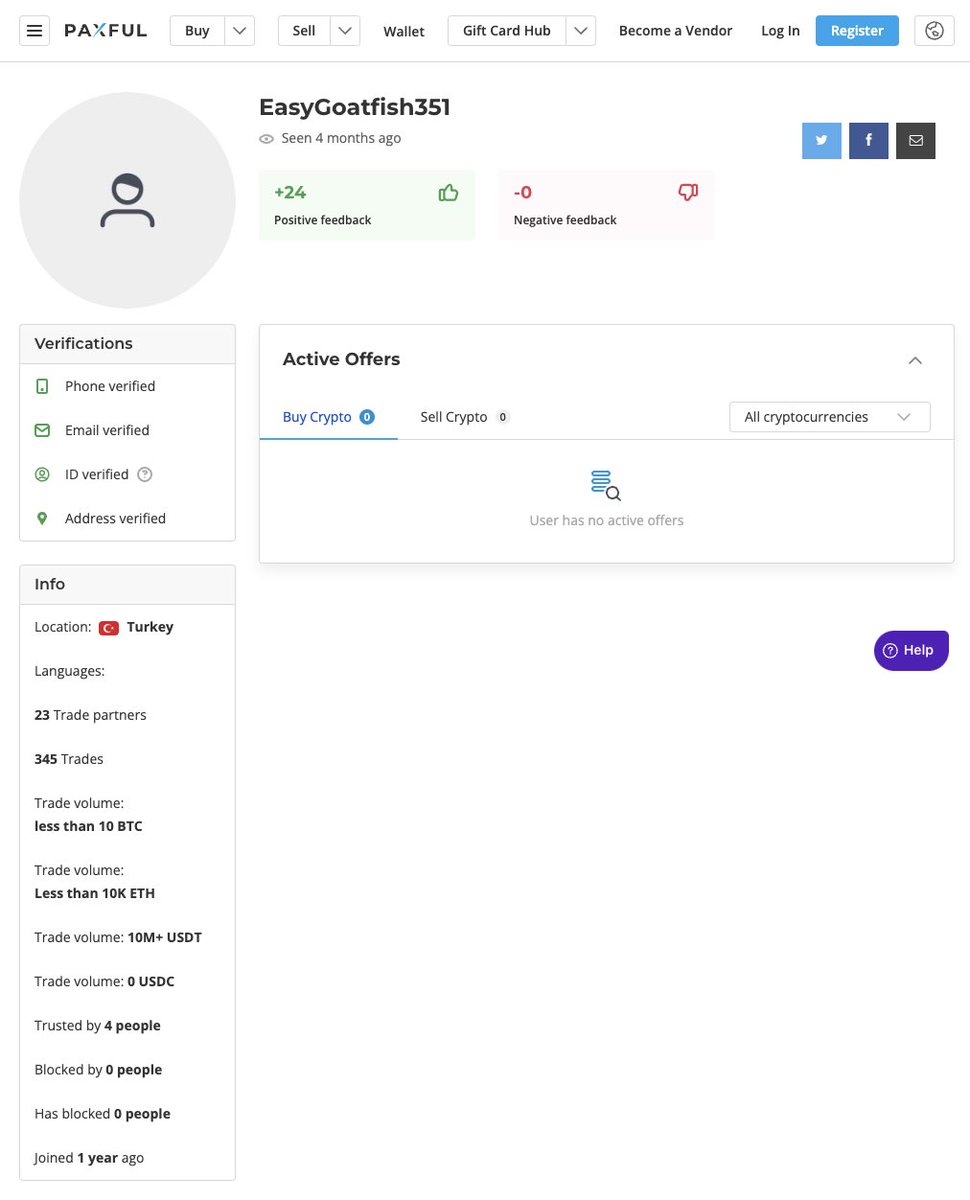
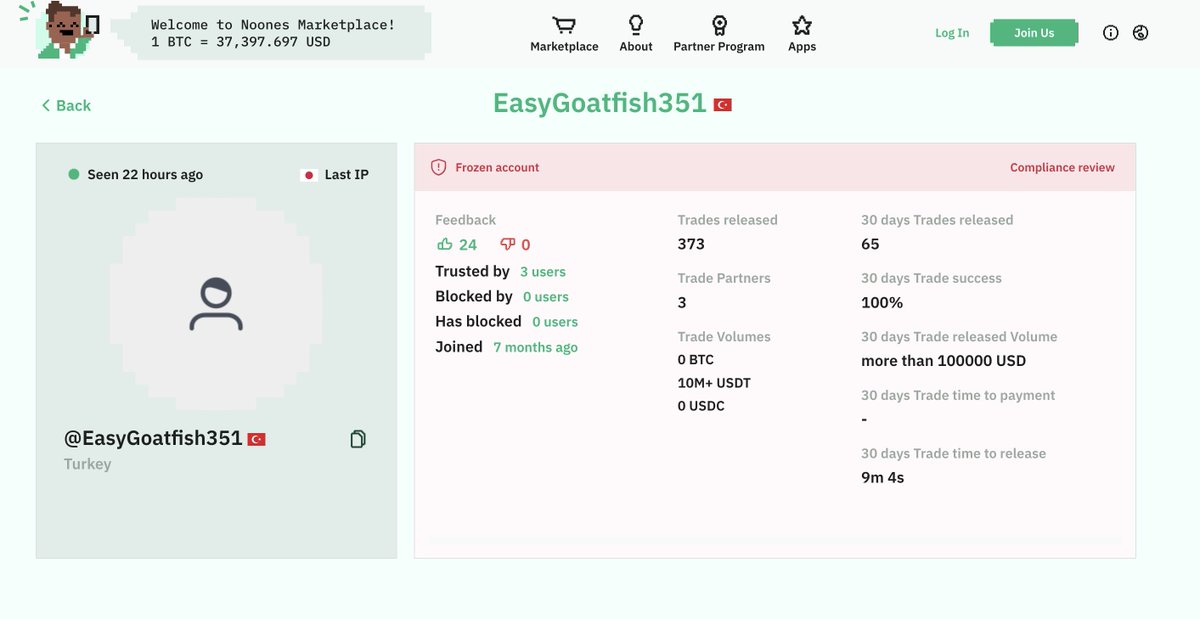
4/ 374K USDT was frozen in November 2023 and an undisclosed amount was frozen at centralized exchanges in Q4 2023.
An additional $3.4M was frozen by 3 of 4 stablecoin issuers sitting in a group of addresses.
This post will be updated once the 4th follows suit.
An additional $3.4M was frozen by 3 of 4 stablecoin issuers sitting in a group of addresses.
This post will be updated once the 4th follows suit.
5/ Link to the free Zora mint to own a digital collectible of this 15 month long investigation.
zora.co/collect/base:0…
zora.co/collect/base:0…
6/ Thousands of people in the space have been impacted directly and indirectly by Lazarus Group attacks and it seems that number will only continue to increase.
This investigation would not have been possible without the contributions of:
@tayvano_ from @MetaMask
@symbiotic_bnb from @binance
@bax1337 from 5IS
@NickCarlsen1 from @trmlabs
This investigation would not have been possible without the contributions of:
@tayvano_ from @MetaMask
@symbiotic_bnb from @binance
@bax1337 from 5IS
@NickCarlsen1 from @trmlabs
Update: As of today all four stablecoin issuers (Paxos, Tether, Techteryx, Circle) have now blacklisted the two addresses below with $4.96M from Lazarus Group.
0x36f2D3871edd59d5C06DB8F0b12bE928d5922A70
0x12ED7f6ed0491678764c2b222A58452926E44DB6
Another $1.65M is frozen at various exchanges bringing the total frozen from my investigation to $6.98M.
0x36f2D3871edd59d5C06DB8F0b12bE928d5922A70
0x12ED7f6ed0491678764c2b222A58452926E44DB6
Another $1.65M is frozen at various exchanges bringing the total frozen from my investigation to $6.98M.

• • •
Missing some Tweet in this thread? You can try to
force a refresh