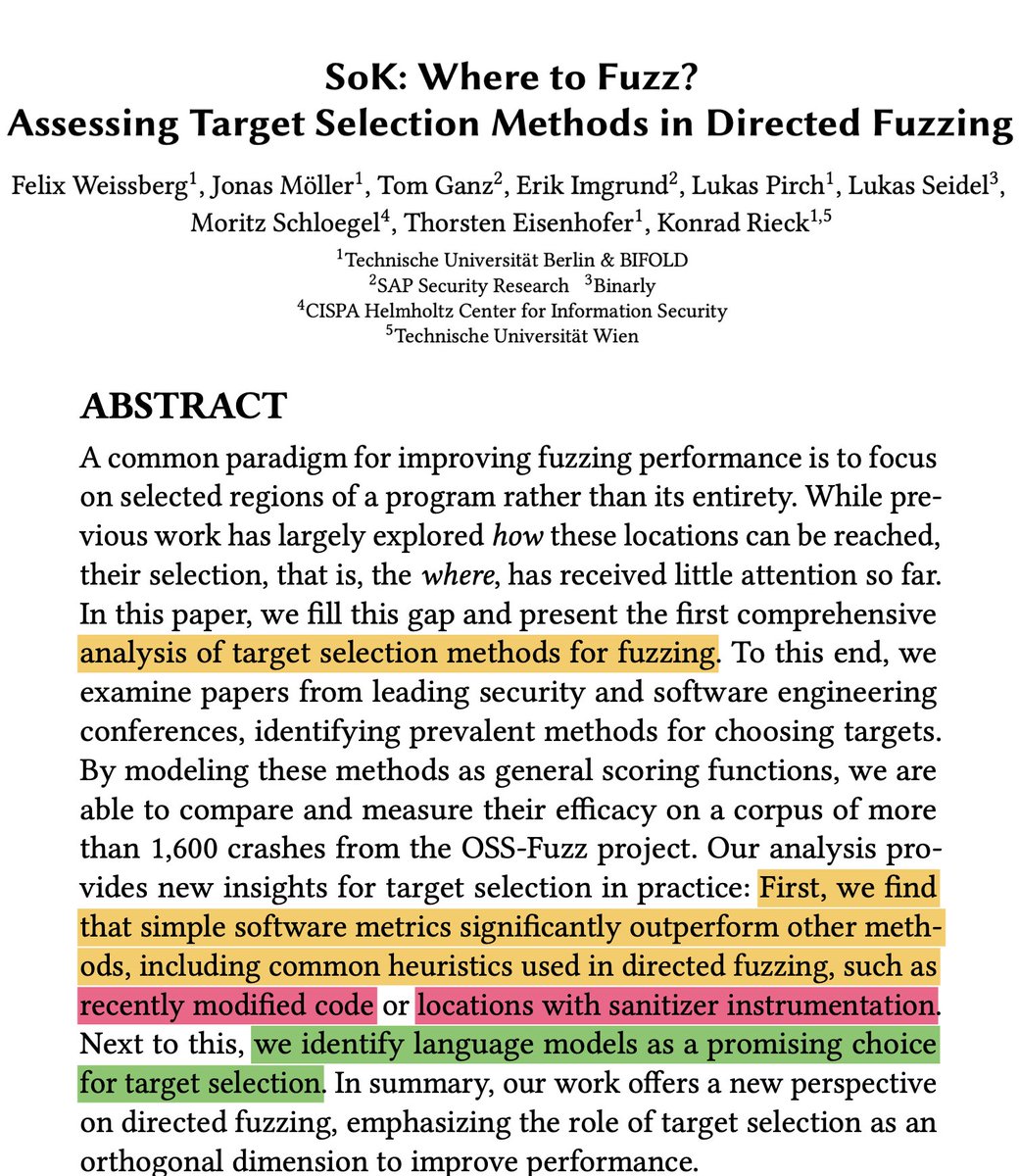
Recently modified code and sanitizer instrumentation seem to be among the most effective heuristics for target selection in directed #fuzzing according to this recent SoK by Weissberg et al. LLMs show much promise for target selection, too.
📝 mlsec.org/docs/2024c-asi…

📝 mlsec.org/docs/2024c-asi…
More info about those two heuristics:
🦠 Sanitizer-guided Greybox Fuzzing:
♻️ Regression Greybox Fuzzing: usenix.org/system/files/s…
mboehme.github.io/paper/CCS21.pdf
🦠 Sanitizer-guided Greybox Fuzzing:
♻️ Regression Greybox Fuzzing: usenix.org/system/files/s…
mboehme.github.io/paper/CCS21.pdf
But in an interesting twist, the authors find that choosing functions by their complexity might be even better at retrieving functions that contained vulnerabilities in the past.
Now, this analysis is hypothetical and w.r.t. the discovery of vulnerabilities across the *entire history* of a repository. Since the objective of a directed fuzzer is to find (unknown) vulns in the *current version*, I would be excited to see this hypothesis put to the test.
When we actually run fuzzers implementing each of these heuristics on the most recent version of a program, do we expect the cyclomatic-complexity-guided fuzzer to outperform the other heuristics?
• • •
Missing some Tweet in this thread? You can try to
force a refresh







