For those who are confused and need additional context.
Earlier today Arkham announced a $150K bounty for the identity of the DJT creator
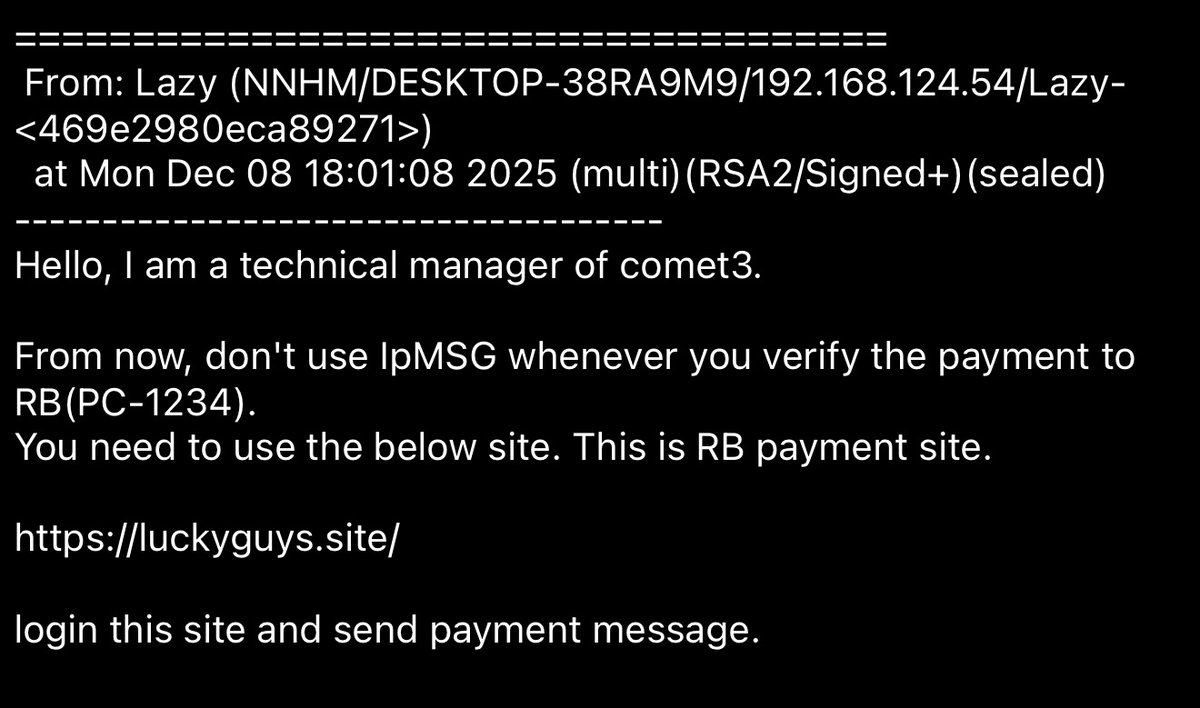
11:49 pm UTC I reply to Arkham saying I submitted for the bounty
11:57 pm UTC Martin Shkreli panic DM’s me
12:27 am UTC Martin Shkreli creates a spaces and announces he is the creator of DJT


Earlier today Arkham announced a $150K bounty for the identity of the DJT creator
11:49 pm UTC I reply to Arkham saying I submitted for the bounty
11:57 pm UTC Martin Shkreli panic DM’s me
12:27 am UTC Martin Shkreli creates a spaces and announces he is the creator of DJT



One of the large DJT insiders verso.sol dumping $832K worth of DJT and then depositing USDC to CEX ~1 hr ago
Coincidentally also a large holder on Martin’s other project Shoggoth
5cPzLzLQjt2oc8X6rGannrh7HmVJNAMFJKq21DdZRuHP



Coincidentally also a large holder on Martin’s other project Shoggoth
5cPzLzLQjt2oc8X6rGannrh7HmVJNAMFJKq21DdZRuHP
https://twitter.com/zachxbt/status/1803231125734826382



Who else was potentially involved with DJT?
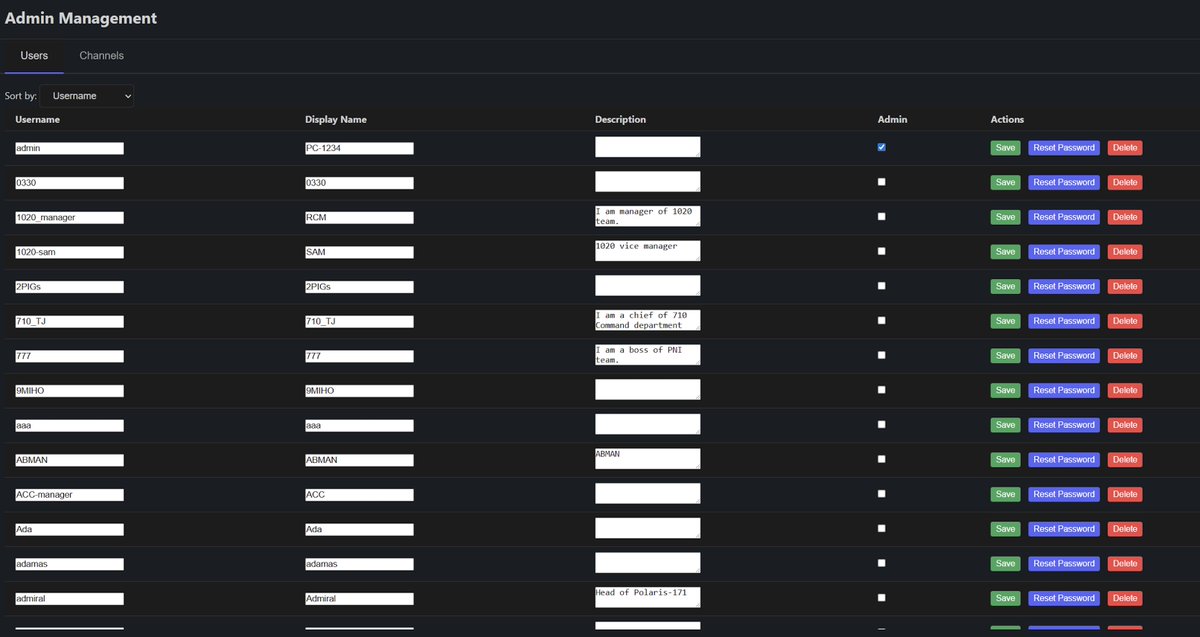
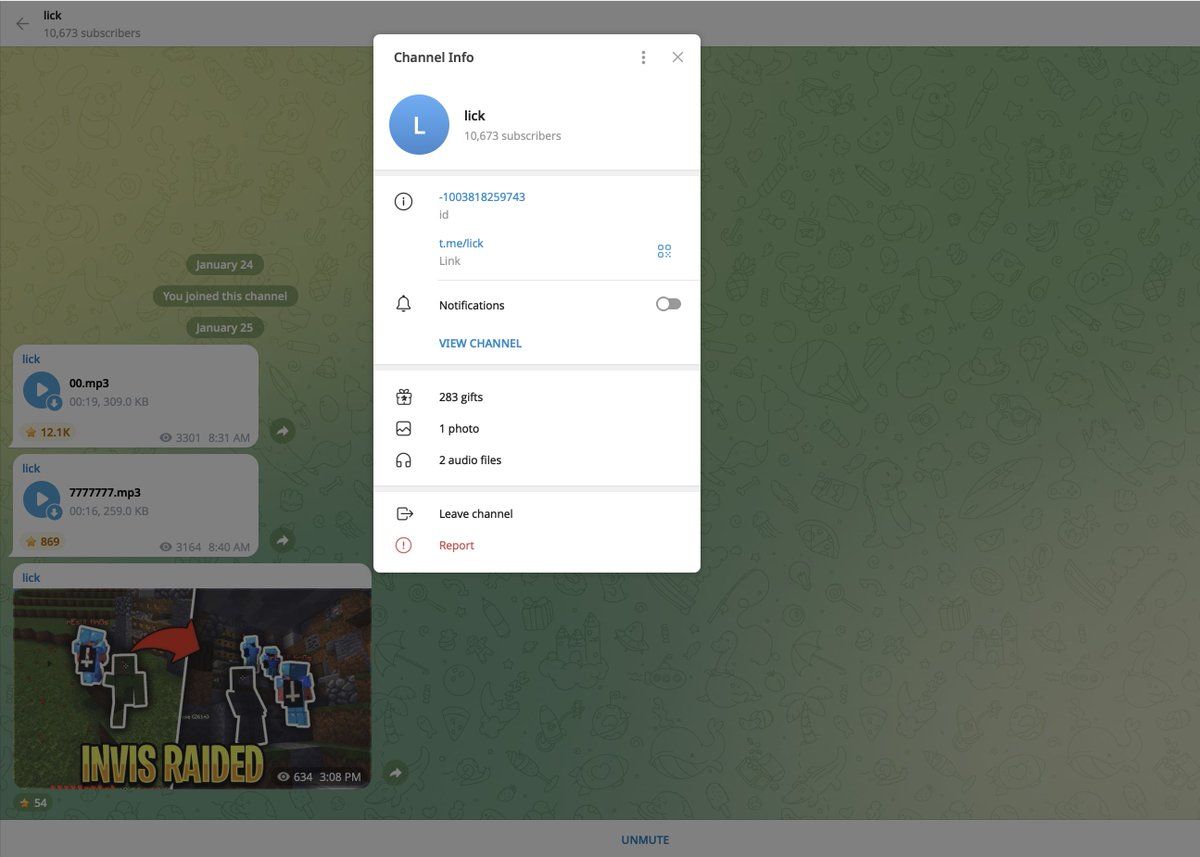
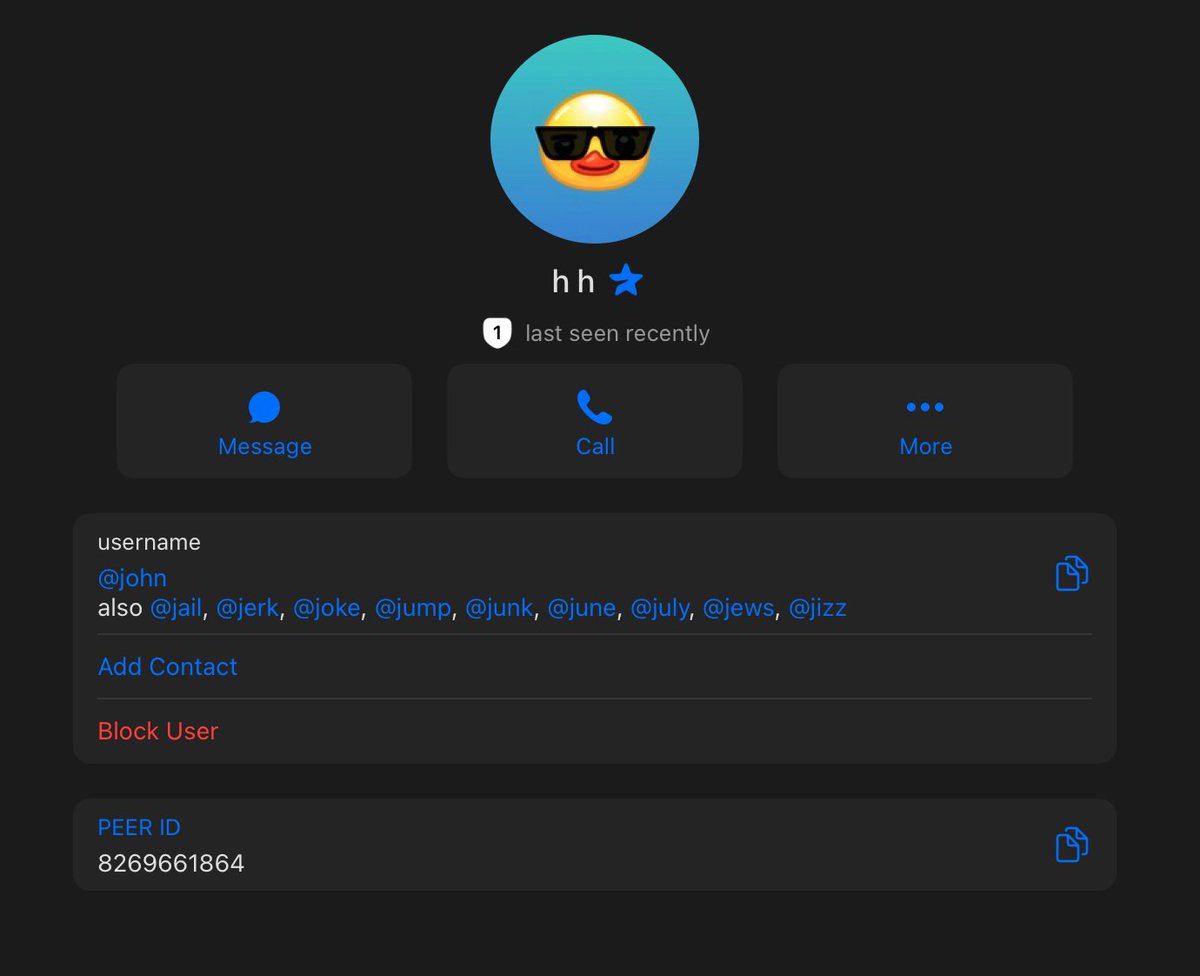
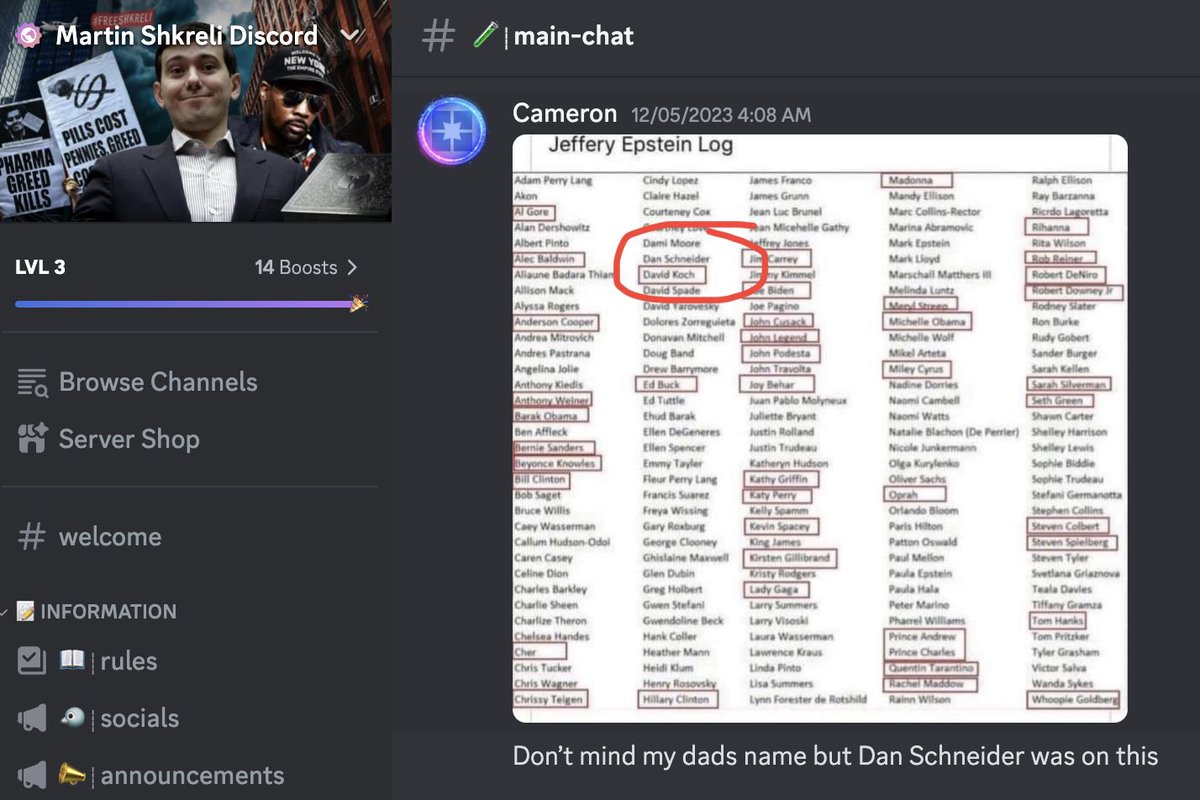
An account named CWR was the admin of the Telegram group for the DJT token.
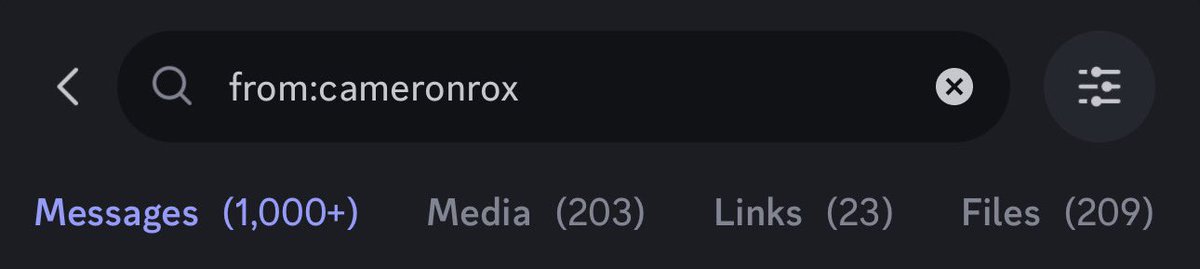
CWR is also very active in Martin Shkrehli’s public Discord server with 1K+ messages.
CWR’s Discord username is ‘cameronrox’ and refers to his alleged real name Cameron Roxborough multiple times.
He boasts about going to school with Barron Trump in multiple messages in the main-chat channel.
Are they actually close friends or is he larping? That part remains unclear.
Last night CWR left both the Telegram group and Discord server. Luckily at the time of this post his messages remain in the Discord server.
Discord ID: 294231685665521664



An account named CWR was the admin of the Telegram group for the DJT token.
CWR is also very active in Martin Shkrehli’s public Discord server with 1K+ messages.
CWR’s Discord username is ‘cameronrox’ and refers to his alleged real name Cameron Roxborough multiple times.
He boasts about going to school with Barron Trump in multiple messages in the main-chat channel.
Are they actually close friends or is he larping? That part remains unclear.
Last night CWR left both the Telegram group and Discord server. Luckily at the time of this post his messages remain in the Discord server.
Discord ID: 294231685665521664



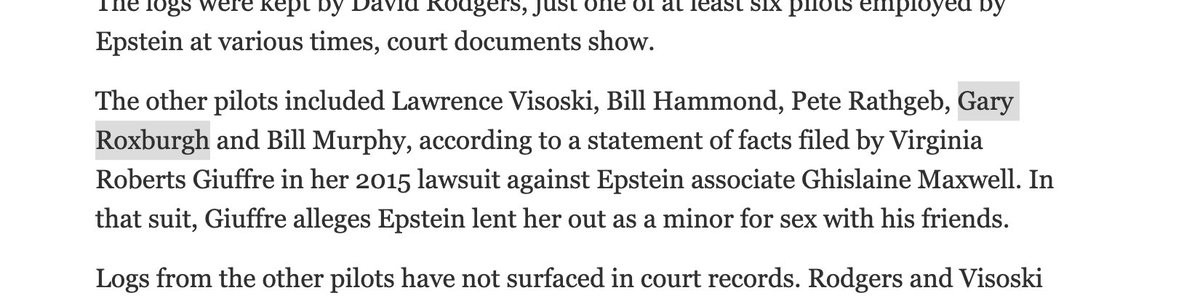
Funny enough CWR flexes how his dad was supposedly the pilot for Epstein and was named in the flight logs.




• • •
Missing some Tweet in this thread? You can try to
force a refresh