🚨 BREAKING: The UK Just Ordered Apple to Kill Encryption for 2 Billion People—And They Can’t Even Talk About It 🚨
A global privacy nightmare is unfolding.
The UK government secretly ordered Apple to backdoor encrypted iCloud storage worldwide—but Apple is legally forbidden from revealing this order, or they face criminal charges.
This affects 2 BILLION USERS.
Here’s the full story & why it’s part of a much bigger power grab. 🧵👇
A global privacy nightmare is unfolding.
The UK government secretly ordered Apple to backdoor encrypted iCloud storage worldwide—but Apple is legally forbidden from revealing this order, or they face criminal charges.
This affects 2 BILLION USERS.
Here’s the full story & why it’s part of a much bigger power grab. 🧵👇

@threadreaderapp unroll please
My X account was hacked right after Elon shared this article. Here is the full thread they did not want you to read: threadreaderapp.com/thread/1888287…
My account was hacked after Elon shared this article. Fortunately Threadreader preserved the entire thread: threadreaderapp.com/thread/1888287…
Below are the missing tweets:
1) 1/ Under the UK’s Investigatory Powers Act (IPA) 2016, Apple was served a Technical Capability Notice (TCN)—forcing them to create a backdoor for encrypted iCloud data.
This is not limited to UK users. It applies worldwide, meaning your private files are at risk, no matter where you live.
🔗@macworld report: macworld.com/article/260251…
Below are the missing tweets:
1) 1/ Under the UK’s Investigatory Powers Act (IPA) 2016, Apple was served a Technical Capability Notice (TCN)—forcing them to create a backdoor for encrypted iCloud data.
This is not limited to UK users. It applies worldwide, meaning your private files are at risk, no matter where you live.
🔗@macworld report: macworld.com/article/260251…
2) 2/ Apple is legally forbidden from revealing this order.
If Apple even acknowledges that the UK issued this demand, they could face criminal charges.
This is a secret government order with global consequences.
If Apple even acknowledges that the UK issued this demand, they could face criminal charges.
This is a secret government order with global consequences.

3/ This isn’t just about the UK (although they are leading the charge in threatening citizens in OTHER countries for violating BRITISH censorship laws!)
If Apple complies, every government in the world will demand the same access—from the US to China to authoritarian regimes.
End-to-end encryption would be effectively dead.
If Apple complies, every government in the world will demand the same access—from the US to China to authoritarian regimes.
End-to-end encryption would be effectively dead.

4/ Apple’s Choice:
🔓 Comply & weaken encryption globally
🚪 Refuse & withdraw services from the UK
WhatsApp & Signal faced similar threats last year and vowed to leave the UK rather than compromise security.
Will Apple do the same?
🚨Watch the heated discussion between Damian Collins, director of CCDH (architect of the UK Online Safety Bill), and Signal’s CEO: youtube.com/watch?v=E--bVV…
🔓 Comply & weaken encryption globally
🚪 Refuse & withdraw services from the UK
WhatsApp & Signal faced similar threats last year and vowed to leave the UK rather than compromise security.
Will Apple do the same?
🚨Watch the heated discussion between Damian Collins, director of CCDH (architect of the UK Online Safety Bill), and Signal’s CEO: youtube.com/watch?v=E--bVV…
5/ Why This Matters:
☑️Encryption protects financial data, health records, personal security (e.g. where you live or work), and private conversations.
☑️Governments always say they need backdoors for national security—but history shows they’re used for mass surveillance.
☑️Once a backdoor exists, hackers, rogue employees, and other governments WILL find it.
☑️Encryption protects financial data, health records, personal security (e.g. where you live or work), and private conversations.
☑️Governments always say they need backdoors for national security—but history shows they’re used for mass surveillance.
☑️Once a backdoor exists, hackers, rogue employees, and other governments WILL find it.
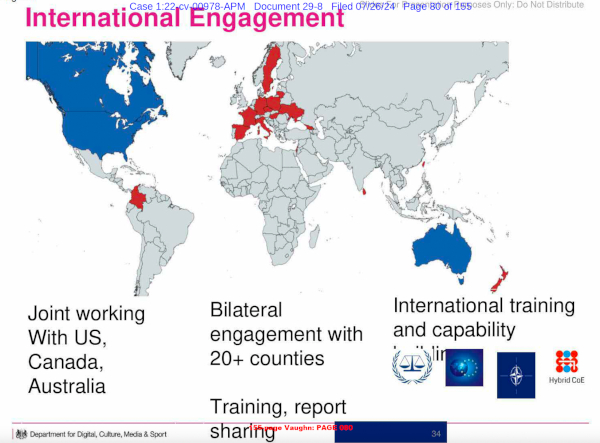
6/ The UK is trying to dominate the global surveillance & censorship landscape.
The UK is part of Five Eyes (UK, US, Canada, Australia, NZ), but notably, the US, Canada, Australia, and New Zealand have supported strong encryption to mitigate cyber threats.
Yet, the UK stands alone in its war on encryption.
The UK is part of Five Eyes (UK, US, Canada, Australia, NZ), but notably, the US, Canada, Australia, and New Zealand have supported strong encryption to mitigate cyber threats.
Yet, the UK stands alone in its war on encryption.
7/ The Free Speech Crackdown 🛑
This isn’t just about encryption—it’s about control.
Governments worldwide are criminalizing dissent and censoring free speech, using tech companies as their enforcement arms.
🔗 GreenMedInfo Report: greenmedinfo.com/content/breaki…
This isn’t just about encryption—it’s about control.
Governments worldwide are criminalizing dissent and censoring free speech, using tech companies as their enforcement arms.
🔗 GreenMedInfo Report: greenmedinfo.com/content/breaki…
8/ This ties into the UK’s broader, GLOBALLY ORCHESTATED censorship agenda:
⚠️ The Online Safety Bill criminalizes encrypted messaging & forces platforms to scan private messages.
⚠️ The Digital Services Act (EU) gives governments the power to shut down online content they don’t like.
⚠️ Leaked US-UK documents show direct coordination between UK intelligence & the Biden administration to censor online speech:
🚨Learn more about the global plot to adjudicate and criminalize free speech involving bilateral engagement with 20+ countries, and coordination with NATO and the G7: greenmedinfo.com/content/americ… (@America1stLegal's CDC lawsuit revealed this plot)
⚠️ The Online Safety Bill criminalizes encrypted messaging & forces platforms to scan private messages.
⚠️ The Digital Services Act (EU) gives governments the power to shut down online content they don’t like.
⚠️ Leaked US-UK documents show direct coordination between UK intelligence & the Biden administration to censor online speech:
🚨Learn more about the global plot to adjudicate and criminalize free speech involving bilateral engagement with 20+ countries, and coordination with NATO and the G7: greenmedinfo.com/content/americ… (@America1stLegal's CDC lawsuit revealed this plot)
9/ Meet the architects of speech policing: CCDH 🕵️♂️
The Center for Countering Digital Hate (CCDH)—a UK intelligence-backed group—has been a driving force behind global censorship.
They were caught:
🔥 Running “black ops” to suppress RFK Jr.’s presidential campaign.
🔥 Leading the "Kill Musk’s Twitter" directive, trying to shut down free speech on X.
🔥 Labeling 12 private US citizens as the “Disinformation Dozen” to justify mass censorship.
🔗 Reclaim the Net Investigation: reclaimthenet.org/black-ops-how-…
The same UK group behind mass censorship also helped design the UK’s anti-encryption policies via the UK Online Safety Bill passed in 2024.
The Center for Countering Digital Hate (CCDH)—a UK intelligence-backed group—has been a driving force behind global censorship.
They were caught:
🔥 Running “black ops” to suppress RFK Jr.’s presidential campaign.
🔥 Leading the "Kill Musk’s Twitter" directive, trying to shut down free speech on X.
🔥 Labeling 12 private US citizens as the “Disinformation Dozen” to justify mass censorship.
🔗 Reclaim the Net Investigation: reclaimthenet.org/black-ops-how-…
The same UK group behind mass censorship also helped design the UK’s anti-encryption policies via the UK Online Safety Bill passed in 2024.
10/ The Pattern is Clear:
1️⃣ Governments create "safety" laws to justify surveillance.
2️⃣ They pressure tech companies to enforce censorship.
3️⃣ Once encrypted services are gone, nothing is private anymore.
This is the biggest attack on digital freedom in history.
And most recently @elonmusk and @lindayaX appear to have taken the bait by backing the Kids Online Safety Bill (KOSA) - a 'child safety' bill trojan horse for draconian censorship: sayerji.substack.com/p/alert-elon-m…
1️⃣ Governments create "safety" laws to justify surveillance.
2️⃣ They pressure tech companies to enforce censorship.
3️⃣ Once encrypted services are gone, nothing is private anymore.
This is the biggest attack on digital freedom in history.
And most recently @elonmusk and @lindayaX appear to have taken the bait by backing the Kids Online Safety Bill (KOSA) - a 'child safety' bill trojan horse for draconian censorship: sayerji.substack.com/p/alert-elon-m…
11/ What Can We Do?
🔹 Support companies that refuse to build backdoors (Signal, ProtonMail, etc.).
🔹 Push for legislation that protects encryption & free speech.
🔹 Stay informed & spread awareness—governments count on secrecy to push these policies through.
🔹 Follow and support privacy and internet freedom organizations such as: @G_W_Forum @FFO_Freedom @ReclaimTheNetHQ @standforhealth1 @ChildrensHD @brownstoneinst @anhcampaign @FreeWCH @TheNHF
🔹 Support companies that refuse to build backdoors (Signal, ProtonMail, etc.).
🔹 Push for legislation that protects encryption & free speech.
🔹 Stay informed & spread awareness—governments count on secrecy to push these policies through.
🔹 Follow and support privacy and internet freedom organizations such as: @G_W_Forum @FFO_Freedom @ReclaimTheNetHQ @standforhealth1 @ChildrensHD @brownstoneinst @anhcampaign @FreeWCH @TheNHF

12/ This is the ultimate power grab: controlling all digital communication.
If Apple caves, every other platform will be forced to follow.
📌 The UK’s Global Playbook:
🔹 A backdoor to encryption (Investigatory Powers Act).
🔹 A government-linked censorship network (CCDH).
🔹 A speech-policing framework that extends worldwide (Online Safety Bill).
This is a global effort to control what people can say, share, and store privately.
If Apple caves, every other platform will be forced to follow.
📌 The UK’s Global Playbook:
🔹 A backdoor to encryption (Investigatory Powers Act).
🔹 A government-linked censorship network (CCDH).
🔹 A speech-policing framework that extends worldwide (Online Safety Bill).
This is a global effort to control what people can say, share, and store privately.
13/ The Final Stand: Will You Comply or Resist? ⚔️🚨
They want total control—your speech, your privacy, your elections. This is the defining battle of our time. 🛑🔒
🇬🇧 UK’s war on encryption = Global censorship blueprint.
🗳️ Election meddling + speech policing = A hijacked democracy. sayerji.substack.com/p/crossfire-of…
📢 Digital freedom is human freedom.
Stand up. Speak out. Fight back. 🏴☠️🔥
🔗 LEARN MORE: greenmedinfo.com/content/kill-m…
They want total control—your speech, your privacy, your elections. This is the defining battle of our time. 🛑🔒
🇬🇧 UK’s war on encryption = Global censorship blueprint.
🗳️ Election meddling + speech policing = A hijacked democracy. sayerji.substack.com/p/crossfire-of…
📢 Digital freedom is human freedom.
Stand up. Speak out. Fight back. 🏴☠️🔥
🔗 LEARN MORE: greenmedinfo.com/content/kill-m…
More details on the leaked global plan to censor, adjudicate, and criminalize free speech: greenmedinfo.com/content/americ…
My account was hacked immediately after Elon shared the tweet. Thankfully, I recovered it before the post was fully deleted. Full thread is preserved here: threadreaderapp.com/thread/1888287…
• • •
Missing some Tweet in this thread? You can try to
force a refresh