#BotSpot: after Twitter changed its ToS, bot creators are still making new botnets. But it's a precarious existence.
medium.com/dfrlab/botspot…
medium.com/dfrlab/botspot…
Meet one short-lived botnet, with a Japanese focus. Its handles started with @kurikairiku51 and went up sequentially to @kurikairiku100. 

Sequential handles. Identical bios. Identical tweets in identical order. Thousands of likes. Following the same number of accounts.
Bots.
Bots.

What's striking is how fast these accounts were set up. Six in seven minutes, on March 24 (UK time). 

Then the main burst: 44 in just under an hour, on March 25. (Image of the first and last in the sequence.)
A rate of almost one a minute: either that's automated, or someone's employing a team to do this.
A rate of almost one a minute: either that's automated, or someone's employing a team to do this.

They were hyperactive while they lasted. This one posted 2,574 likes in under five days, for an average of about 588 a day.
Across the network, we're talking on the order of 100,000 likes in five days.
Across the network, we're talking on the order of 100,000 likes in five days.

Numbers 101 onwards don't exist; the numbers up to 50 had been suspended earlier. (The "suspended" image here is from @kurikairiku49).
So this looks like a botnet that was created in a batch of 50, probably to avoid tripping Twitter's automated detectors.
So this looks like a botnet that was created in a batch of 50, probably to avoid tripping Twitter's automated detectors.
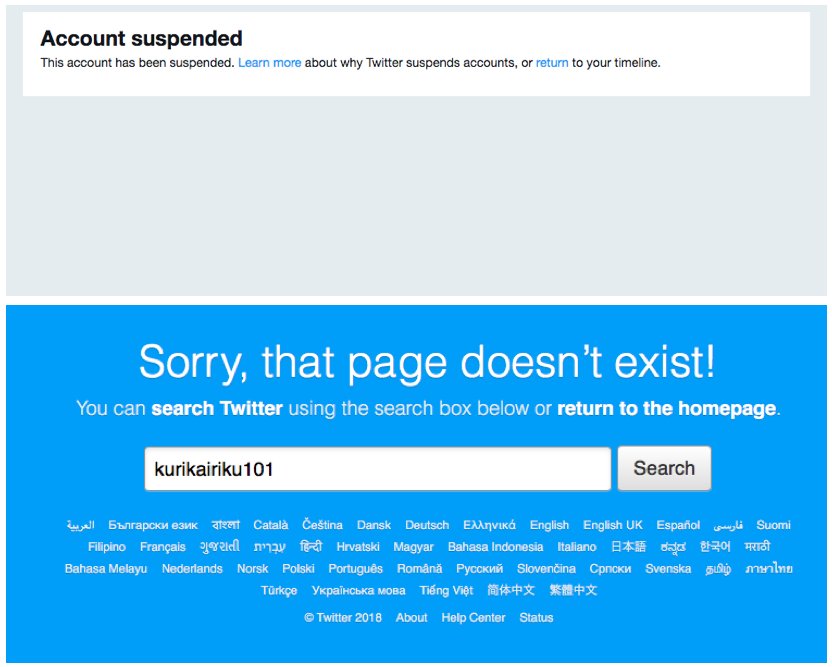
Twitter shut it down yesterday. That shows their detectors are working.
But someone managed to set them up in the first place, fast, blatantly (those handles), and undetected. That shows there's still a window open, even if it's getting narrower. / Thread ends.
But someone managed to set them up in the first place, fast, blatantly (those handles), and undetected. That shows there's still a window open, even if it's getting narrower. / Thread ends.

• • •
Missing some Tweet in this thread? You can try to
force a refresh