
Cyber_Security_Re-searcher || Ai Re-searcher || AI-ML || Malware Analysis II Pwn || 0SINT || Project AI-StrikeSec || 0ld Accounts Suspended @0xSojalSec ||
How to get URL link on X (Twitter) App

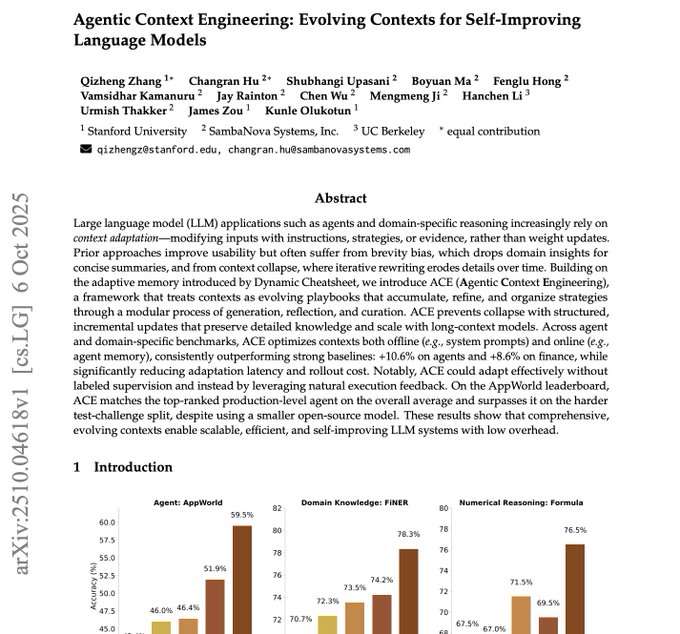
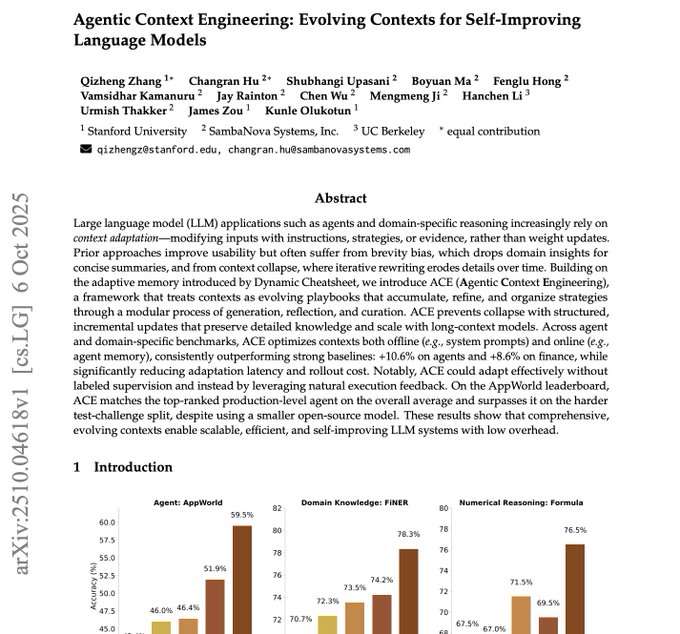 How ACE works :
How ACE works : 
https://twitter.com/sinwindie/status/1251320697370095617?s=20)
 - GraphQL in 40 Minutes:
- GraphQL in 40 Minutes: 
 1. Cyber Work
1. Cyber Work