
Your weekly go-to cybersecurity newsletter, curated and commented on by our senior analysts.
Got tips? Signal: IntCyberDigest.20
How to get URL link on X (Twitter) App

 Go to iOS Settings → Notifications → [App Name] → Show Previews and set it to Never.
Go to iOS Settings → Notifications → [App Name] → Show Previews and set it to Never. 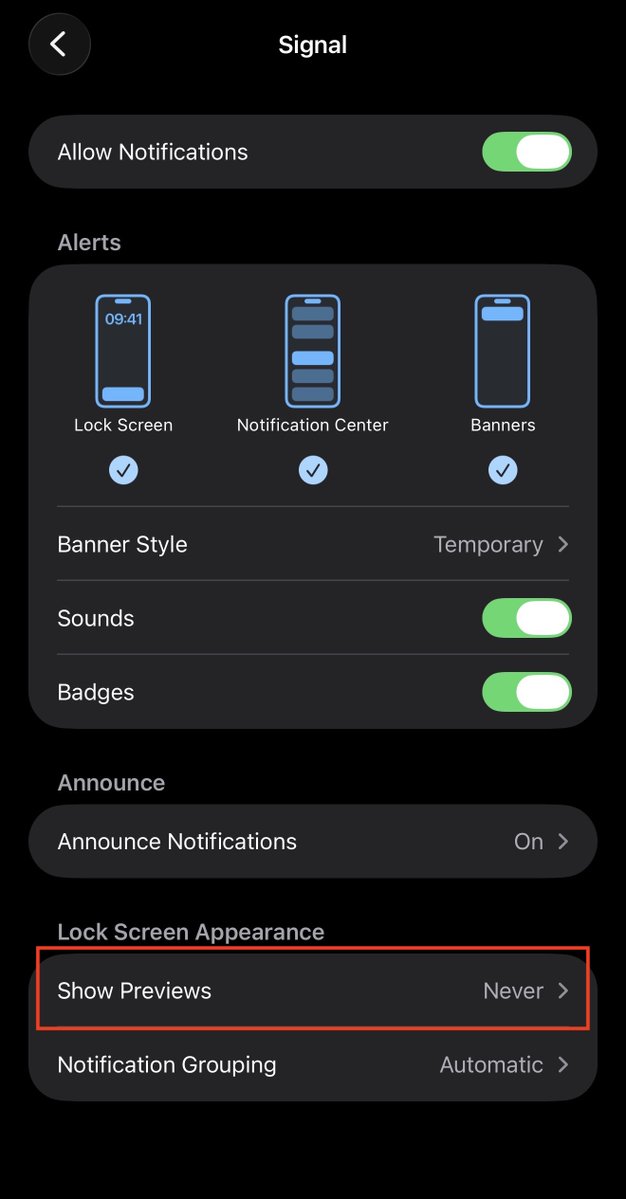


 Anodot is a shady company — we've heard they haven't replied to any emails journalists have sent. Even their AI assistant looks like the Unabomber on crack...
Anodot is a shady company — we've heard they haven't replied to any emails journalists have sent. Even their AI assistant looks like the Unabomber on crack... 


 Sam Altman hearing this right now. 😂
Sam Altman hearing this right now. 😂 


 Meta's Multi-Channel Influence Network
Meta's Multi-Channel Influence Network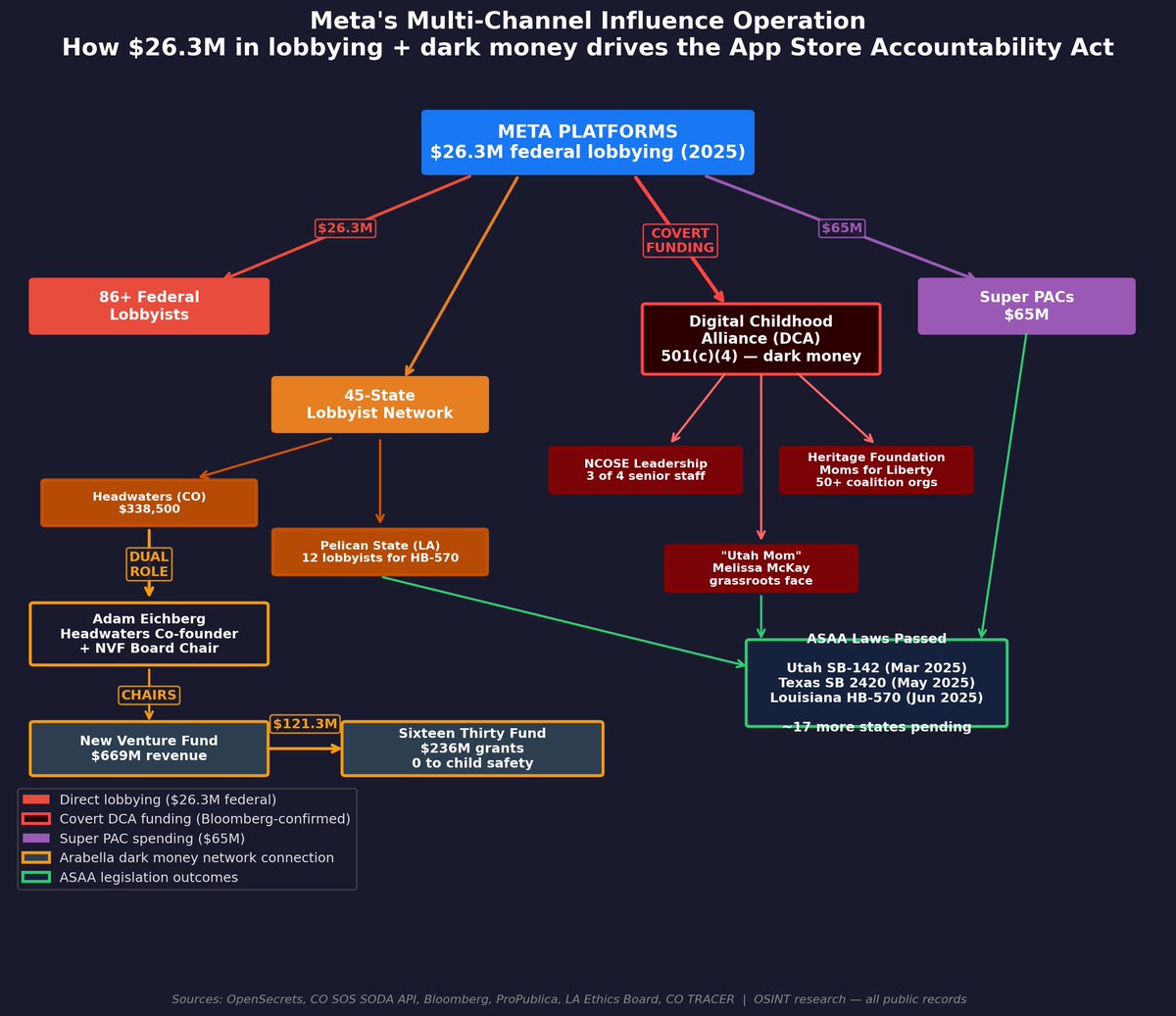


 Here's a tree of the repo:
Here's a tree of the repo: 
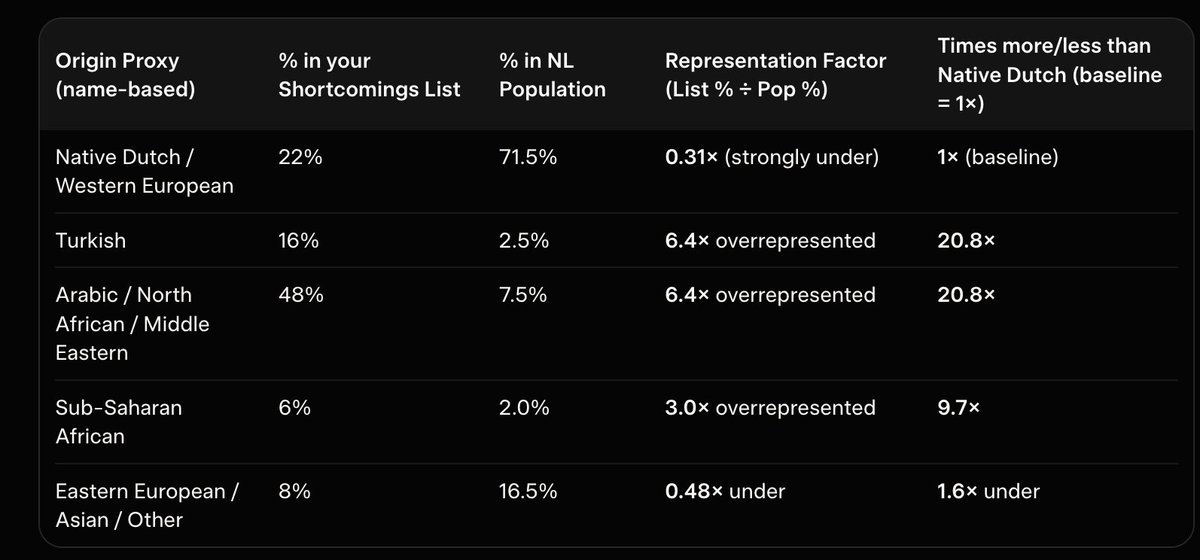
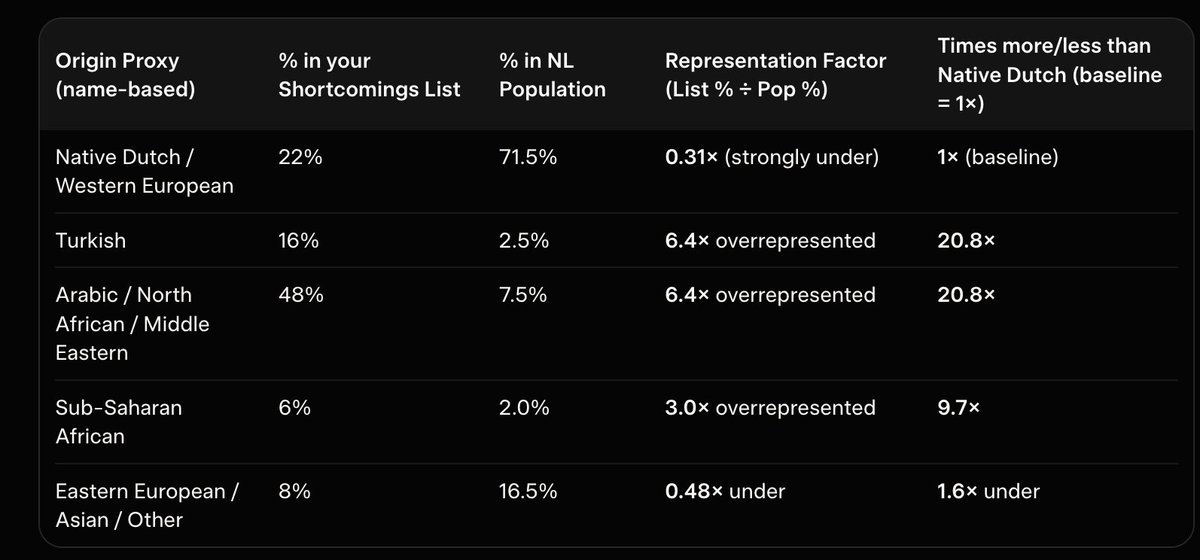
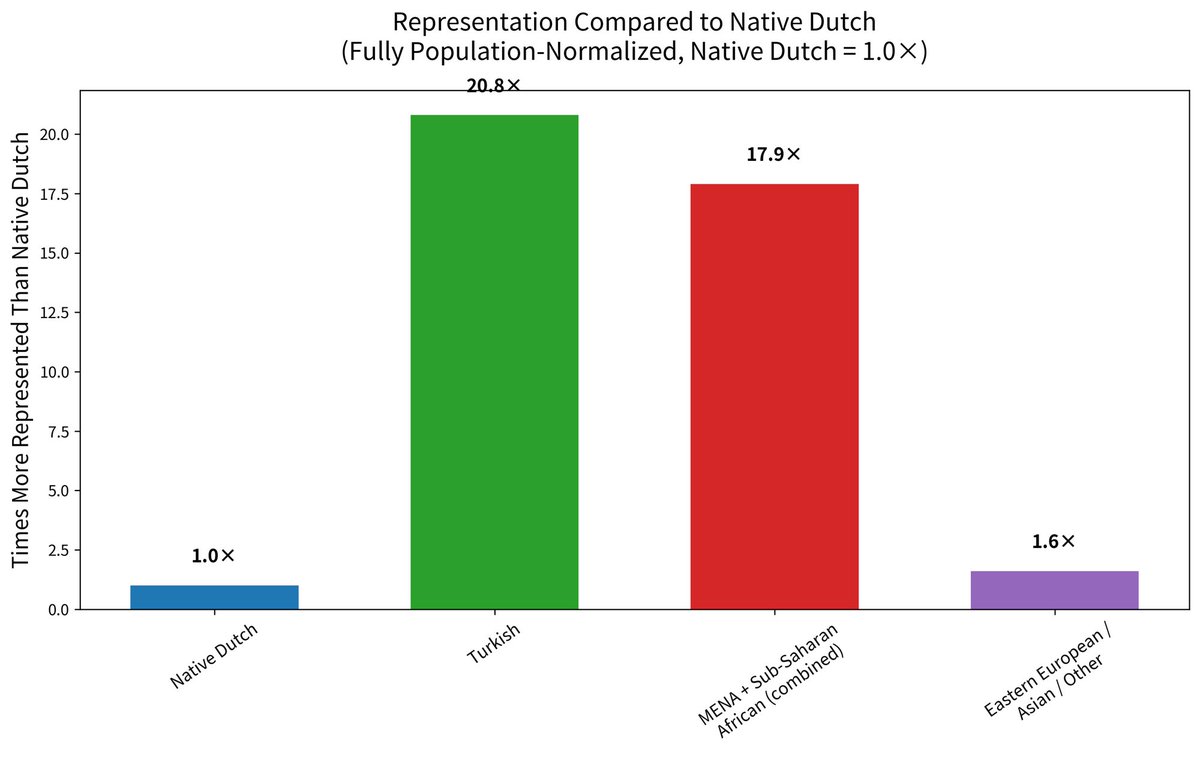
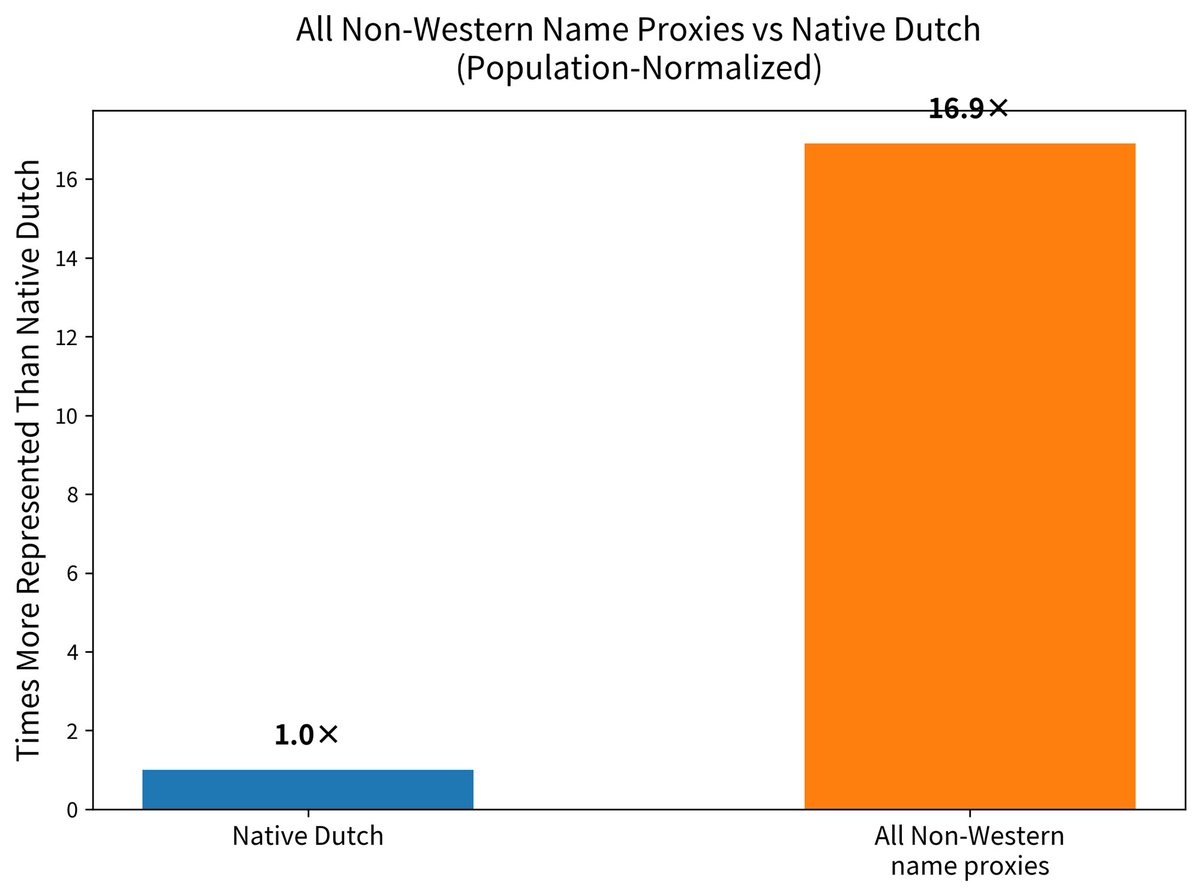 These are absolute values:
These are absolute values: 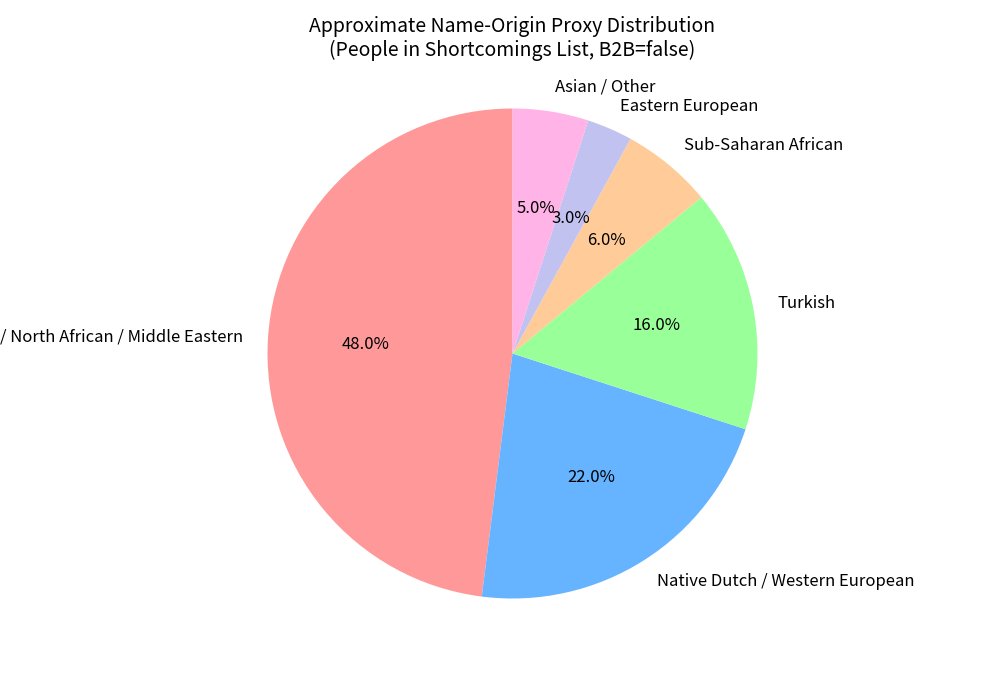


 Persona maintains a public list of subprocessors aka third-party companies that process your personal data on their behalf. Here's the full list:
Persona maintains a public list of subprocessors aka third-party companies that process your personal data on their behalf. Here's the full list: 


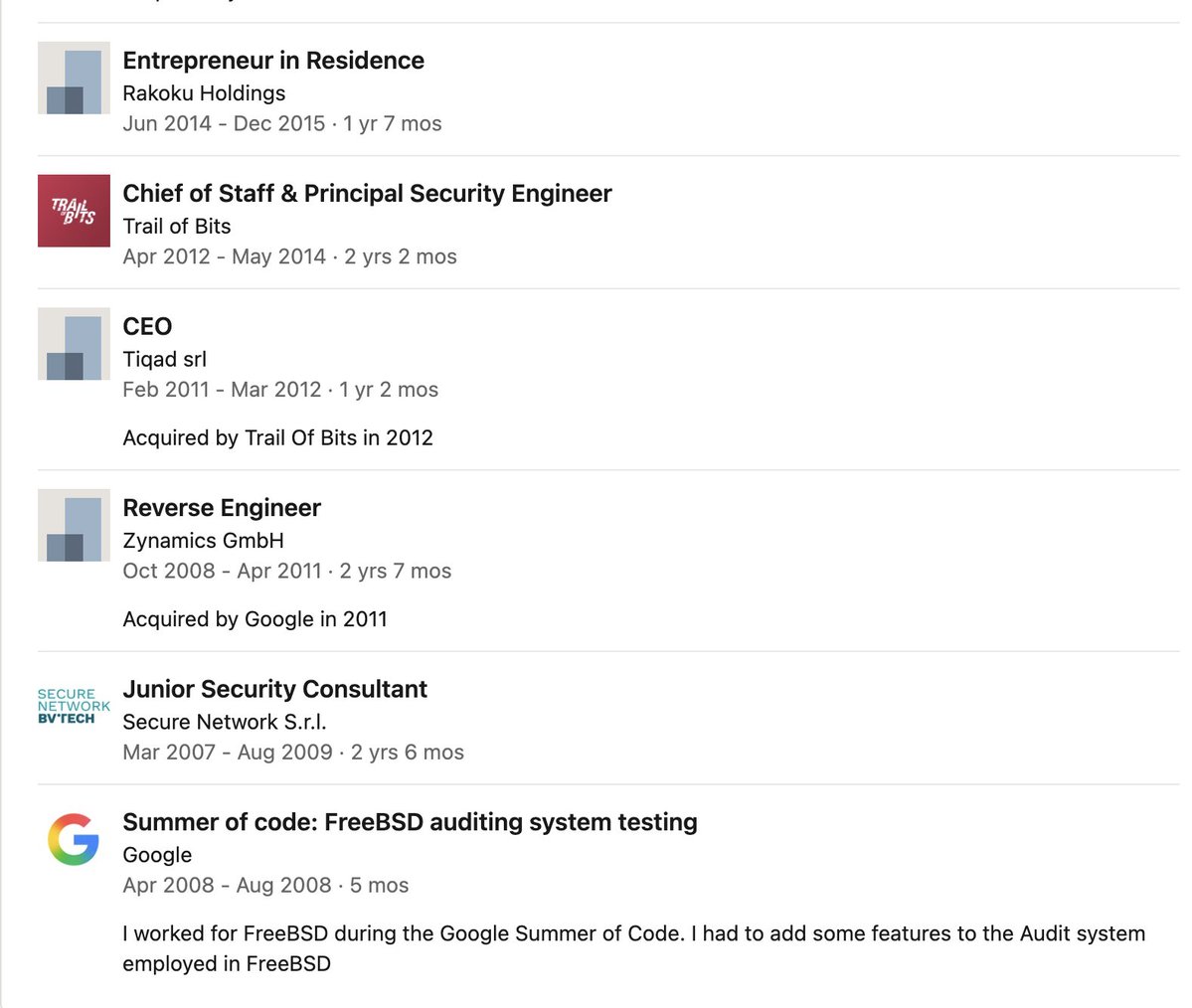
 His LinkedIn shows his company "Iperlane" was sold to CrowdStrike and that he was also a board member of Black Hat, hence he invited Jeffrey to join him at Black Hat.
His LinkedIn shows his company "Iperlane" was sold to CrowdStrike and that he was also a board member of Black Hat, hence he invited Jeffrey to join him at Black Hat.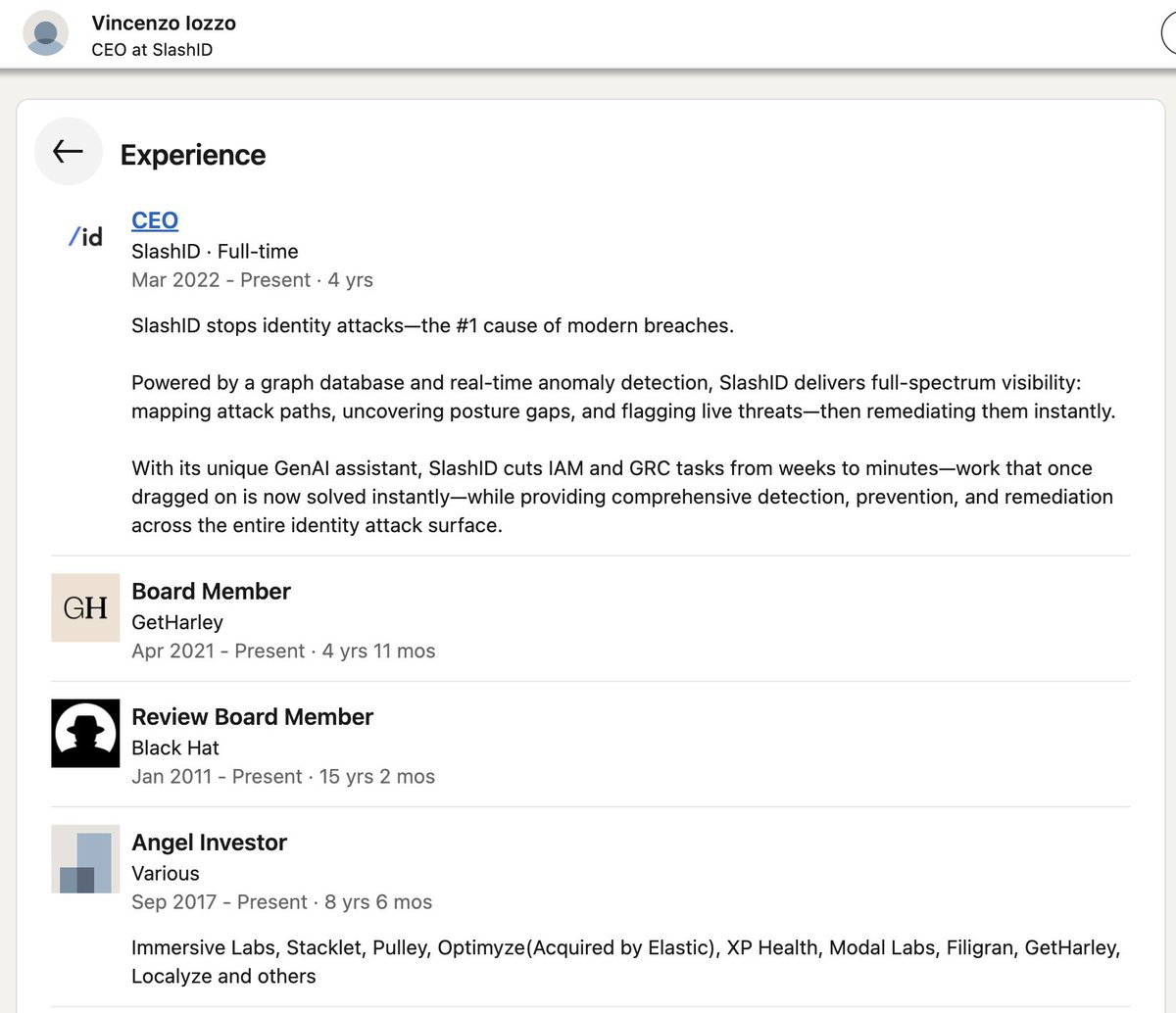



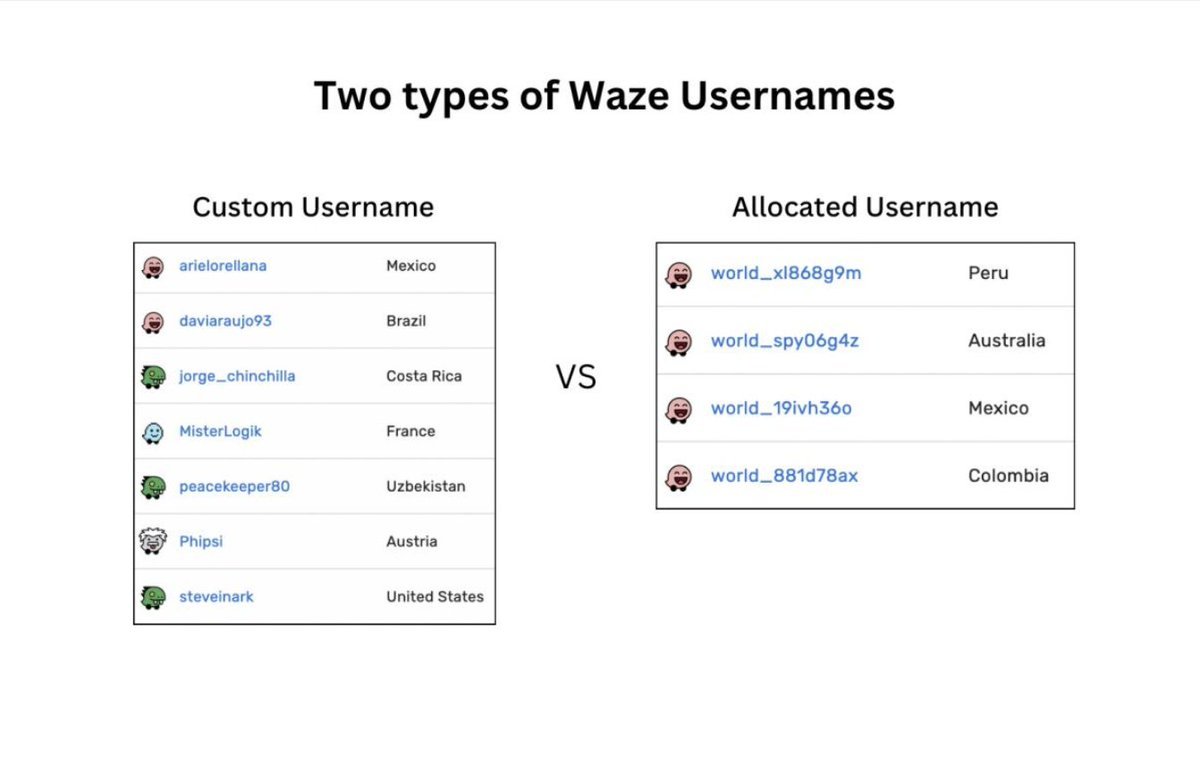
 He was able to deanonymize custom usernames by using OSINT tools.
He was able to deanonymize custom usernames by using OSINT tools.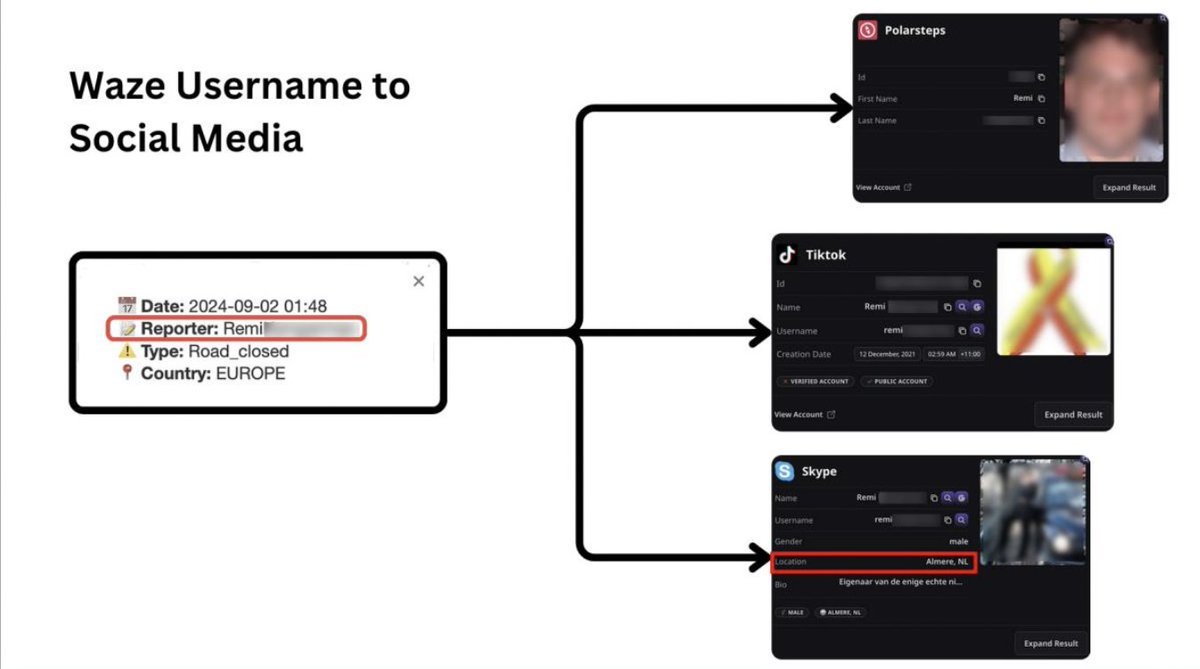

 One year later, the suspect is summoned to appear at the police station in Antwerp, Belgium, on suspicion of premeditated murder.
One year later, the suspect is summoned to appear at the police station in Antwerp, Belgium, on suspicion of premeditated murder. 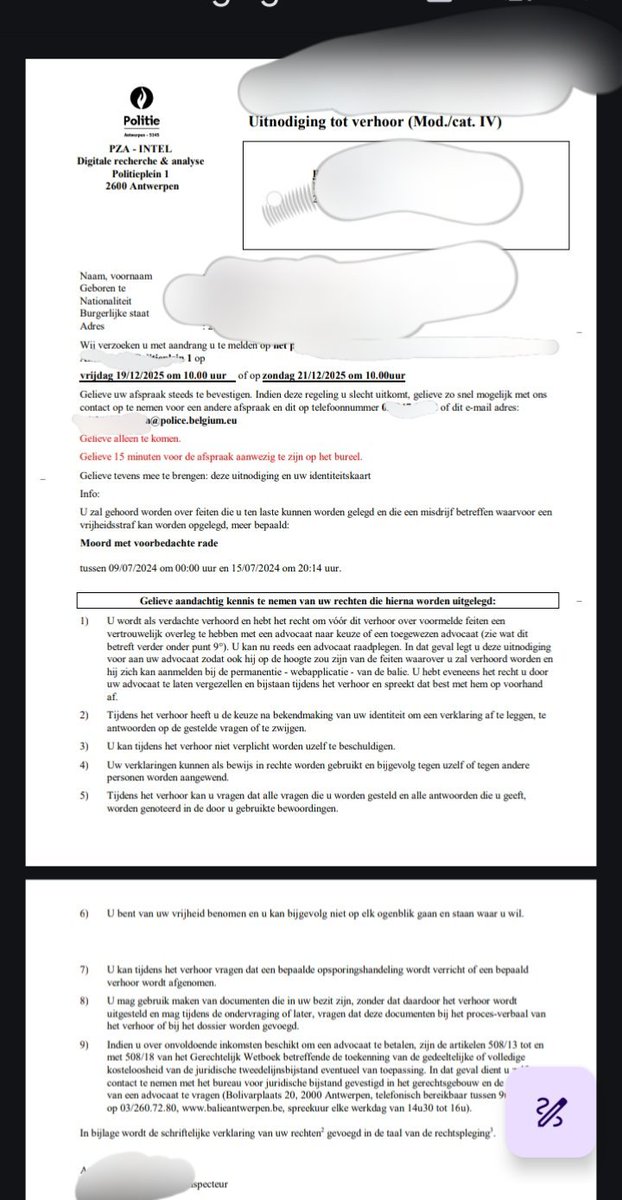

 Internal leaked company documents, sales and marketing materials, as well as training videos from the “Intellexa Leaks” investigation provide a never-before-seen glimpse into the internal operations of a mercenary spyware company focused on exploiting vulnerabilities in mobile devices to enable targeted surveillance attacks on human rights defenders, journalists, and members of civil society.
Internal leaked company documents, sales and marketing materials, as well as training videos from the “Intellexa Leaks” investigation provide a never-before-seen glimpse into the internal operations of a mercenary spyware company focused on exploiting vulnerabilities in mobile devices to enable targeted surveillance attacks on human rights defenders, journalists, and members of civil society.


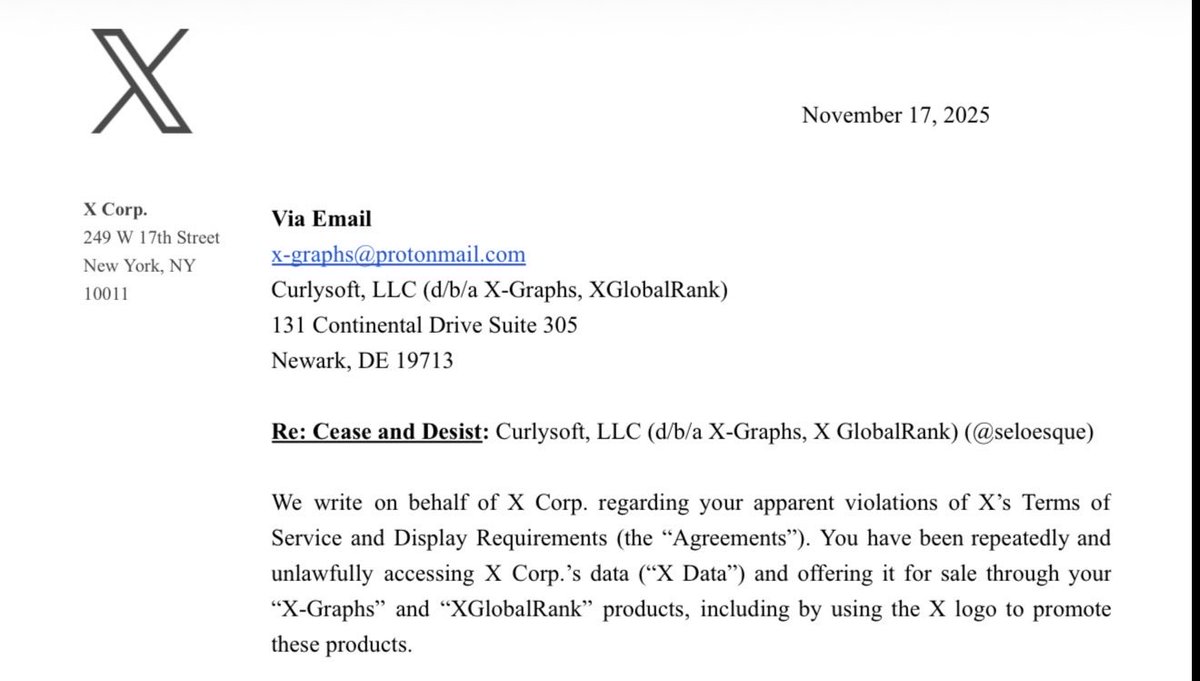
 Despite the developer being open about his project with X employees from the beginning, and getting a job interview and vouch because of it, Nikita Bier mocked him after he was sent a cease and desist.
Despite the developer being open about his project with X employees from the beginning, and getting a job interview and vouch because of it, Nikita Bier mocked him after he was sent a cease and desist.

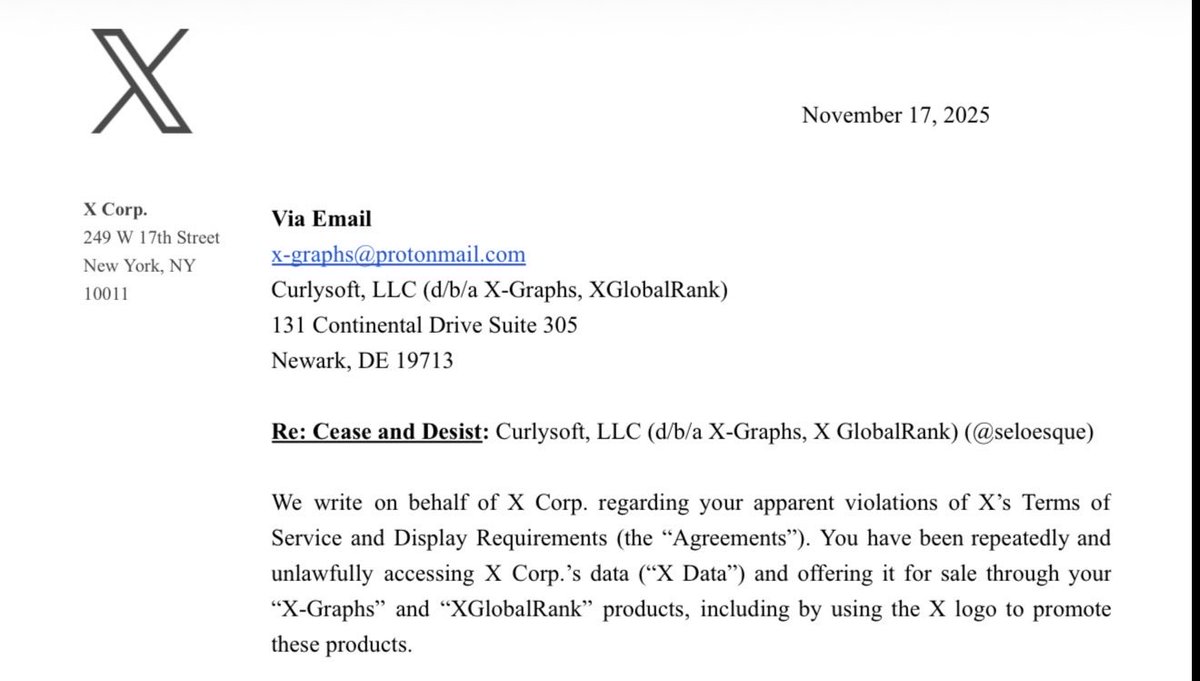
 The documents show a network operations training environment capable of supporting 300 users and 10,000 concurrent connections. It includes DNS gateways, a URL classification database with 100 million entries, and support for 50,000 concurrent connections.
The documents show a network operations training environment capable of supporting 300 users and 10,000 concurrent connections. It includes DNS gateways, a URL classification database with 100 million entries, and support for 50,000 concurrent connections. 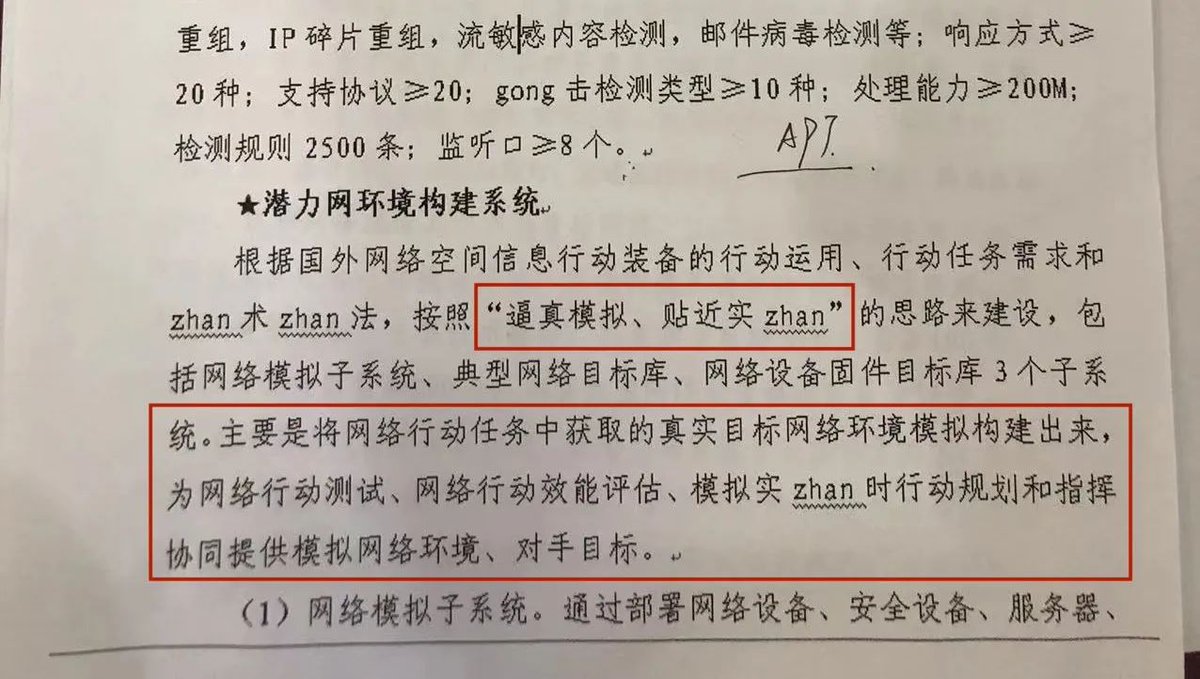

 ZoomEye
ZoomEye
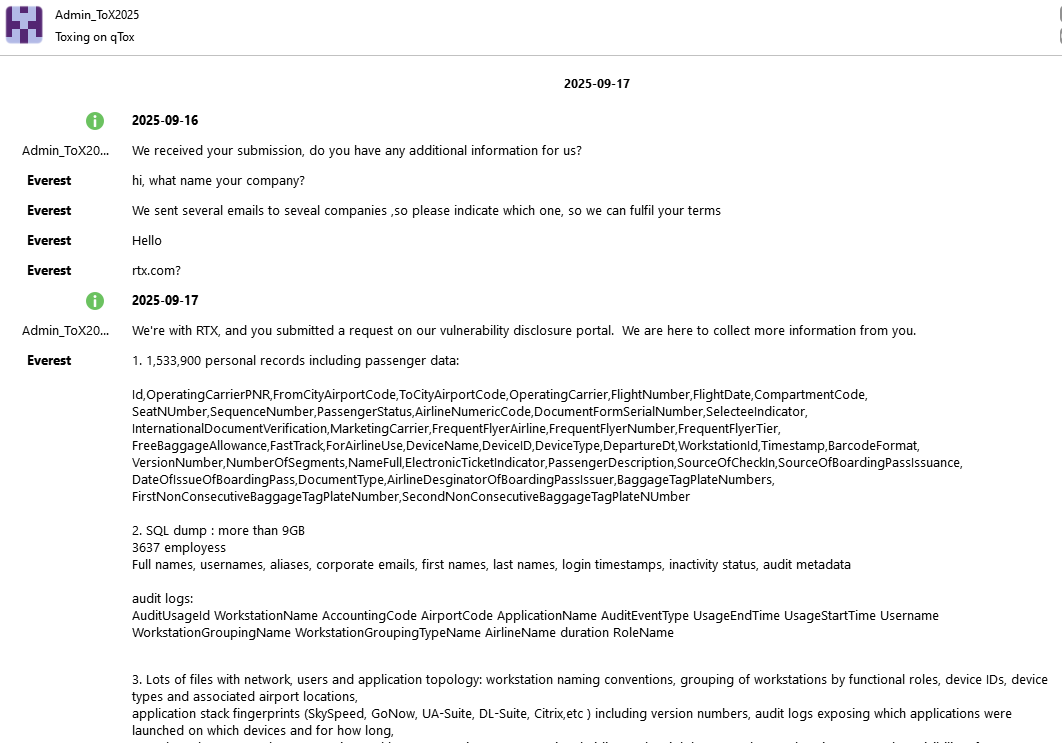
 This is the compromised SFTP server. Username: aiscustomer, password: muse-insecure. Insecure indeed. Why store sensitive files like passenger data, SQL, service documentation, and configurations on a publicly accessible, insecure SFTP server?
This is the compromised SFTP server. Username: aiscustomer, password: muse-insecure. Insecure indeed. Why store sensitive files like passenger data, SQL, service documentation, and configurations on a publicly accessible, insecure SFTP server? 



https://twitter.com/IntCyberDigest/status/1975846997568737666
 Tables:
Tables: