
The Cyber Populist | Hacker. Writer. Heretic. | Reverse engineering narratives, systems, and power. Holding the pen.
How to get URL link on X (Twitter) App

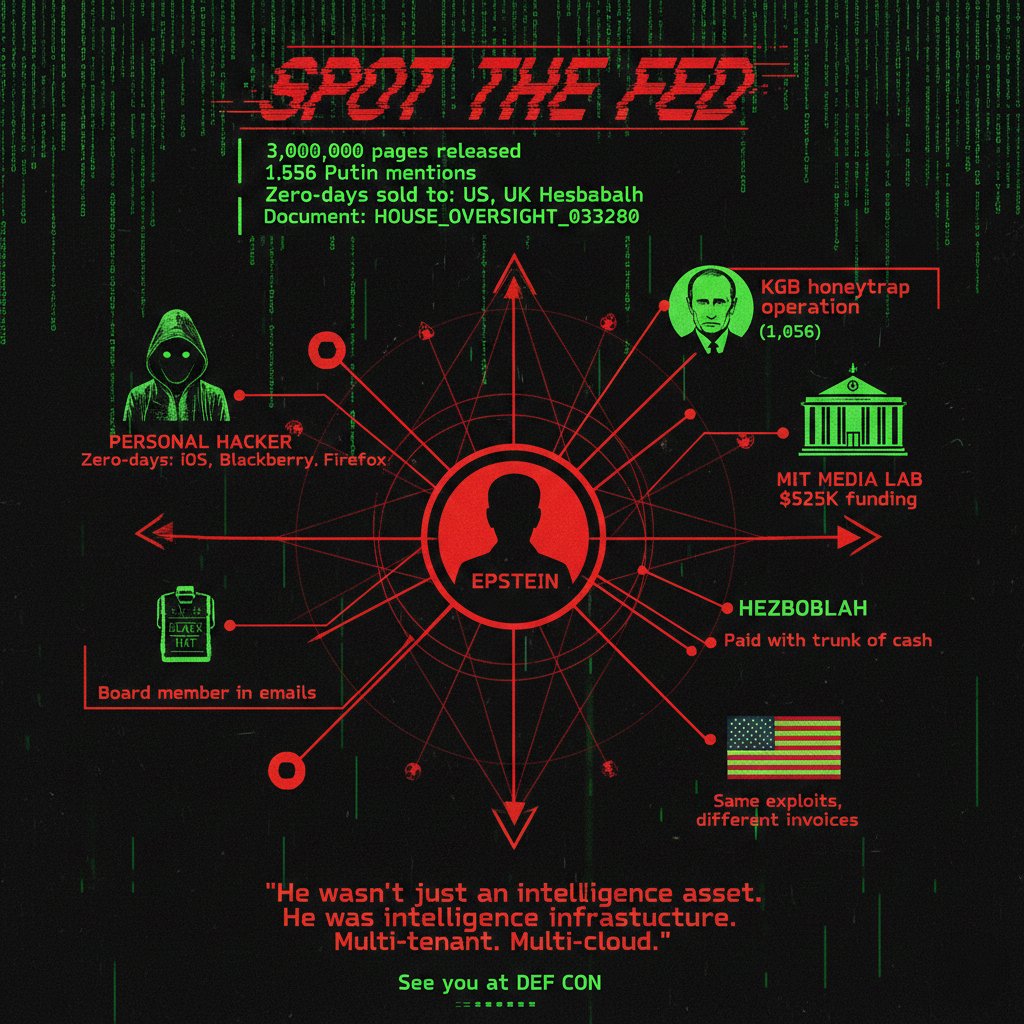
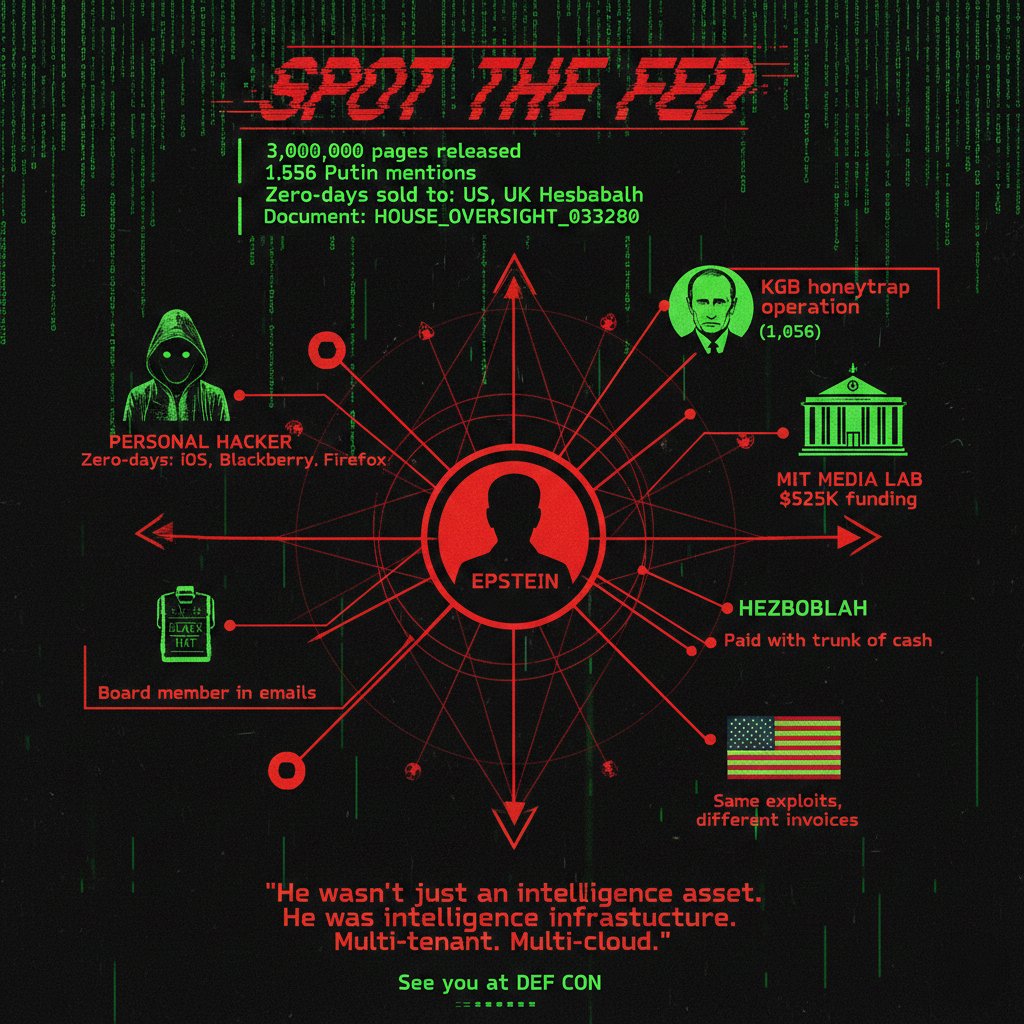
https://x.com/gothburz/status/2045574398573453312The Frankfurt School's fundamental error was assuming that diagnosing power's machinery would inoculate you against building it. Karp proved the opposite thesis. The man who can name every gear in the cage builds the tightest one.


 TL;DR:
TL;DR: