So, here we go! This one is a big one.
👇 👇
The Jeffrey Epstein Associate Nobody's Talking About: The IDF Linked Bond Girl Infiltrating the UK NHS - FIFA Corruption, the Panama Papers, & the Mossad by @JohnnyVedmore via @vocal_creators #Epstein #NHS
theswamp.media/the-epstein-as…
👇 👇
The Jeffrey Epstein Associate Nobody's Talking About: The IDF Linked Bond Girl Infiltrating the UK NHS - FIFA Corruption, the Panama Papers, & the Mossad by @JohnnyVedmore via @vocal_creators #Epstein #NHS
theswamp.media/the-epstein-as…
Last week, when you typed “Nicole Junkermann” into google, it would autocomplete with age, wealth or husband etc.
Now, you type in Nicole Junkermann, the first autocomplete option is “Nicole Junkermann Epstein”.
I’m taking credit for that 😉
Thanks to everyone for sharing 😘
Now, you type in Nicole Junkermann, the first autocomplete option is “Nicole Junkermann Epstein”.
I’m taking credit for that 😉
Thanks to everyone for sharing 😘
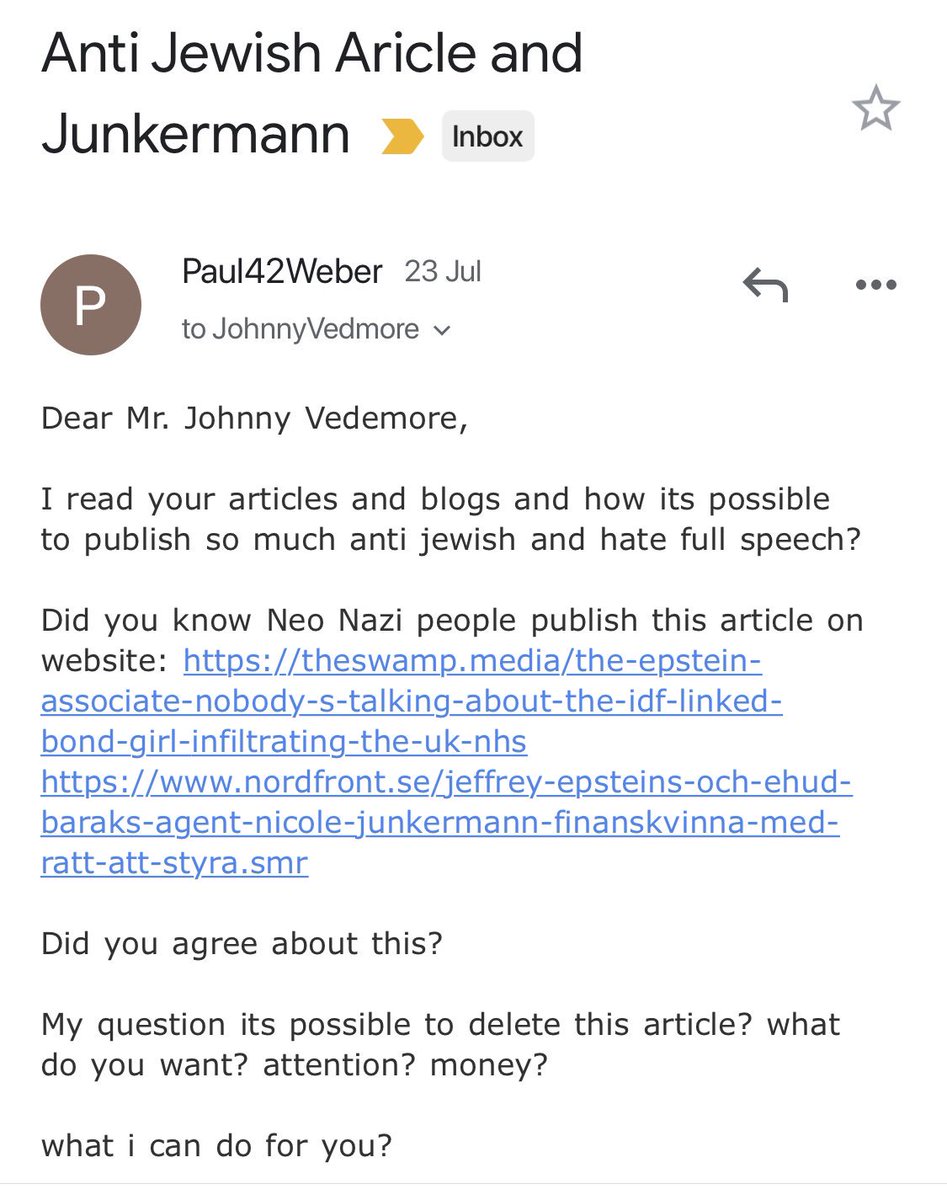
Here is the first email I’ve received from the allies of Nicole Junkermann, trying to make me take this story down, and my response.
Even though I only talk about her factual links with Israeli Intelligence, apparently that’s antisemitic. Not a surprise.
They ask for my price.


Even though I only talk about her factual links with Israeli Intelligence, apparently that’s antisemitic. Not a surprise.
They ask for my price.

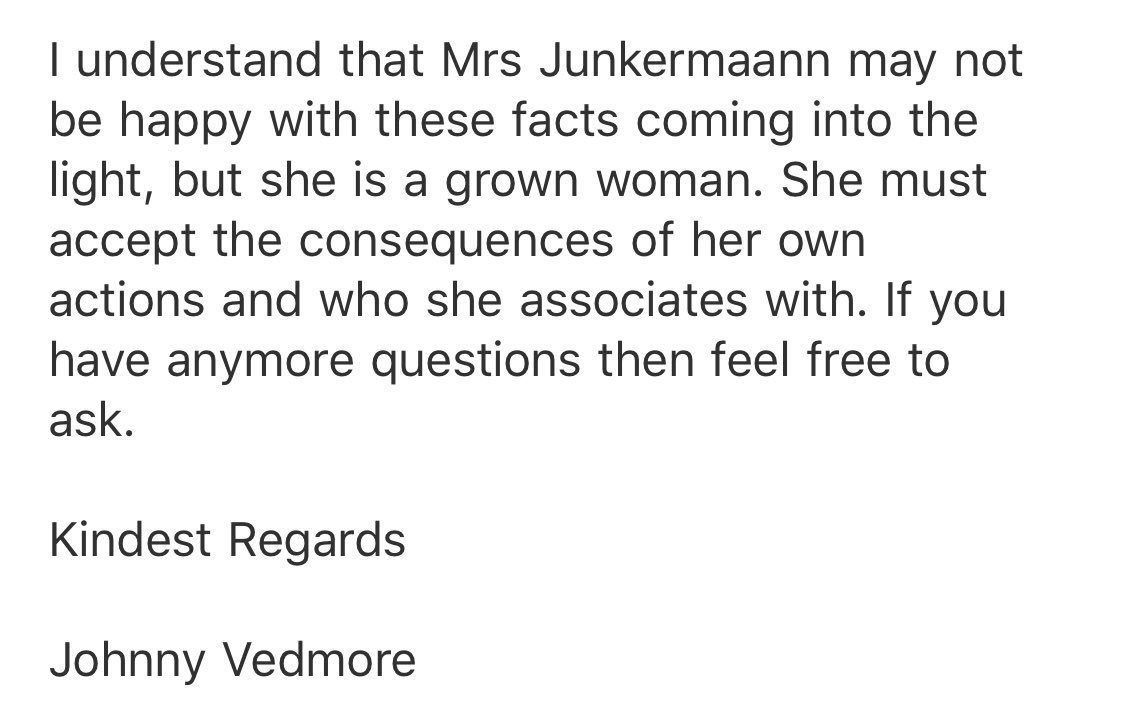
This 2nd email is from a lady called Natalie Leibniz. She claims to have taken all the photos from my article, even though there are photos from different sources, and the others are screenshots from a published website of great public interest. Can you copyright a screenshot? 



The lady who’s threatening legal action against me doesn’t seem to want to communicate. I still can’t verify her identity so I can credit her in the article. A credit she doesn’t seem to want.
Natalya or Natalie, Leibniz or Libitc?
She uses both names in her correspondence.


Natalya or Natalie, Leibniz or Libitc?
She uses both names in her correspondence.



I’m still hunting for Jeffrey Epstein & Nicole Junkermann’s location in the UK on 1st September 2002.
Is it a coincidence that it was Alan Dershowitz’s birthday?
Junkermann had graduated Harvard, Dershowitz was teaching Law at Harvard, & Epstein was about to donate to Harvard.
Is it a coincidence that it was Alan Dershowitz’s birthday?
Junkermann had graduated Harvard, Dershowitz was teaching Law at Harvard, & Epstein was about to donate to Harvard.
"Nicole runs NJF Holdings, based in London, and has collaborated on investments with Silicon Valley personalities such as Eric Schmidt —Google— or Peter Thiel — Paypal."
From Vanity Fair Magazine, 2019.
revistavanityfair.es/poder/articulo…
From Vanity Fair Magazine, 2019.
revistavanityfair.es/poder/articulo…
• • •
Missing some Tweet in this thread? You can try to
force a refresh








