The term is “daylight saving” but I’ll take that up with the Relevant People at a later date.
* Note weasel words.
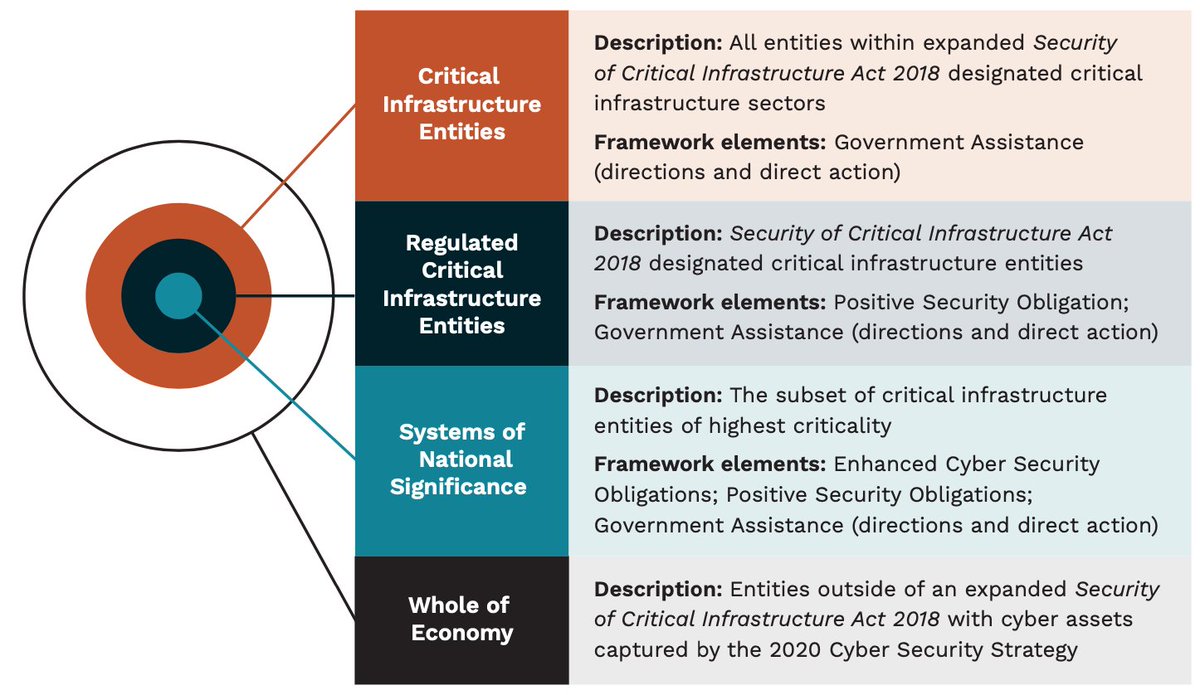
• Banking and finance
• Communications
• Data and the Cloud
• Defence industry
• Education, research and innovation
• Energy
• Food and grocery
• Health
• Space
• Transport
• Water.
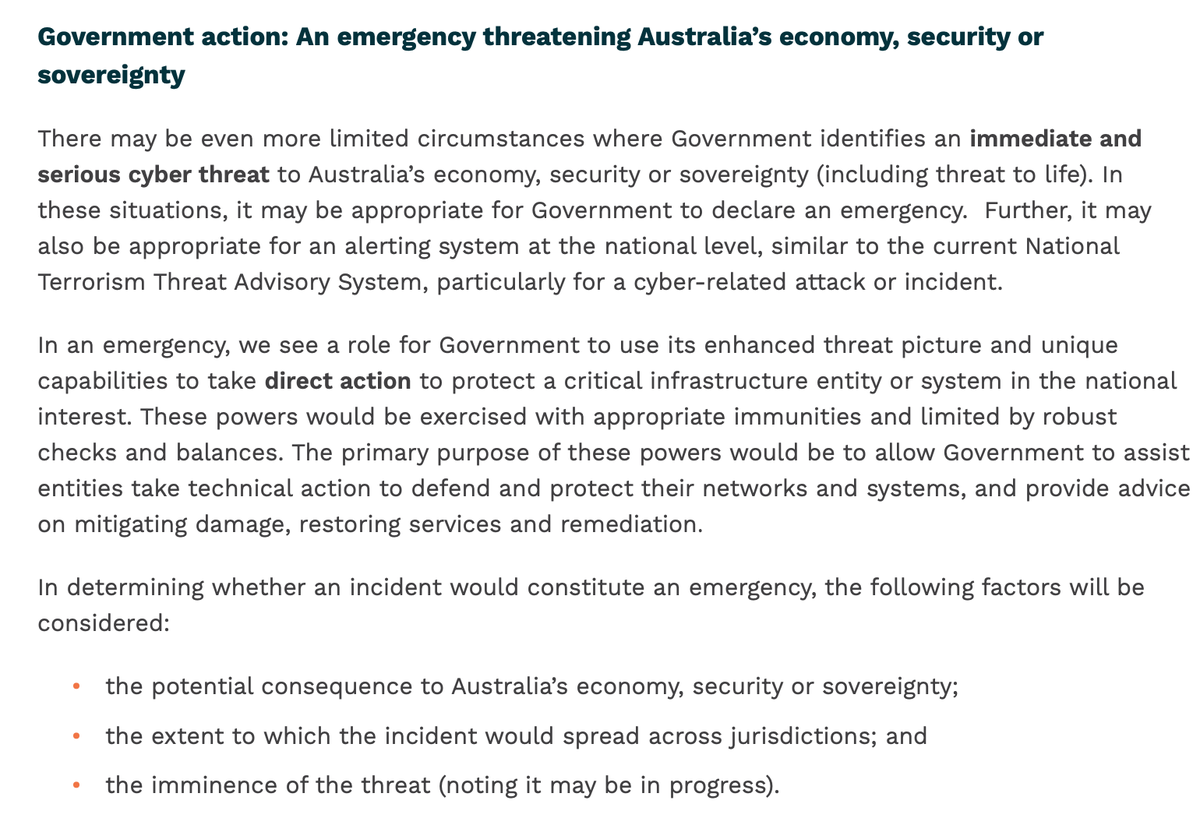
“A a minimum, owners and operators of critical infrastructure should be legally obliged to manage risks that may impact business continuity and Australia’s economy, security and sovereignty.”
(This law will be very difficult to write, but odds-on they’ll want it by Christmas. Before Dutton is sacked, anyway.)