ORF (media) in Austria report that 5 eyes Intelligence Community have convinced EU Council to secretly resolve for a total EU backdoor on end-to-end encryption.
(in German) fm4.orf.at/stories/300893…
Draft Resolution:
files.orf.at/vietnam2/files…
(in German) fm4.orf.at/stories/300893…
Draft Resolution:
files.orf.at/vietnam2/files…
There’s some gems in this (drafty) resolution:
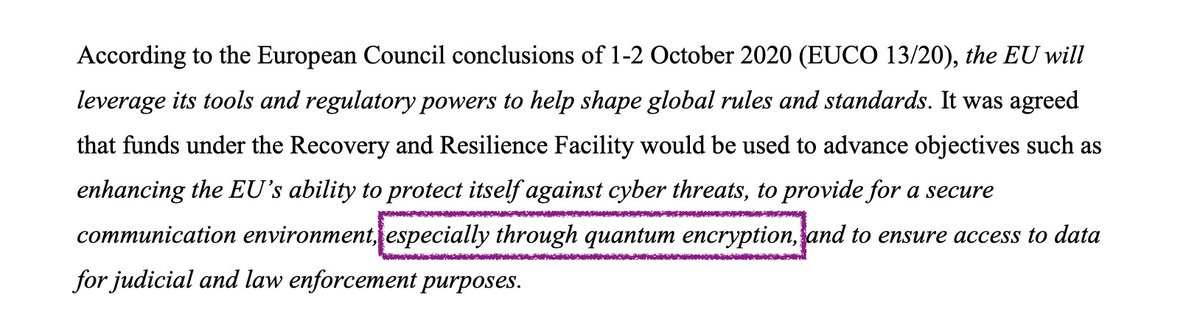
They’re going to steal money from the Recovery and Resilience Facility to “advance objectives” relating to cybersecurity.
How broken is that? 🧐 Do they know no shame?
They’re going to steal money from the Recovery and Resilience Facility to “advance objectives” relating to cybersecurity.
How broken is that? 🧐 Do they know no shame?

The meeting of JHA Counsellors (Encryption) whatever they are also called out quantum encryption.
Does this mean
- they want to backdoor quantum encryption as well,
- pay off their academic advisors, OR
- they have no clue what they are talking about?
the bind moggles… 🤨
Does this mean
- they want to backdoor quantum encryption as well,
- pay off their academic advisors, OR
- they have no clue what they are talking about?
the bind moggles… 🤨
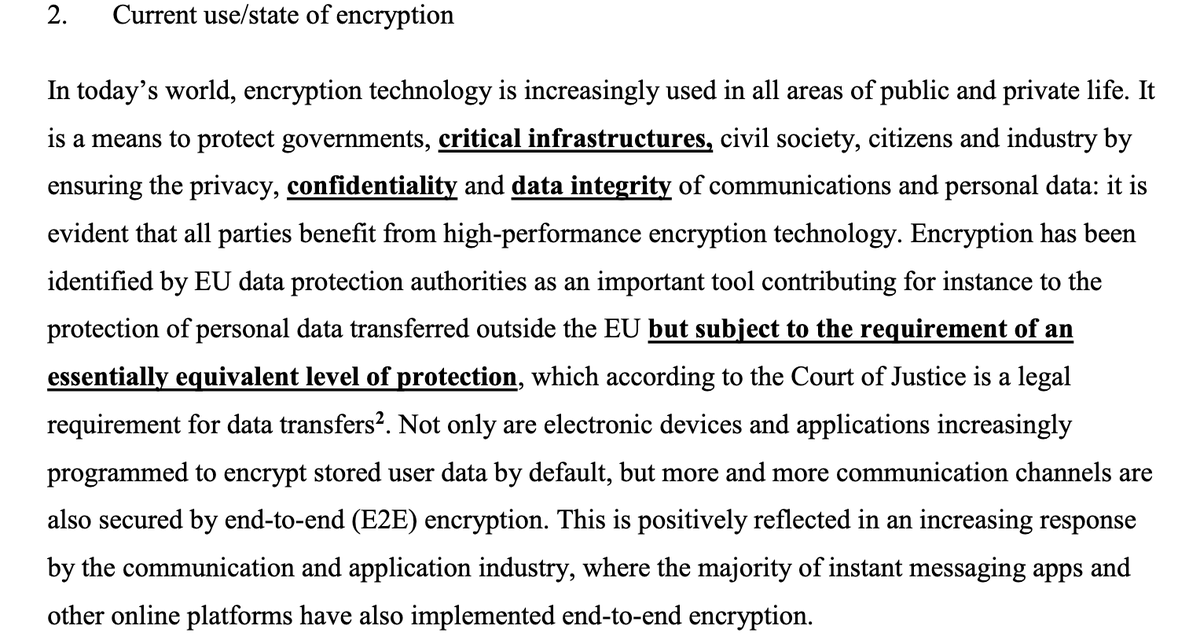
Oddly, they seem entirely aware that the European Court of Justice has ruled that strong protections including full encryption must be available when moving data outside the EU.
Setting up for ECJ to tell them they can’t have their cake and eat it too?
Setting up for ECJ to tell them they can’t have their cake and eat it too?
The problem with this statement - that it is essential to break encryption to fight various crimes - is that it is just not true.
The evidence that has been surfaced through court cases and the like has pointed out that encryption did not slow or hinder the investigation.
The evidence that has been surfaced through court cases and the like has pointed out that encryption did not slow or hinder the investigation.
This untruth reveals that the real purpose of the breaking of encryption is for intelligence community (IC) mass surveillance. The reason we know this is that it has been the same pattern for 30 years (who remembers FBI's Louis Freeh?):
IC speaks through Justice ministries.
IC speaks through Justice ministries.
Section 6. Legal Framework plays the olive branch tactic of “cooperation” with industry that has so well failed in the past.
As there is no plausible solution that ensures the safety of customers, their only option is 1) legislate 2) force backdoors thus 3) Break the security.
As there is no plausible solution that ensures the safety of customers, their only option is 1) legislate 2) force backdoors thus 3) Break the security.
As a simple argument - the call for a consistent framework ensures broad surveillance across EU.
Access to 30 countries’ backdoor farms by 30 “competent authorities”...
Can the EU guarantee lack of corruption in 30 police & intelligence agencies?
No. Fail.
Access to 30 countries’ backdoor farms by 30 “competent authorities”...
Can the EU guarantee lack of corruption in 30 police & intelligence agencies?
No. Fail.
• • •
Missing some Tweet in this thread? You can try to
force a refresh