
Ledger Nano devices threat model is quite simple and could be summarized as follows:
1. Confidentiality of keys
2. Secure use with user consent
3. Genuineness check
4. Users' privacy
[2/n]
donjon.ledger.com/threat-model/
1. Confidentiality of keys
2. Secure use with user consent
3. Genuineness check
4. Users' privacy
[2/n]
donjon.ledger.com/threat-model/
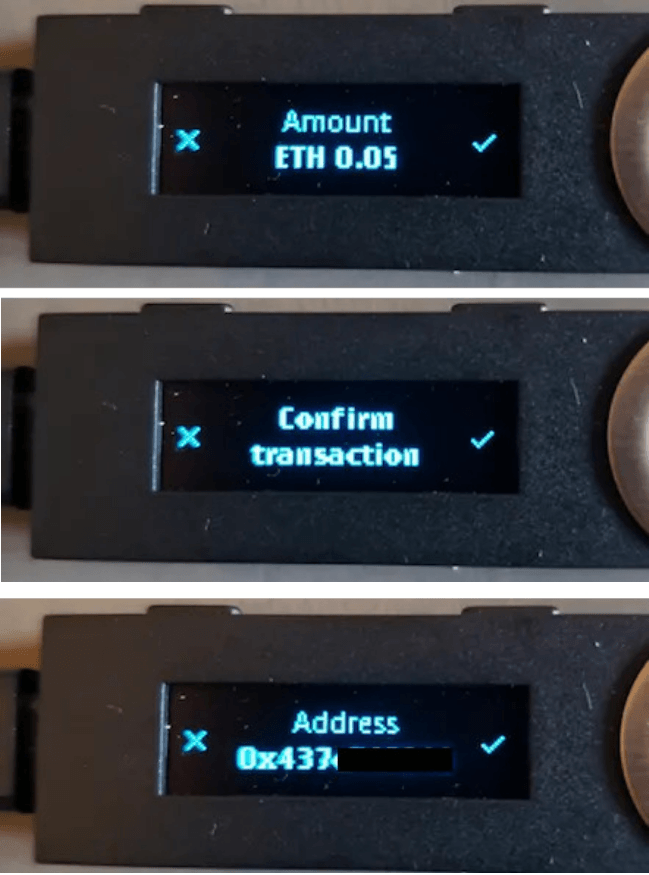
To ensure user consent, the device implements a Trusted Display. Only the info displayed on the device's screen can be trusted.
When you want to make an ETH transaction, you have to verify amount, recipient and fees on the device
[3/n]
When you want to make an ETH transaction, you have to verify amount, recipient and fees on the device
[3/n]
When it comes to smartcontract interaction, it becomes more tricky. It's not possible to parse smartcontracts calls and make them human readable in a generic and trusted way.
In this situation, there are 2 cases:
[4/n]
In this situation, there are 2 cases:
[4/n]
Case 1 - The smartcontract call is supported and the device is able to display all the relevant data to the user.
This is the case for ERC20 transfer, Coumpound or ETH2 contract deposit.
[5/n]
ledger.com/blog/lend-dire…
ledger.com/blog/ledger-is…
This is the case for ERC20 transfer, Coumpound or ETH2 contract deposit.
[5/n]
ledger.com/blog/lend-dire…
ledger.com/blog/ledger-is…
Case 2 - The smartcontract is NOT supported. To avoid users having locked funds, it's still possible to blind-sign (no human readable data) the interaction.
In such a case, we're out of the Nano threat model, the security is reduced to any wallet without Trusted Display.
[6/n]
In such a case, we're out of the Nano threat model, the security is reduced to any wallet without Trusted Display.
[6/n]
Blind signing is not secure, that's why we implemented a Trusted Display at the first place.
It's worth noting Ledger Live never asks for blind signing. Some 3rd party integration, like metamask or WalletConnect can ask for blind signing when the contract is not supported
[7/n]
It's worth noting Ledger Live never asks for blind signing. Some 3rd party integration, like metamask or WalletConnect can ask for blind signing when the contract is not supported
[7/n]
For the future, we're working on a plugin mechanism for ETH app allowing easier smartcontract interaction implementation. We're also thinking about a better UX for blind-signing. It will be announced soon. Stay tuned.
[8/n]
[8/n]
• • •
Missing some Tweet in this thread? You can try to
force a refresh




