Europol: Emotet malware will uninstall itself on March 25th - @LawrenceAbrams
bleepingcomputer.com/news/security/…
bleepingcomputer.com/news/security/…
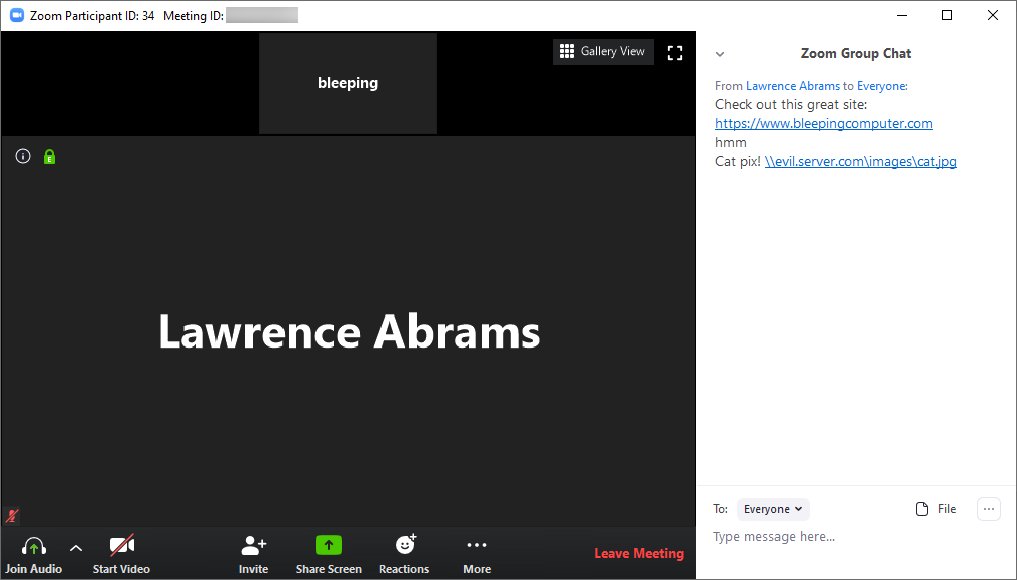
After today's disruption of the Emotet malware, security research milkream discovered that a new module was being pushed to infected PCs.
This module will automatically uninstall Emotet from infected devices on March 25th, 2021.
This module will automatically uninstall Emotet from infected devices on March 25th, 2021.
https://twitter.com/milkr3am/status/1354459859912192002
In a phone call, Europol's press office confirmed that the German Bundeskriminalamt (BKA) federal police was in charge of this uninstall operation.
This correlates with Emotet's new command and control servers, which are now all located in Germany.
https://twitter.com/milkr3am/status/1354473617145409545
After further analysis by Malwarebytes, the correct uninstall date is April 25th, 2020. We have updated our story to include this information.
https://twitter.com/MBThreatIntel/status/1354842730711502850
The confusion was caused by how the Microsoft Time structure's tm_mon value starts at 0, not 1.
docs.microsoft.com/en-us/cpp/c-ru…
docs.microsoft.com/en-us/cpp/c-ru…
Some further info from Germany's @bka in response to our inquiries into the new module. 

The US DOJ also released press release today with further information about a "law enforcement file" that would be distributed to devices infected with Emotet.
justice.gov/opa/pr/emotet-…
justice.gov/opa/pr/emotet-…

• • •
Missing some Tweet in this thread? You can try to
force a refresh