In more Securing Democracy at #enigma2021, @ChrFolini talking about "THE ADVENTUROUS TALE OF ONLINE VOTING IN SWITZERLAND"
usenix.org/conference/eni…
usenix.org/conference/eni…
Switzerland is a direct democracy where citizens get to vote at least 4x/year, with a lot of mail-in voting. We have a long history of online voting.
Disclaimer: THIS IS NOT SWEDEN.
[I get the picture that @ChrFolini has had to explain the difference several times.]
Disclaimer: THIS IS NOT SWEDEN.
[I get the picture that @ChrFolini has had to explain the difference several times.]

Process around mail-in ballots.
[tl;dr it's very complicated and wasn't threat-modeled until recently]
[tl;dr it's very complicated and wasn't threat-modeled until recently]

Most security folks don't think that we can't make a secure online voting system.
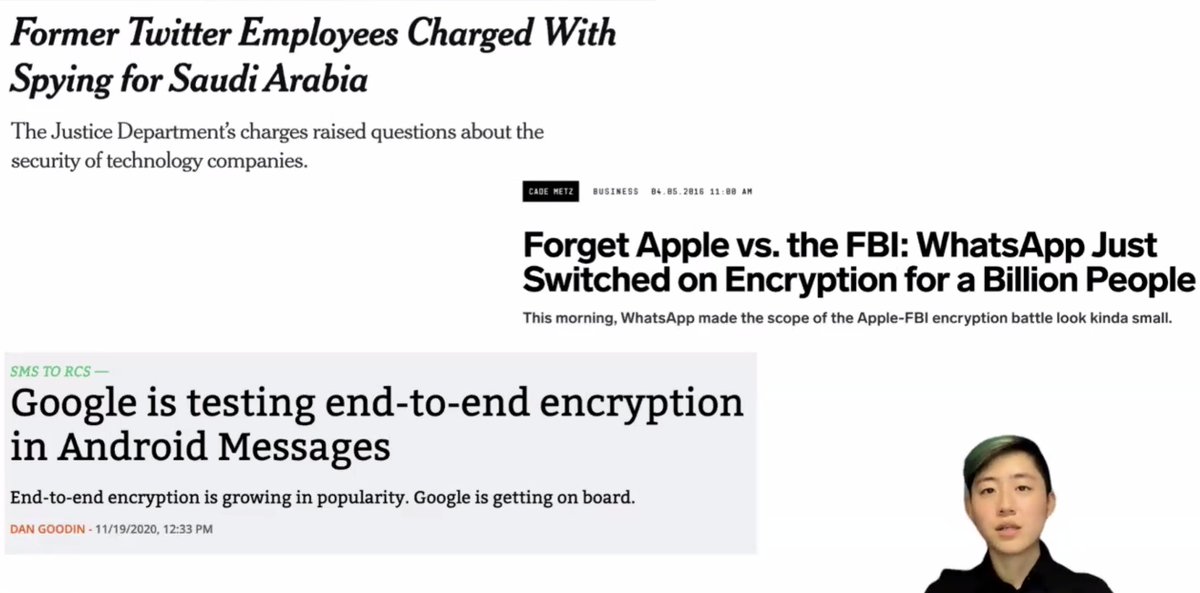
@ChrFolini says this is because of encryption
[Note: this is not the main reason that a lot of people cite -- we're more worried about things like malware but it's complicated]
@ChrFolini says this is because of encryption
[Note: this is not the main reason that a lot of people cite -- we're more worried about things like malware but it's complicated]
There are reasons to want online voting:
* Citizens living abroad
* Visually impaired and quadriplegic voters need to have assistants that they trust
* Many invalid ballots (even <10%!)
* Physical voting has security problems, too
* Citizens living abroad
* Visually impaired and quadriplegic voters need to have assistants that they trust
* Many invalid ballots (even <10%!)
* Physical voting has security problems, too
Like the states of the US, there are cantons in Switzerland, federalized system. The cantons have almost complete control over the elections *except* that the federal system has exclusive control over the security of online voting.
Several cantons have been experimenting, with Geneva being the first, followed by a group of eight cantons. 

In 2017 the federal chancellor calls for 2/3 of the cantons to offer internet voting for national elections in 2019. There were not many CS people represented and they declared internet voting "solved".
That was a wakeup for people on internet voting.
That was a wakeup for people on internet voting.
Geneva pulled funding after political quarrels... which paved the way for SwissPost.
In 2019 they posted the source code before the election. It didn't take long for several fundamental security flaws to be found.
[ I can't type this fast and find everyone's names sorry]
In 2019 they posted the source code before the election. It didn't take long for several fundamental security flaws to be found.
[ I can't type this fast and find everyone's names sorry]
In the wake of that failure everyone figured out that internet voting was not, in fact, solved. At all.
So they brought in a bunch of experts.
So they brought in a bunch of experts.
What happens if you get together a bunch of experts? A scientific report!
[If someone has a link, please reply with it]
@ChrFolini was brought in to moderate the workshops... then the pandemic hit. Lots of debate on cryptography, software development, etc.
[If someone has a link, please reply with it]
@ChrFolini was brought in to moderate the workshops... then the pandemic hit. Lots of debate on cryptography, software development, etc.
After all that debate and new work, there is a new report [anyone have a link? @ChrFolini?] in line with the recommendations of the scientists. But we'll need to keep tweaking as tech changes.
Key recommendations:
* Strict hierarchy of recommendations, starting with a verifier model which can be reasoned about, then moving to pseudocode then code. Use formal models.
* Strict hierarchy of recommendations, starting with a verifier model which can be reasoned about, then moving to pseudocode then code. Use formal models.
* Diversity of hard- and soft-ware to resist attacks. It's more expensive, but there are security benefits.
[Boy howdy this is going to be controversial one, depending on how this is set up -- checks of different versions against each other?]
[Boy howdy this is going to be controversial one, depending on how this is set up -- checks of different versions against each other?]
* Maximum level of transparency, especially in development
* Voting security beyond internet voting
* Voting security beyond internet voting
Summary:
* Switzerland is a useful testbed for online voting
* Iterative process with strict supervision on federal level
* Expert dialogue with recommendations in 2020
* Switzerland is a useful testbed for online voting
* Iterative process with strict supervision on federal level
* Expert dialogue with recommendations in 2020
@ChrFolini sees online voting as something which may or may not be securable but it's a political question whether it's introduced... so we'd better work on it.
[paraphrased]
[paraphrased]
Giving my hands a break, so end of talk as the questions are coming thick and fast (not at all shocking!)
• • •
Missing some Tweet in this thread? You can try to
force a refresh