Last talk about Securing Democracy at #enigma2021: @jackhcable speaking about "THE FULL STACK PROBLEM OF ELECTION SECURITY"
usenix.org/conference/eni…
usenix.org/conference/eni…
Let's imagine that elections use all the security measures security people have been advocating: risk-limiting audits, paper ballots, etc. Would people trust the elections more?
Jack would argue no. Most people don't understand this stuff and most of the claims people are making can't be disproven. And are massively bogus already.
Georgia did a full recount on paper ballots and it very much didn't stop people from doubting the election!
Georgia did a full recount on paper ballots and it very much didn't stop people from doubting the election!
Are election security results in vain? The point of election security is to convince the loser they lost.
No! Have to focus on the whole stack, from election infrastructure to campaigns to people and mis/dis-informaton
No! Have to focus on the whole stack, from election infrastructure to campaigns to people and mis/dis-informaton
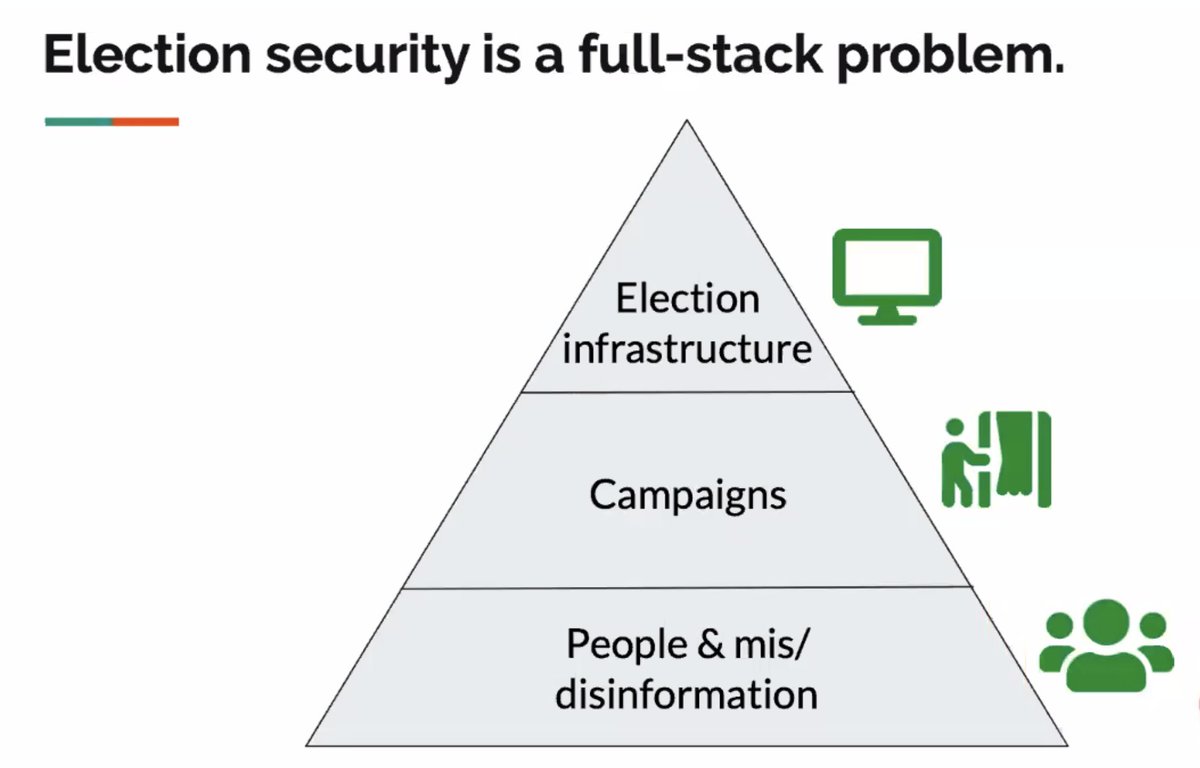
One takeaway from the talk: the parts of the stack must work in tandem. Can't fight misinformation in a vacuum, but must build on other election security measures.
The voting process
* significant advances in recent years (e.g. paper ballots, risk-limiting audits, end-to-end verifiability)
* research needed in integrating these technologies
* expanding to mail-in voting?
* significant advances in recent years (e.g. paper ballots, risk-limiting audits, end-to-end verifiability)
* research needed in integrating these technologies
* expanding to mail-in voting?
But there's also internet voting
* we can't do it securely today [oh no voatz reference]
* we have to combat malware, authentication etc.
* if we could solve them, that would be great. But in the meantime voting has to be successful for everyone
* we can't do it securely today [oh no voatz reference]
* we have to combat malware, authentication etc.
* if we could solve them, that would be great. But in the meantime voting has to be successful for everyone
* can improve accessibility through things like getting ballot online, filling it out, then returning through the mail
Election support systems
* less researched. Probably because they look boring
* Voter registration databases aren't working. Russians breached at least 2 states, targeted all 50 states
* little to no public scrutiny of these systems
* less researched. Probably because they look boring
* Voter registration databases aren't working. Russians breached at least 2 states, targeted all 50 states
* little to no public scrutiny of these systems
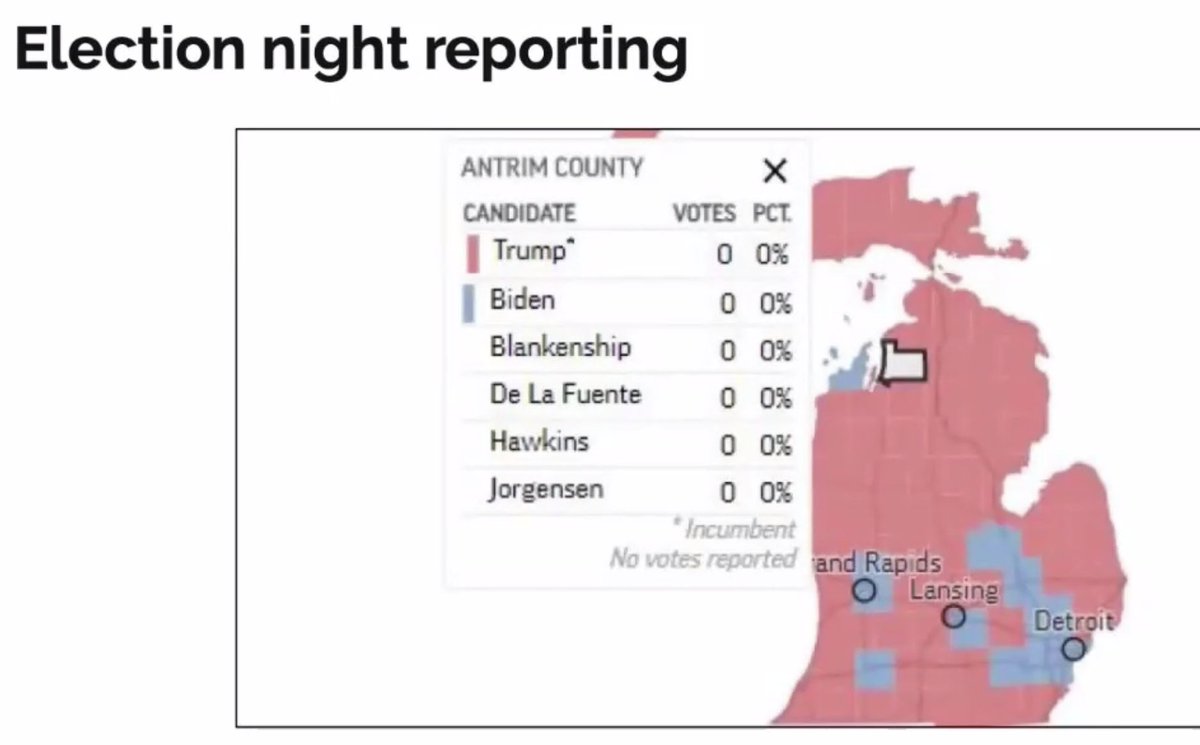
* election night reporting -- this is a picture of one where there was a bug in reporting. [It was fixed but freaked a lot of people out] 
A lot of the trouble with the security of election support systems is not that we don't know how to do it -- it's that we have to do it
Campaign security
* biggest unknown (see Sunny Consolvo's talk!)
* we must view campaign security as non-partisan and increase resources and services available
* biggest unknown (see Sunny Consolvo's talk!)
* we must view campaign security as non-partisan and increase resources and services available
Public confidence
* major damage from domestic actors
* widespread mis/dis-information
* technical election security measures helps to debunk rumours floating around
* major damage from domestic actors
* widespread mis/dis-information
* technical election security measures helps to debunk rumours floating around
Misinformation-fighting supply measures:
* platforms: downranking and deplatforming
* trusted institutions
* debunking & fact checks
* platforms: downranking and deplatforming
* trusted institutions
* debunking & fact checks
Misinformation-fighting demand measures:
* media literacy
* increased civics education
[ Also note that @katestarbird will be giving a talk on misinformation don't miss it: usenix.org/conference/eni…]
* media literacy
* increased civics education
[ Also note that @katestarbird will be giving a talk on misinformation don't miss it: usenix.org/conference/eni…]
Let's fix election support systems!
* Much of this is applying security things we already know
[ Note: a lot of organizations have this problem 😭 ]
* engage in public research. Have a vuln disclosure policy so people can confidently help
* Much of this is applying security things we already know
[ Note: a lot of organizations have this problem 😭 ]
* engage in public research. Have a vuln disclosure policy so people can confidently help
Election security is a problem that can only be solved by working together: elections officials, security people, everyone
[end of talk]
[end of talk]
• • •
Missing some Tweet in this thread? You can try to
force a refresh