Last talk at #enigma2021 for today by Pardis Emami-Naeini on "PRIVACY AND SECURITY NUTRITION LABELS TO INFORM IOT CONSUMERS"
usenix.org/conference/eni…
usenix.org/conference/eni…
People keep buying smart devices, but they're worried about them. Which makes sense because they keep getting hacked! 

Also IoT companies are forgetful, like when Google forgot to tell people that Nest camera included a microphone.
... and there are lots of these things we don't know yet, like how Amazon employees were listening to Alexa recordings.
... and there are lots of these things we don't know yet, like how Amazon employees were listening to Alexa recordings.
Users don't know enough about the data sharing and selling practices of these devices. Our proposal? A label for smart devices.
This is the most recent version of this label [apologies I cannot type this out there are pictures]
This is the most recent version of this label [apologies I cannot type this out there are pictures]

Multi-step path to label design
1. Large-scale surveys
2. Consumer interviews
3. Expert interviews
4. Consumer interviews
1. Large-scale surveys
2. Consumer interviews
3. Expert interviews
4. Consumer interviews
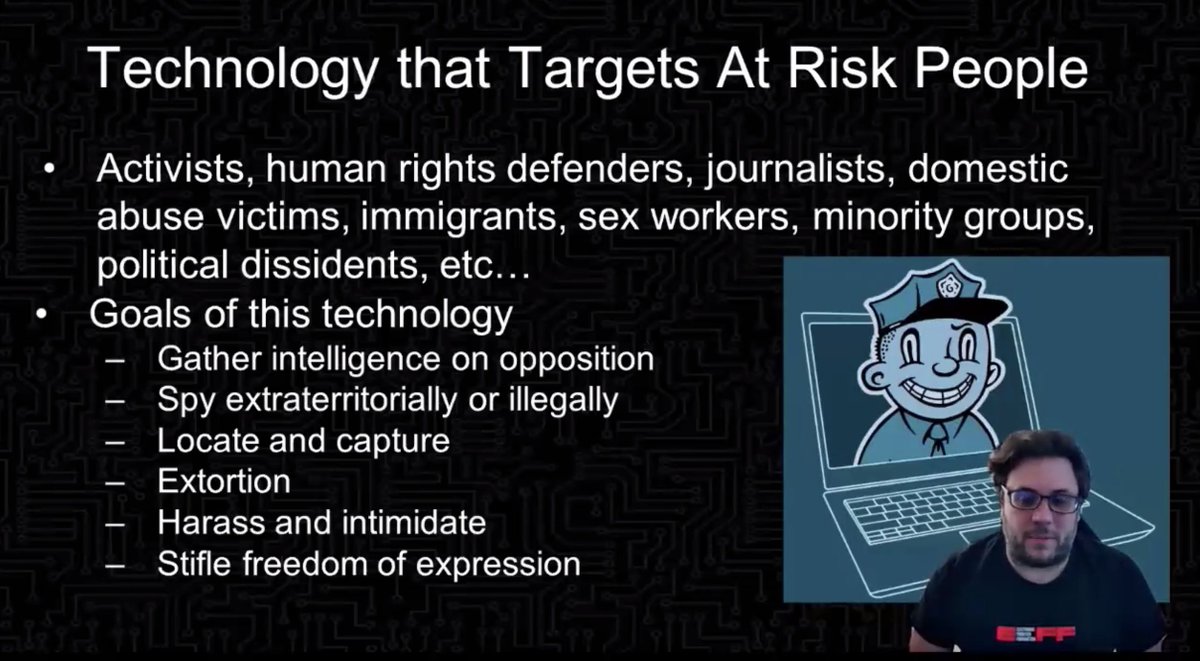
Found that context was more important than individual factors, so need to show the data holistically rather than focusing on particular factors in isolation
Social influence factors
* level of expertise (friend vs expert)
* consensus level (strong vs weak)
* difference of opinion (consistent vs inconsistent)
* level of expertise (friend vs expert)
* consensus level (strong vs weak)
* difference of opinion (consistent vs inconsistent)
Used these in experiments to show a social cue to some users e.g. "85% of users allowed this collection"
Experiments showed that both friends and privacy experts influenced privacy decisions
Experiments showed that both friends and privacy experts influenced privacy decisions
Studies showed positive attitude towards labels:
* almost everyone wanted security and privacy information before purchase
* would be willing to pay 10-30% more for this information
* almost everyone wanted security and privacy information before purchase
* would be willing to pay 10-30% more for this information
Privacy and security are latent concerns
* they might not think to be worried about it up front, but when Alexa starts laughing out of nowhere they get freaked out
* so putting security and privacy information up front can help people make choices which take this into account
* they might not think to be worried about it up front, but when Alexa starts laughing out of nowhere they get freaked out
* so putting security and privacy information up front can help people make choices which take this into account
Policy makers are excited about nutrition labels
... but why? And why aren't they thinking about privacy? What should be on the label
... but why? And why aren't they thinking about privacy? What should be on the label

Held an expert panel
* ended up with so much stuff that they broke it up into two layers with different levels of detail (one online, so it can be more detailed and easily updated)
* ended up with so much stuff that they broke it up into two layers with different levels of detail (one online, so it can be more detailed and easily updated)

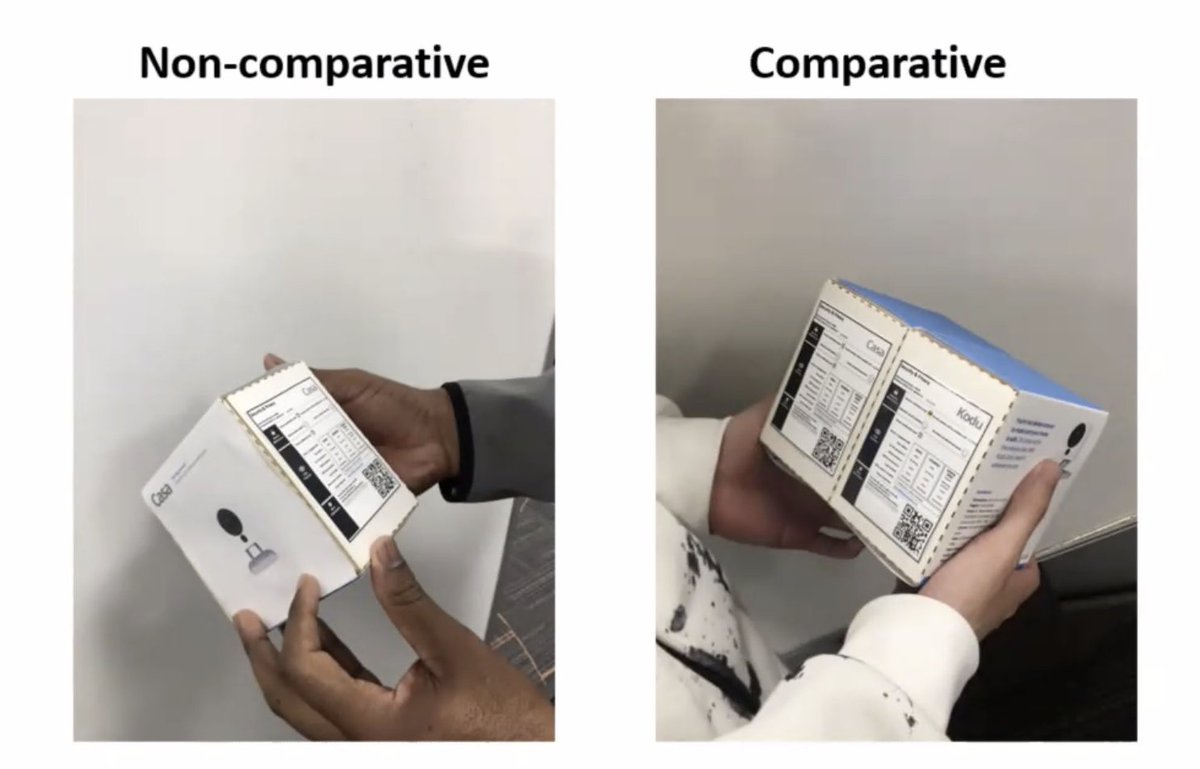
Consumer semi-structured interviews
* non-comparative (hey it's a label) and comparative (which label is better)
* most consumers didn't understand the information but still wanted it
[ ... this doesn't mean they'll use it in practice, of course ]
* non-comparative (hey it's a label) and comparative (which label is better)
* most consumers didn't understand the information but still wanted it
[ ... this doesn't mean they'll use it in practice, of course ]
Labels are not just for normal consumers but also for experts and tech policy folks
Hey, want to be the first adopter of these labels? They want to work with you! There's a tool.
Also, can encourage IoT security and privacy labels to regulators and policy folks.
Demand transparency.
Also, can encourage IoT security and privacy labels to regulators and policy folks.
Demand transparency.
• • •
Missing some Tweet in this thread? You can try to
force a refresh