New: The U.S.' cyber agency is underfunded, overwhelmed, and struggling to keep up with evolving threats.
@CISAgov got $650m in the Covid-19 bill, but experts say it'll need a lot more support to have a chance of stopping the next SolarWinds.
My story: politico.com/news/2021/03/3…
@CISAgov got $650m in the Covid-19 bill, but experts say it'll need a lot more support to have a chance of stopping the next SolarWinds.
My story: politico.com/news/2021/03/3…
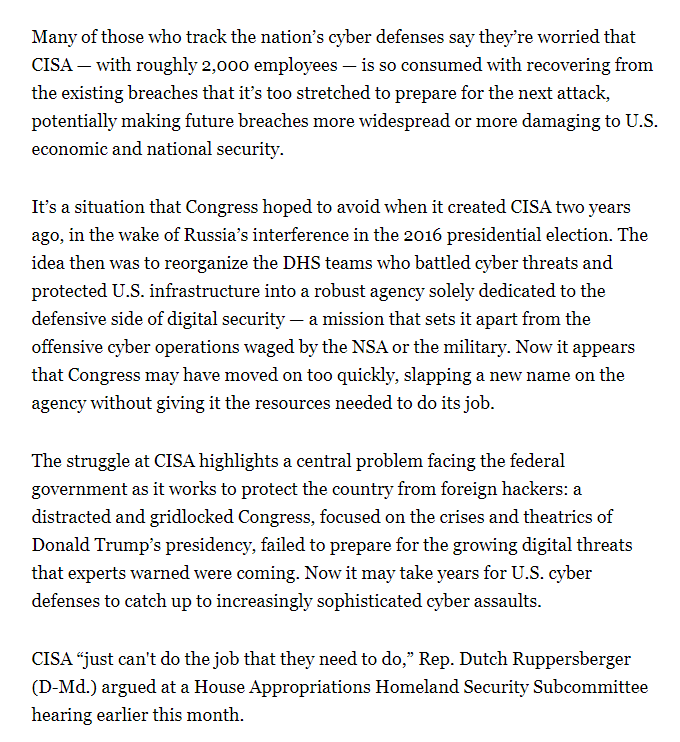
I talked to 15 people familiar with CISA’s work, including 4 current employees and 5 former CISA officials. Some of the problems they described:
* Far too few hunt & incident response teams
* Not enough $ for risk management center
* Not enough data analysis capabilities
* Far too few hunt & incident response teams
* Not enough $ for risk management center
* Not enough data analysis capabilities
Even though many employees are "exhausted," as one put it, they're still optimistic about their agency's future.
They love their mission and hope new Biden admin leadership will get them what they need.
They love their mission and hope new Biden admin leadership will get them what they need.
CISA Cyber Division chief Eric Goldstein, one of those new political appointees, told me that CISA isn't yet "having to make triaging decisions" about what cyber aid to offer, and to whom — but he added that regular funding boosts would ensure that that remains the case.
There's bipartisan support for boosting CISA's budget.
Both @BennieGThompson and @RepJohnKatko told me that CISA needs more money to meet policymakers' expectations.
Both @BennieGThompson and @RepJohnKatko told me that CISA needs more money to meet policymakers' expectations.
One of CISA's biggest problems: its two main programs for monitoring federal networks, CDM and the National Cybersecurity Protection System, are out of date.
They'll need major upgrades to handle novel malware, ubiquitous encryption, cloud services, and identity-based attacks.
They'll need major upgrades to handle novel malware, ubiquitous encryption, cloud services, and identity-based attacks.
CISA is in the process of fixing some of these problems. It's investing in new network sensors and data analysis capabilities so it can spot and understand problems before they blossom into crises.
But it needs more $ & a more mature hiring process to sustain growth & progress.
But it needs more $ & a more mature hiring process to sustain growth & progress.
As @CostelloJK pointed out, CISA has unique advantages. Companies and state/local govts trust it in a way they don't trust NSA/FBI. As a result, it gets unique domestic cyber threat insights.
If it falters, other agencies won't be able to pick up its slack.
If it falters, other agencies won't be able to pick up its slack.
CISA is in a difficult spot.
Its reputation suffers with every major breach it misses — even if it's not realistic to expect it to catch everything; certainly its foreign-focused counterparts don't — and every reputational hit jeopardizes its partners' all-important trust.
Its reputation suffers with every major breach it misses — even if it's not realistic to expect it to catch everything; certainly its foreign-focused counterparts don't — and every reputational hit jeopardizes its partners' all-important trust.
Great question!
One thing I wasn't able to get into my story is that, in the FY21 NDAA, Congress allowed CISA to proactively hunt for threats on other agencies' networks without being invited in.
This should greatly increase their visibility. It was their big recent ask.
One thing I wasn't able to get into my story is that, in the FY21 NDAA, Congress allowed CISA to proactively hunt for threats on other agencies' networks without being invited in.
This should greatly increase their visibility. It was their big recent ask.
https://twitter.com/t3chlaw/status/1376884813345488898
• • •
Missing some Tweet in this thread? You can try to
force a refresh