DHS just wrapped up a background briefing with senior officials on the department's cybersecurity agenda.
Nothing earth-shattering, but I'll share a few comments that stood out to me.
Nothing earth-shattering, but I'll share a few comments that stood out to me.
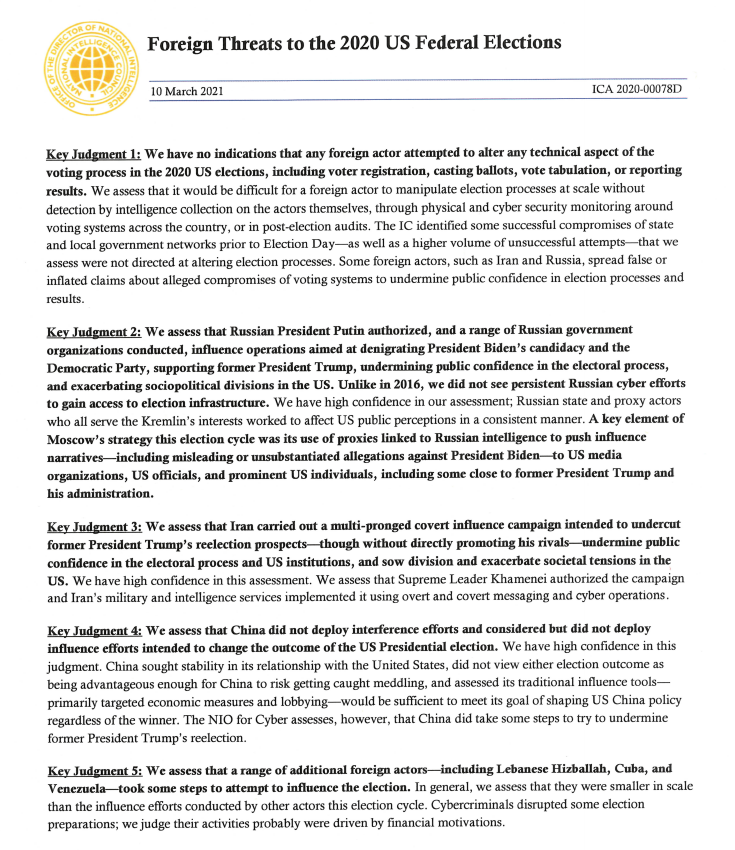
We've previously heard from Anne Neuberger that the Biden administration has an EO coming with mitigations related to the SolarWinds/Exchange vulnerabilities. Today, a senior DHS official told us that it will contain "close to a dozen actions."
DHS Sec Mayorkas will be discussing cyber tomorrow during an RSA event.
Per sr official, he will offer a "comprehensive vision" for using DHS/CISA to defend the country, incl through several "cybersecurity sprints" that he previously teased.
1st sprint will focus on ransomware.
Per sr official, he will offer a "comprehensive vision" for using DHS/CISA to defend the country, incl through several "cybersecurity sprints" that he previously teased.
1st sprint will focus on ransomware.
Not sure if it's b/c they saw my story this morning politico.com/news/2021/03/3… but one senior DHS official was adamant that CISA has enough resources to respond to the requests for help that it's getting right now.
Quote in next tweet.
Quote in next tweet.
“Our capacity remains within the parameters of our demand signal at this point in time," sr official said. "At no point during [SW/Exchange] did CISA need to turn away a compromised entity that was seeking help."
But sr official noted that things could get even worse and that CISA wants to be ready.
"We do have capacity yet to deploy, but recognizing the evolving environment, we want to make sure that we are moving ahead of the point where we may see capacity constraint."
"We do have capacity yet to deploy, but recognizing the evolving environment, we want to make sure that we are moving ahead of the point where we may see capacity constraint."
DHS is in the middle of "an in-depth lessons-learned exercise" about SolarWinds and Exchange that will lead to "a set of recommendations that will guide our work for the administration moving forward," one senior official said.
Unclear how that will overlap with the imminent EO.
Unclear how that will overlap with the imminent EO.
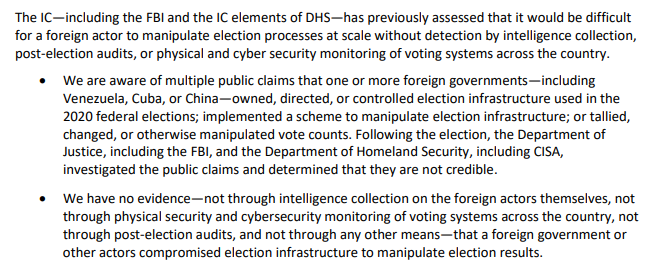
Multiple reporters asked officials for more transparency about the specific impacts of SolarWinds, amid reports of specific Trump Cabinet secretaries being hacked.
Officials declined to get that specific, saying the hackers' exact movements aren't crystal clear.
Officials declined to get that specific, saying the hackers' exact movements aren't crystal clear.
Hacks like this often produce "a level of ambiguity about what a particular adversary accessed or what their intent was," one senior official said, so discussing "impacts as individualized as a given user account would likely be speculative."
"Where possible we do want to make sure that the public understands the impact of a given attack," sr official said, but "it is equally if not more important to convey the strategic view" of the hackers' goals, esp if those goals include "damaging attacks with physical impact."
On the Q of new authorities, the officials said the Biden administration wants to work with Congress "to examine possible options, like mandatory incident reporting in some cases and for some entities," that would help CISA gather the data it needs to assess threats.
• • •
Missing some Tweet in this thread? You can try to
force a refresh