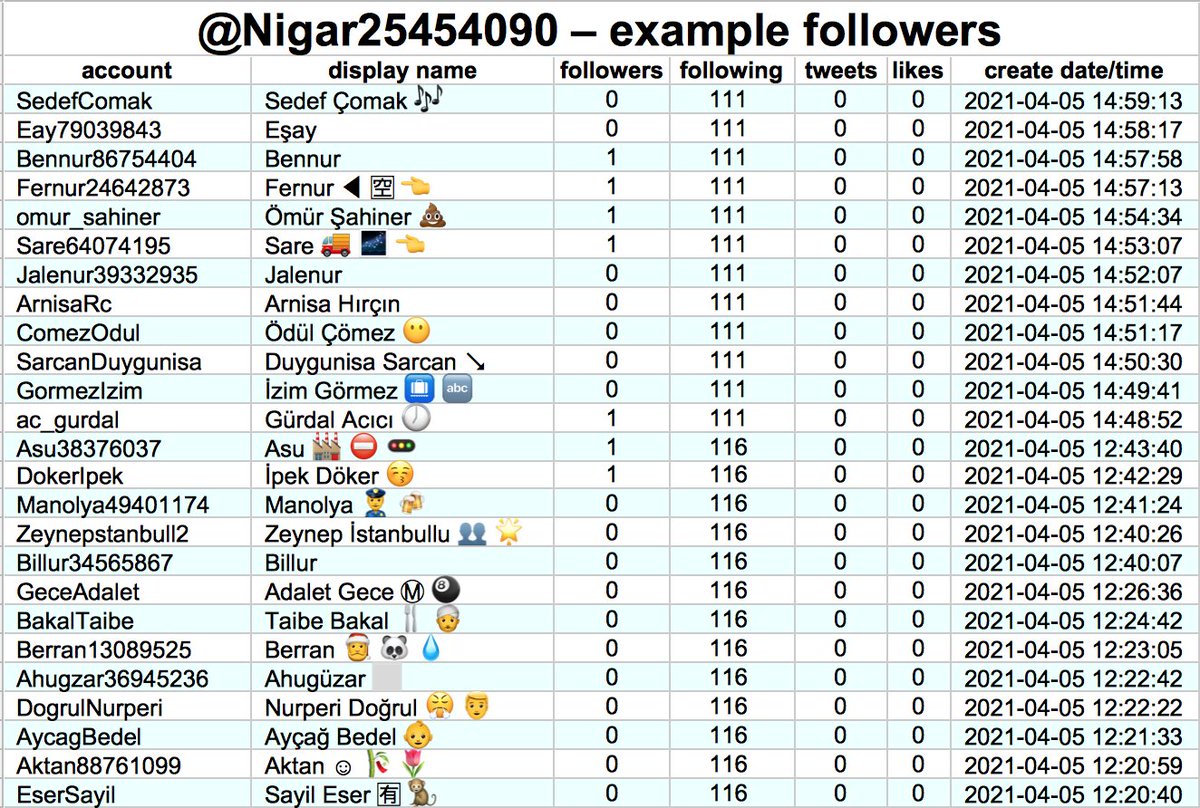
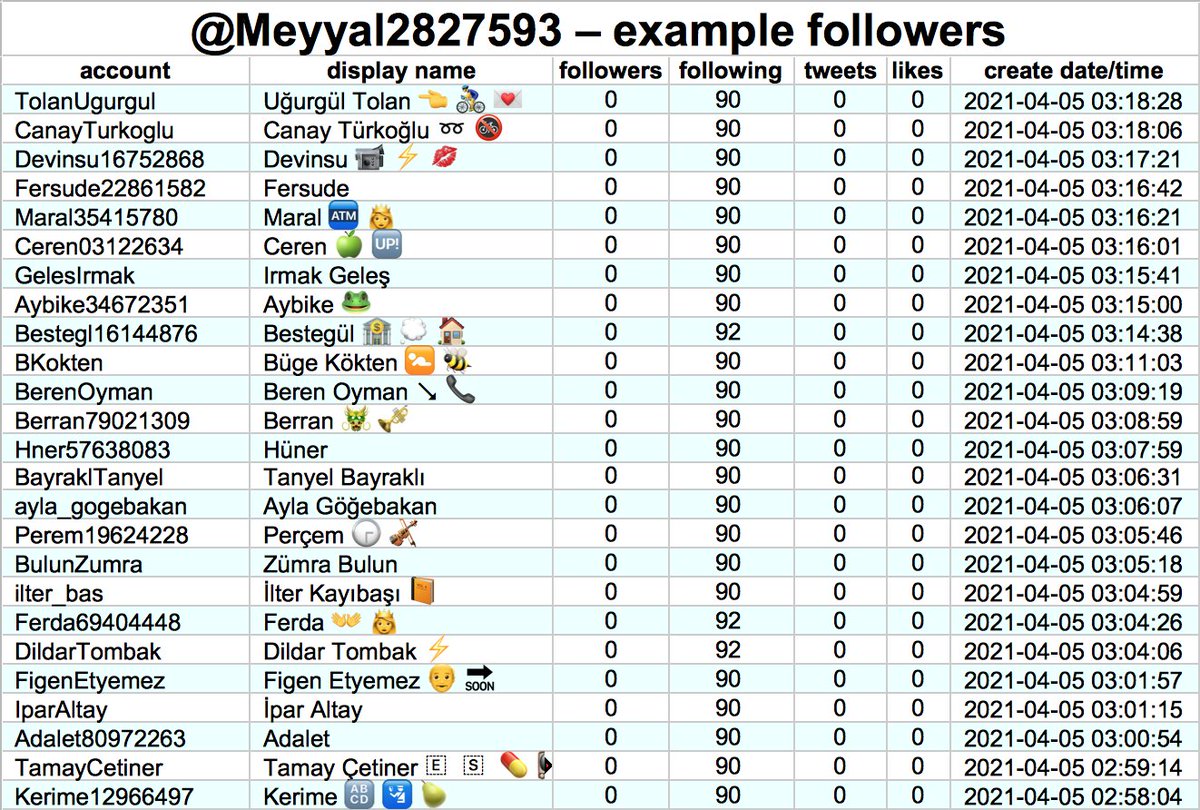
All twelve of these accounts have the same anomalous pattern in their followers: long spans of time post-2019 where nearly all their new followers are accounts created prior to mid-November 2018. What's up with that? #WednesdayWisdom
cc: @ZellaQuixote
cc: @ZellaQuixote
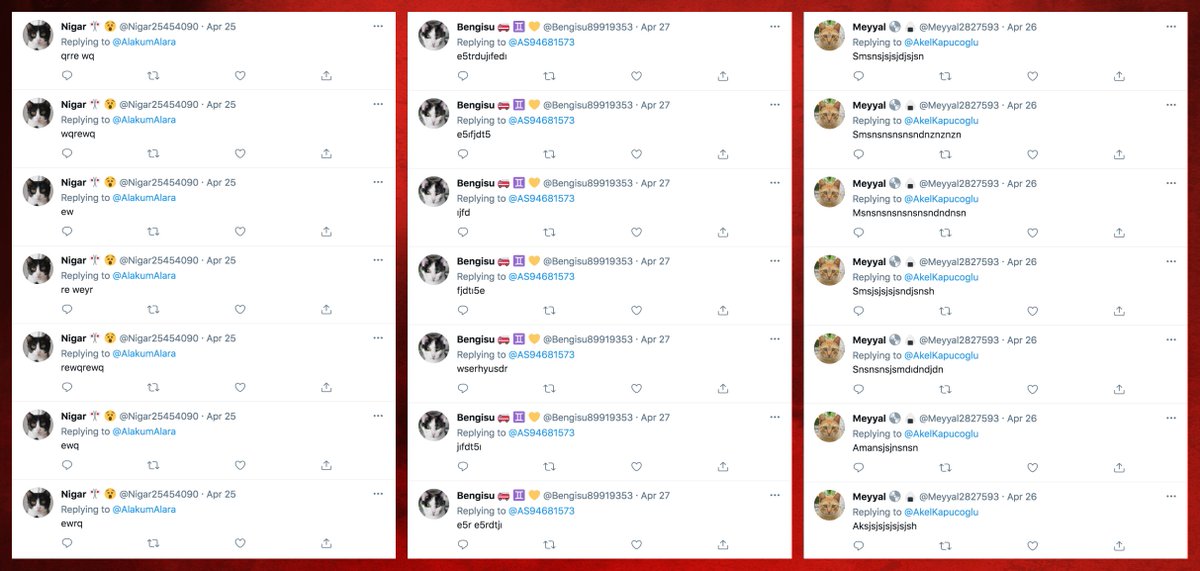
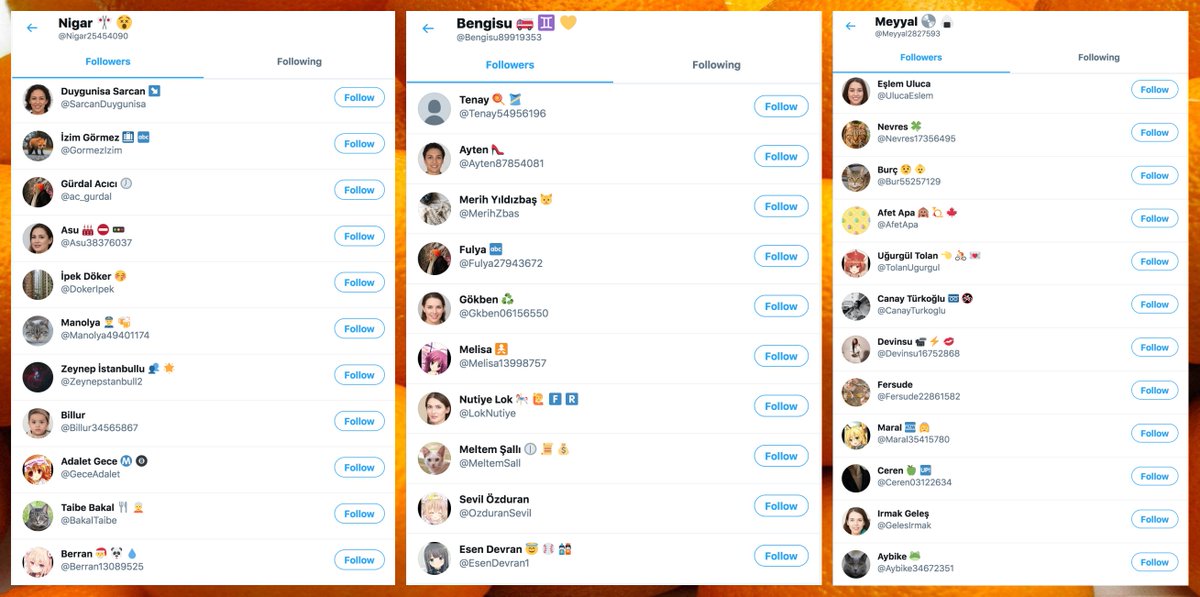
The twelve accounts don't have the same anomalous followers, however, and the anomalous followers in question by and large don't look like batch-created accounts or obvious bots. The twelve accounts do have something in common, however. . .
All twelve accounts are being promoted in Twitter's "who to follow" section. We're not precisely sure why, but there appears to be a correlation between this form of Twitter promotion and accounts mostly gaining followers created before November 2018. 

Note that this pattern, although common, is not universal. We pulled followers for 15 promoted "who to follow" accounts (with at least 10K followers each), and found the anomaly in 12 of them. The remaining 3 looked relatively normal.
• • •
Missing some Tweet in this thread? You can try to
force a refresh