1/5
@Wault_Finance was exploited to extract about $888K “profit” for the attacker (370 ETH). Here is the related tx: bscscan.com/tx/0x31262f15a…
@Wault_Finance was exploited to extract about $888K “profit” for the attacker (370 ETH). Here is the related tx: bscscan.com/tx/0x31262f15a…
2/5
The hack is similar to an earlier yDAI hack: the stake() function has a flaw that can be forced to swap from USDT to WEX via the related USDT_WEX pair, even when the pair has been manipulated to be highly imbalanced. peckshield.medium.com/the-ydai-incid…
The hack is similar to an earlier yDAI hack: the stake() function has a flaw that can be forced to swap from USDT to WEX via the related USDT_WEX pair, even when the pair has been manipulated to be highly imbalanced. peckshield.medium.com/the-ydai-incid…
3/5
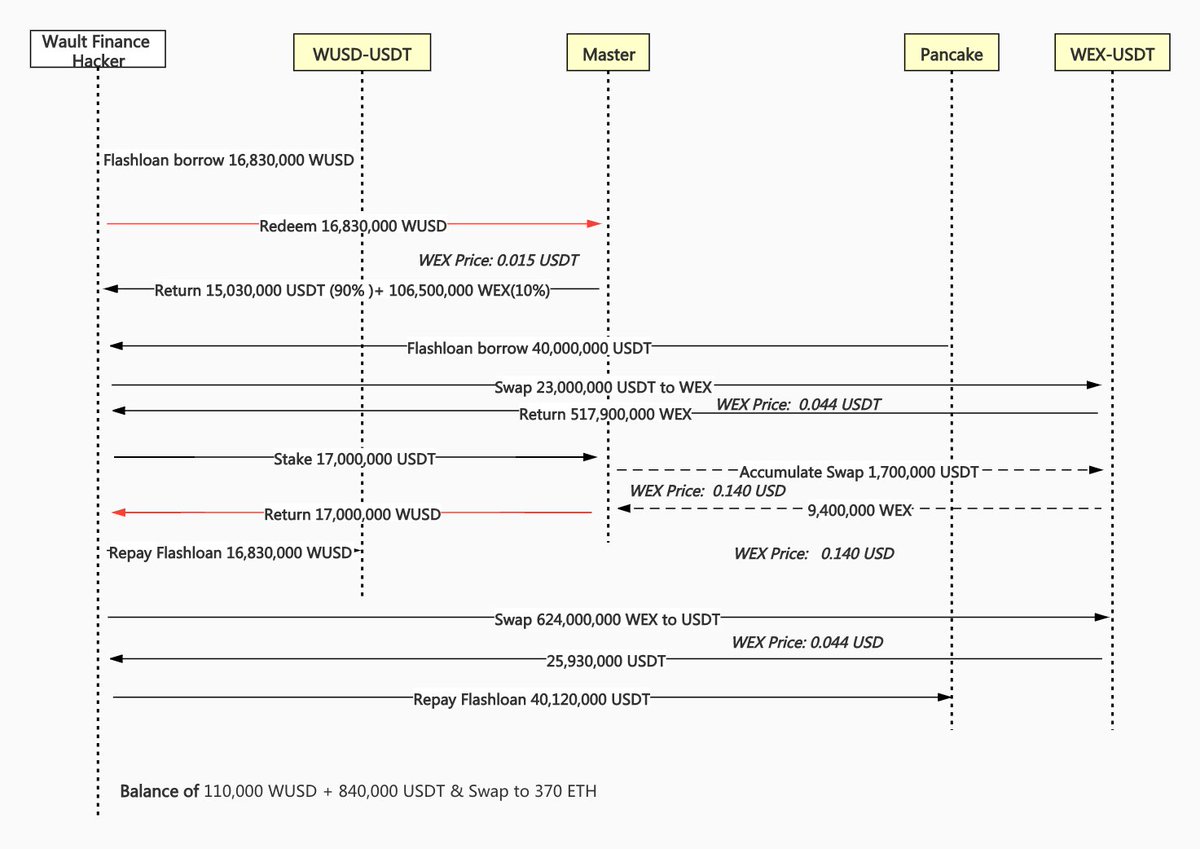
In the exploit, the hacker makes the first flashloan of 16M WUSD (and redeems the WUSD to 15M USDT and 106M WEX), then the second flashloan of another 40M USDT, and swaps 23M USDT to 518M WEX, resulting in an imbalanced USDT_WEX pair.
In the exploit, the hacker makes the first flashloan of 16M WUSD (and redeems the WUSD to 15M USDT and 106M WEX), then the second flashloan of another 40M USDT, and swaps 23M USDT to 518M WEX, resulting in an imbalanced USDT_WEX pair.
4/5
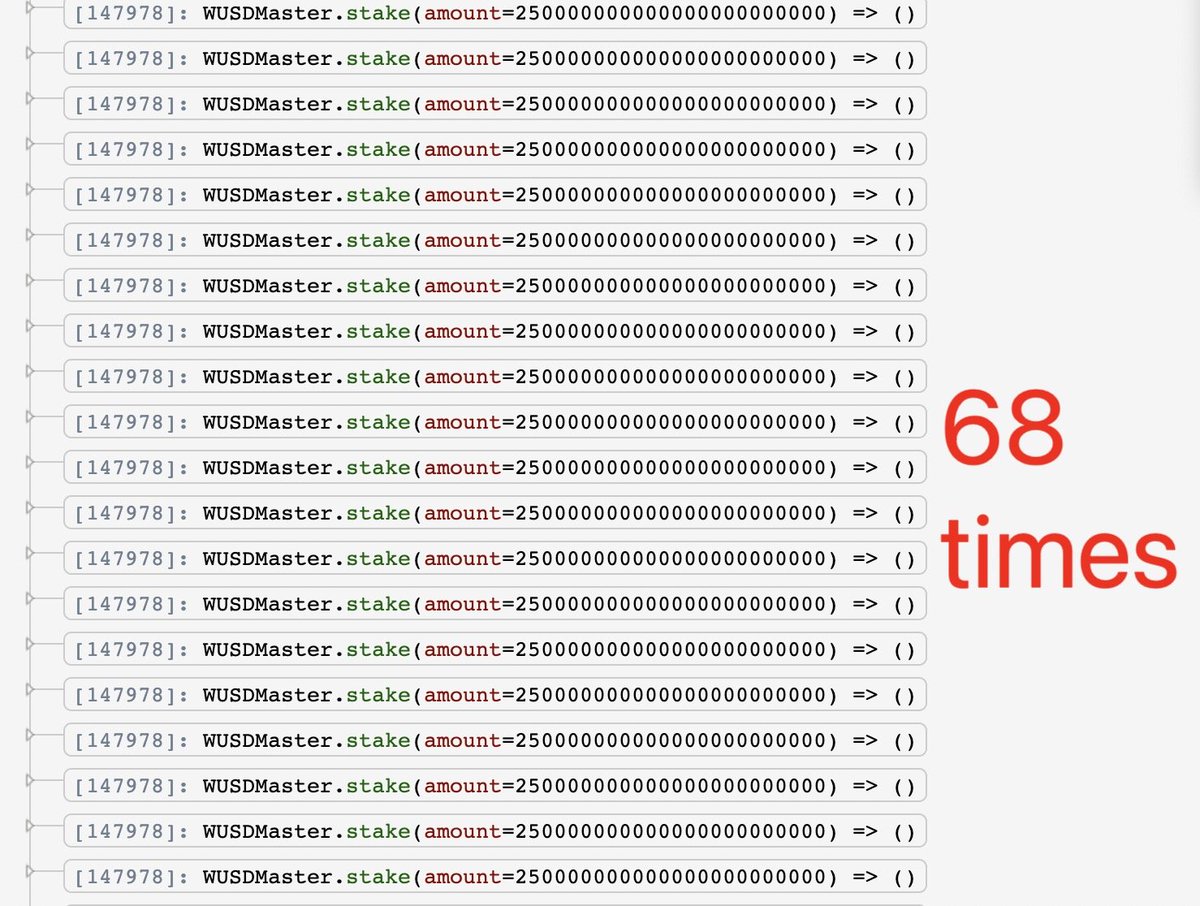
The attacker repeats stake() 68 times. Each time the WUSDMaster is coded (forced) to swap 10% of the staked USDT (250K) into WEX via the imbalanced USDT_WEX pair, which becomes even skewed. At the end, the attacker makes a reverse swap from WEX to USDT for profit.
The attacker repeats stake() 68 times. Each time the WUSDMaster is coded (forced) to swap 10% of the staked USDT (250K) into WEX via the imbalanced USDT_WEX pair, which becomes even skewed. At the end, the attacker makes a reverse swap from WEX to USDT for profit.
5/5
Overall, the attacker makes a profit of 370.19 ETH (~$888K), which is immediately transferred from @BinanceChain to @ethereum (0xf9E3D08196F76f5078882d98941b71C0884BEa52) via @Anyswap. We are actively monitoring this address for any movement.
Overall, the attacker makes a profit of 370.19 ETH (~$888K), which is immediately transferred from @BinanceChain to @ethereum (0xf9E3D08196F76f5078882d98941b71C0884BEa52) via @Anyswap. We are actively monitoring this address for any movement.
2/5
The hack is similar to an earlier yDAI hack: the stake() function has a flaw that can be forced to swap from USDT to WEX via the related USDT_WEX pair, even when the pair has been manipulated to be highly imbalanced.
The hack is similar to an earlier yDAI hack: the stake() function has a flaw that can be forced to swap from USDT to WEX via the related USDT_WEX pair, even when the pair has been manipulated to be highly imbalanced.
• • •
Missing some Tweet in this thread? You can try to
force a refresh