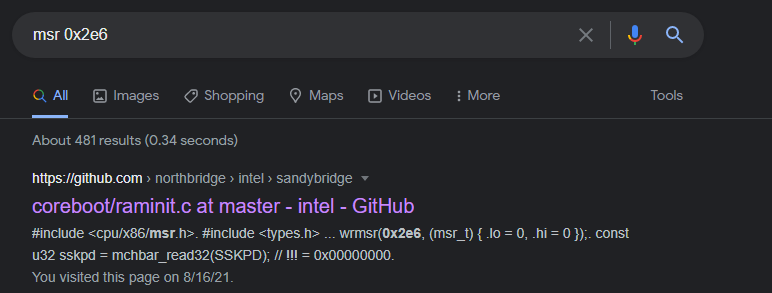
Broadwell seems to have a fun undocumented MSR 😛
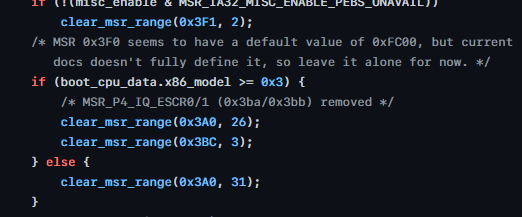
0x3F0, doesn't work on Skylake so not architectural, write-protected, seems to be 1 only on the CPU #0. Only mention seems to be in XEN, doesn't seem to be accurate. 
Thing is, as trivial and innocent as it is, stuff like this opens up detection vectors for virtualization based sandboxes. Running on a Broadwell? Switch to first core, read 3F0 in a loop for a few seconds, if it ever returns 0 or faults, you're in a VM, congrats. ¯\_(ツ)_/¯
Not that there aren't a thousand other easier methods, but you get the point.
• • •
Missing some Tweet in this thread? You can try to
force a refresh