How to check iOS devices for signs of CVE-2021-30860 / FORCEDENTRY exploitation (for context, see @citizenlab's 13.09.2021 blog). #nso #pegasus #malware #ios
Make an unencrypted iTunes backup, or use MVT (docs.mvt.re/en/latest/inde…) to decrypt an encrypted one. You can also check older backups, if you have them. (it's a good idea to make regular iTunes backups for all your devices, precisely for this reason)
Use DB Browser for SQLite (see sqlitebrowser.org) to open Manifest.db, in the root folder of the iTunes backup. Make sure you open it read-only - "File -> Open Database Read Only".
Once Manifest.db is loaded, go to "Browse Data" and type "Library/SMS/Attachments". You should see something similar to this: 
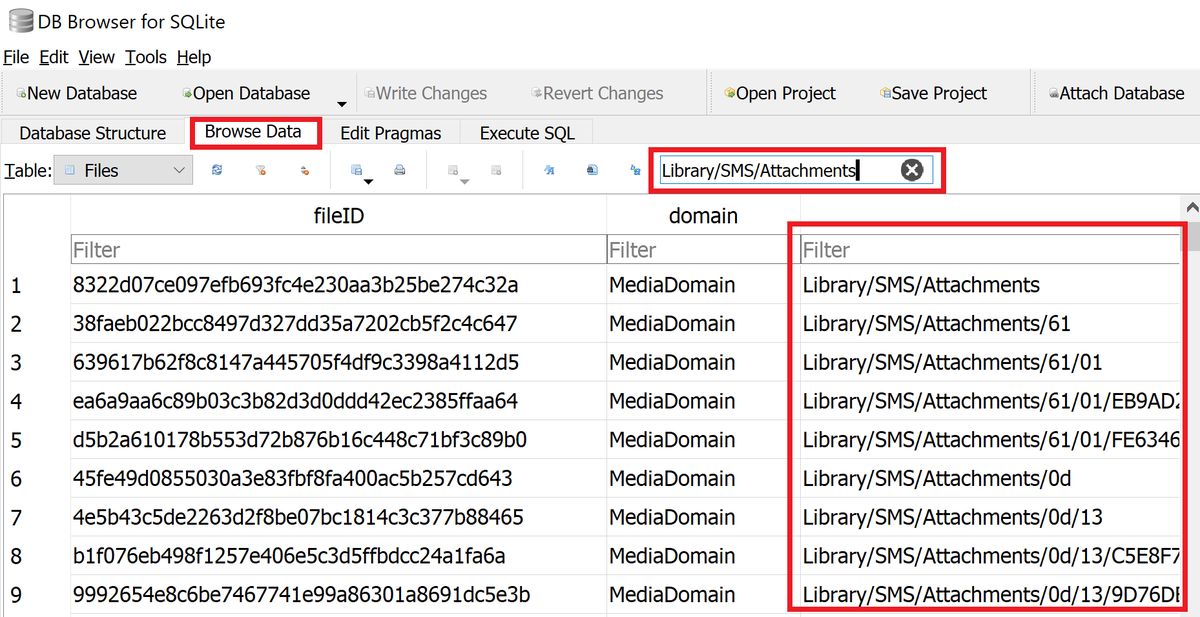
Then, type space (" ") and .gif, to check for any .gif files in "Library/SMS/Attachments". Full search string should be "Library/SMS/Attachments .gif". If you find some hits (.gif files) it's a good idea to check them further to establish maliciousness. DM for details.
According to @citizenlab, the malicious .gif files are actually .PDF and .PSD format. A gif file has a typical "GIF8..." header, like this: 

Last but not least: finding some .gif files in SMS (iMessage) attachments is not a 100% proof that you got targeted - further checks are required to confirm the nature of these files. Also, not finding any files doesn't mean you weren't targeted. Stay vigilant.
And some more generic iOS security tips: reboot your device daily, to remove non-persistent implants. Create regular iTunes backups, to check them later for signs of compromise. Trigger sysdiags regularly and save them.
• • •
Missing some Tweet in this thread? You can try to
force a refresh