Sorry for the drama tweet, but imo it's educational!
Remember the bug bounty Verizon drama? At the time I tried to understand his frustration, but his public information didn't explain the bug well. I reached out in DM to understand more abt the security issue he reported
🧵👇
Remember the bug bounty Verizon drama? At the time I tried to understand his frustration, but his public information didn't explain the bug well. I reached out in DM to understand more abt the security issue he reported
🧵👇

The past few hours I have been in a heated public debate about this again. @jonathandata1 decided to share private messages from me out-of-context and accusing me of being a liar. He also called me "asshole" and "Hillary Clinton ass mother fucker".
https://twitter.com/jonathandata1/status/1441871817023574017
So a tipping point has been reached, where I decided to share our full conversation. You can see our conversation and some of his tweets here:
imgur.com/a/zC0chge
imgur.com/a/zC0chge
I believe the whole issue arises because @jonathandata1 is bad at communicating his findings.
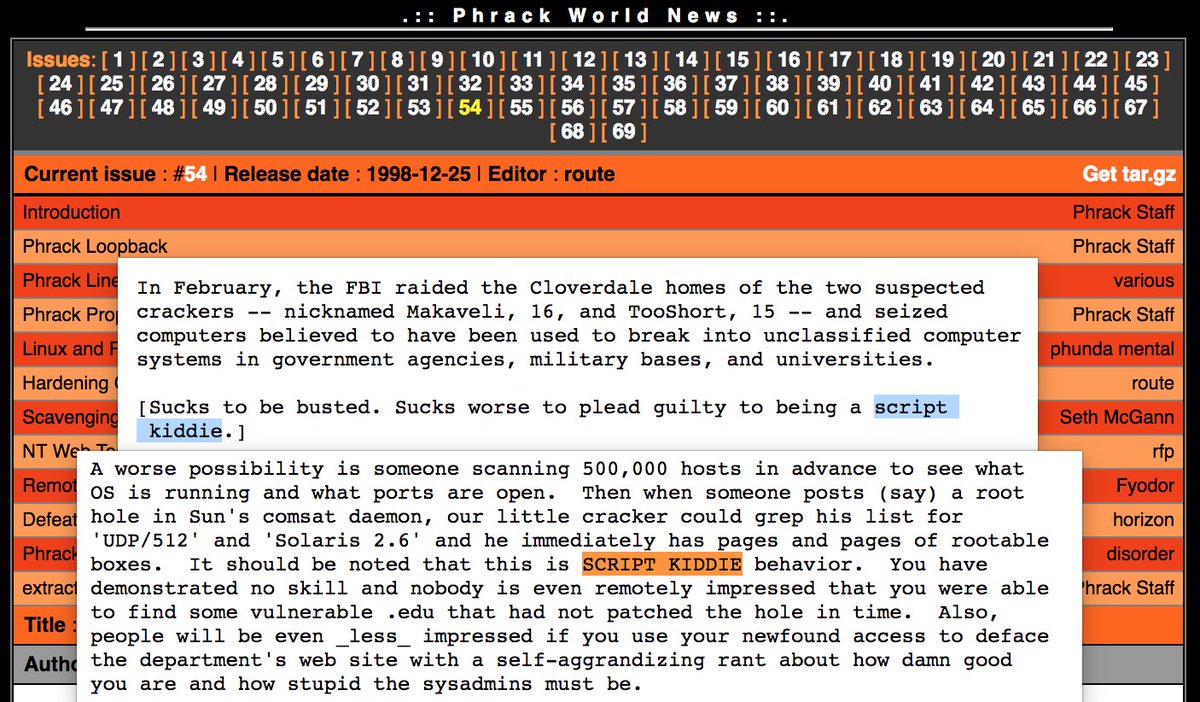
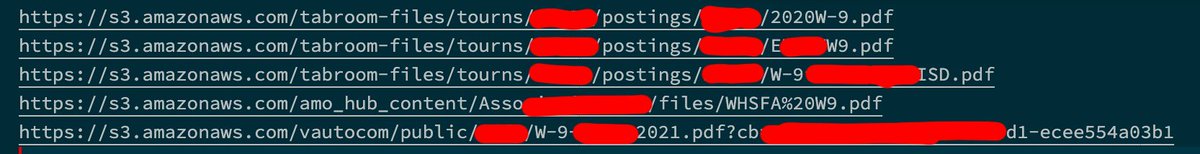
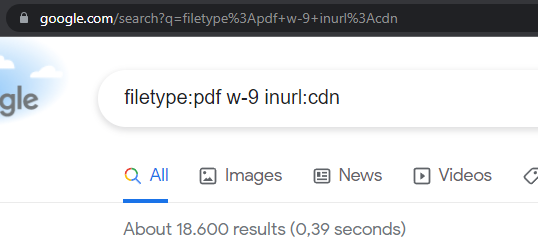
It took me quite a while to understand that he essentially google dorked w-9 forms on a yahoo CDN (this info was not part of his h1 report).
The question is now, who is "leaking" here?
It took me quite a while to understand that he essentially google dorked w-9 forms on a yahoo CDN (this info was not part of his h1 report).
The question is now, who is "leaking" here?
My argument was, when AWS customers upload their w-9 tax form to their s3 bucket, it's not an issue to report to Amazon bug bounty. You would report this s3 customer.
And my claim is that his finding is the same, just on Yahoo CDN. BUT...
And my claim is that his finding is the same, just on Yahoo CDN. BUT...
... the terrible report, explanation, examples, ... from him leave room for interpretation. And this is what makes the whole thing so muddy. Let me do an example where I would give the full benefit of the doubt:
>> Let's say you are a Verizon (Yahoo) customer and you use their CDN. And then Verizon has a backend where they ask for your w-9 form and it gets automatically uploaded to your own CDN publicly reachable and gets indexed by Google. I'd say that is an issue with Yahoo <<
Notice how I was able to explain in one tweet how a valid report could look like?
But his original report, his publicly shared information on GitHub and the personal conversation with me, were not enough to explain what he actually found???
But his original report, his publicly shared information on GitHub and the personal conversation with me, were not enough to explain what he actually found???
That's why I do not believe he actually found a valid security issue. I believe he just google dorked the Yahoo CDN, found some PII (surprise!) and tried to stir up drama after the report was rejected.
Kind of like this
Kind of like this
I COULD BE WRONG! As I said, it's muddy and his lack of clear communication leaves massive room for interpretation. And unfortunately so far he was not willing to share his original h1 report or our conversation publicly. I feel entitled to do the latter.
I think this is a very interesting case to dig deeper into. @jonathandata1 claims the issue has been fixed. So I think it would be beneficial to everybody if he shares all the information about this case. I think he owes it to everybody, after stirring up so much drama about it.
Also I have to mention again, I'm not a huge fan of bug bounties. I generally criticize the exploitation of labor at scale. But for now I'm still standing with @Hacker0x01 and all the triagers that have to dig through piles of crap like this.
But only all of the information is out there, we can finally find the #truth (as Jonathan likes to say). And I'm totally willing to change my position if presented with conclusive evidence. Until then, I stand by my position "most likely not a vulnerability by Verizon".
Long story short, you can get quite the big social media following by shrouding drama in a cloud of confusion so nobody understands anymore what the heck is going on.
• • •
Missing some Tweet in this thread? You can try to
force a refresh