Anyone else seen this and reviewed? Just had a bunch of people point me to it.
https://twitter.com/Sinoc229/status/1445639261974261766
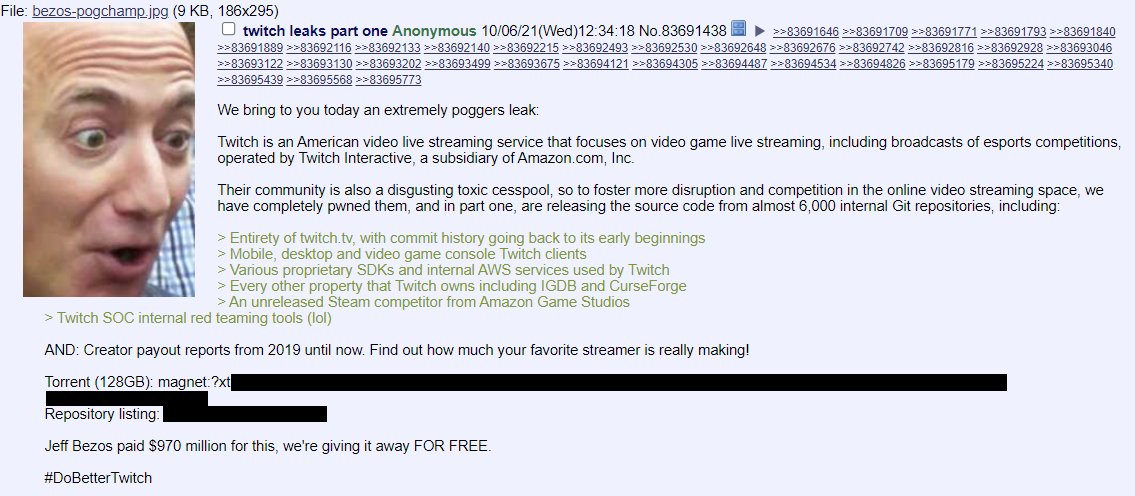
The general consensus from the masses is "it's legit", but I'm yet to see any analysis yet. The torrent is being shared pretty extensively, it contains 278 files totalling 125GB *compressed* so it's sizeable. Here's what's inside: gist.github.com/troyhunt/0770c…
The post containing the torrent claims that Twitch is a "disgusting toxic cesspool". Whether that's motive or a convenient excuse is yet to be seen. 
Possible acknowledgment from Twitch on the legitimacy of this, although nothing official:
https://twitter.com/vgc_news/status/1445679722692710410
And now for some analysis. Thread on the contents of the payout files, certainly looks feasible:
https://twitter.com/KnowS0mething/status/1445651544200781830
Or… maybe not. Need some official commentary from Twitch on this incident:
https://twitter.com/Rimmy_Downunder/status/1445680780995280901
Corrected data and confirmation from a streamer:
https://twitter.com/rimmy_downunder/status/1445695639283658752
And another one:
https://twitter.com/BigJon06/status/1445699831666675723
Looking more and more legit by the minute:
https://twitter.com/tehmorag/status/1445705291077619715
Can anyone confirm if email addresses are present? Including mine 😭
https://twitter.com/tehmorag/status/1445705291077619715
“The Twitch leak is legit” (but apparently doesn’t contain personal data… yet)
https://twitter.com/tomwarren/status/1445710439309062147
This is what’s been bugging me too; obtaining source is one thing, pulling data is quite another (unless keys in source provide access to data…):
https://twitter.com/miraclesec/status/1445719983342948352
While I was sleeping, confirmation from @twitch:
https://twitter.com/twitch/status/1445770441176469512
Echoing @campuscodi’s tweet - if you know where hashes are, DM me. Obviously there’s a huge amount of interest in this right now and if user accounts are in there, I know many people will want to check them in @haveibeenpwned as soon as they can:
https://twitter.com/campuscodi/status/1445746474948562956
And if you’ve not already done so, subscribe here and I’ll send you an email as soon as any data with your address is loaded: haveibeenpwned.com/NotifyMe
I’m hearing about a “part 2” containing email addresses, but I’m yet to see anything to substantiate its presence:
https://twitter.com/backyaro/status/1445726599123439617
Twitch stored passwords in a pretty familiar fashion. Plenty of other services have taken the same approach (such as Dropbox, which we know from their breach), but it leaves a huge number of passwords exposed with the weak hashing algorithm. Wonder if we’ll see how many…
https://twitter.com/chriseng/status/1445834501184229377
Well that didn’t take long. Dedicated website reporting on earnings by Twitch streamer: twitchearnings.com
If you created your Twitch account 6 years ago or more and haven’t changed your password since, there’s a pretty solid chance someone else will change it for you if hashes are released:
https://twitter.com/chriseng/status/1445845944742727682
Found *some* email addresses in this breach. Only 2,455 of them contained in a phpBB3 backups folder. Very old (most recent is Dec 2009), let's see what else turns up. 

Like pretty much every other major tech platform, Twitch reviews data breaches and compares to their own user base to identify accounts with reused credentials:
https://twitter.com/cyberyooks/status/1445859981148962822
• • •
Missing some Tweet in this thread? You can try to
force a refresh