1/ So I went and reviewed some of the internal documents for Solchicks
Here are some of the funniest things I found
(Yes the project is that bad)
Here are some of the funniest things I found
(Yes the project is that bad)
2/ Here they admit to “buying-fake-twitter-followers” and you also can see other promos they’ve paid for 

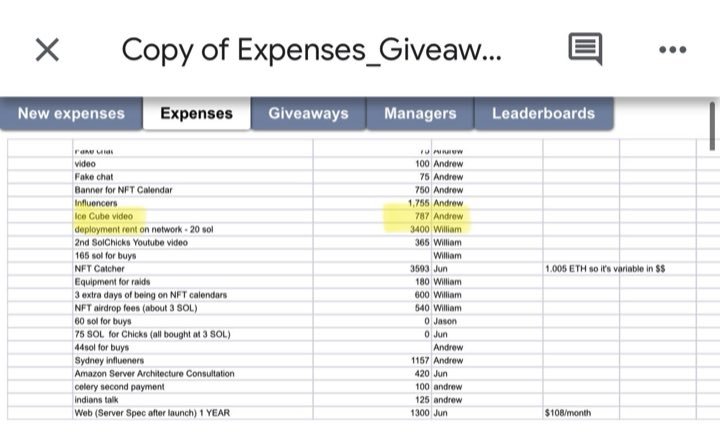
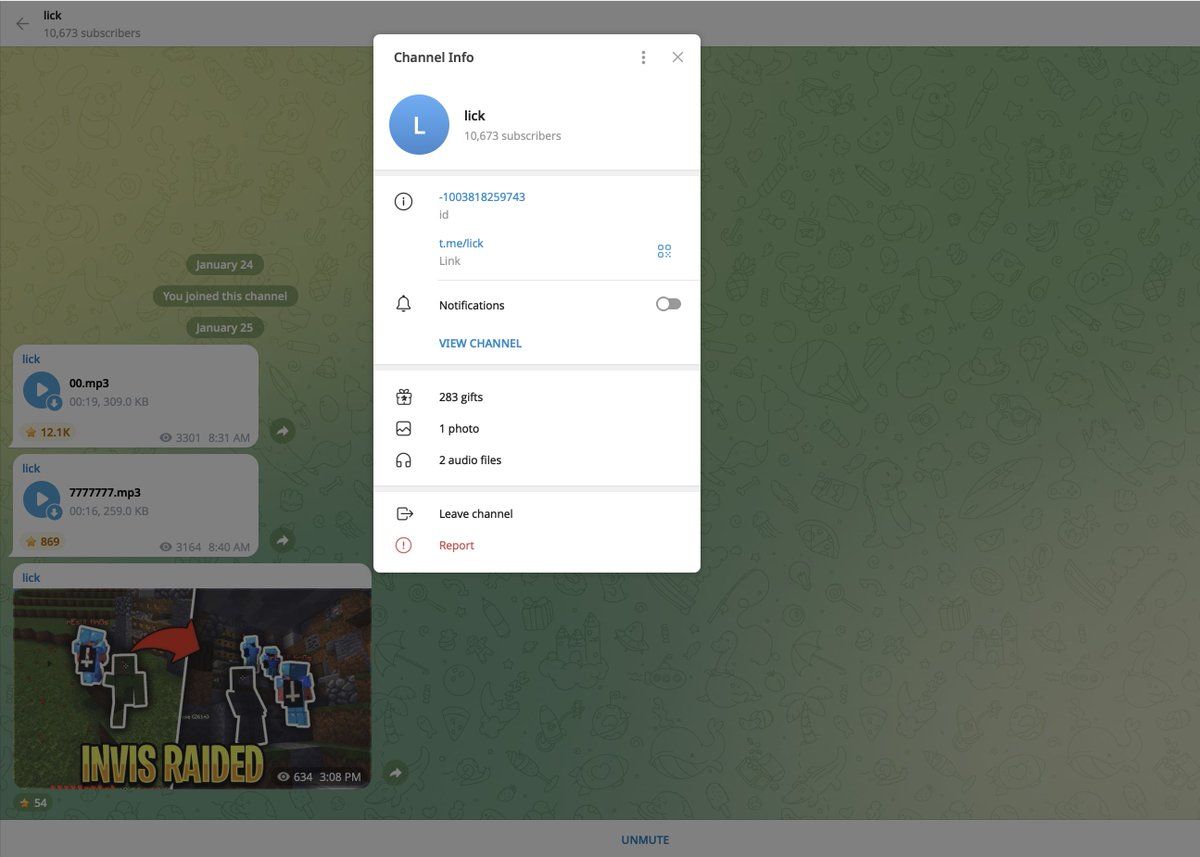
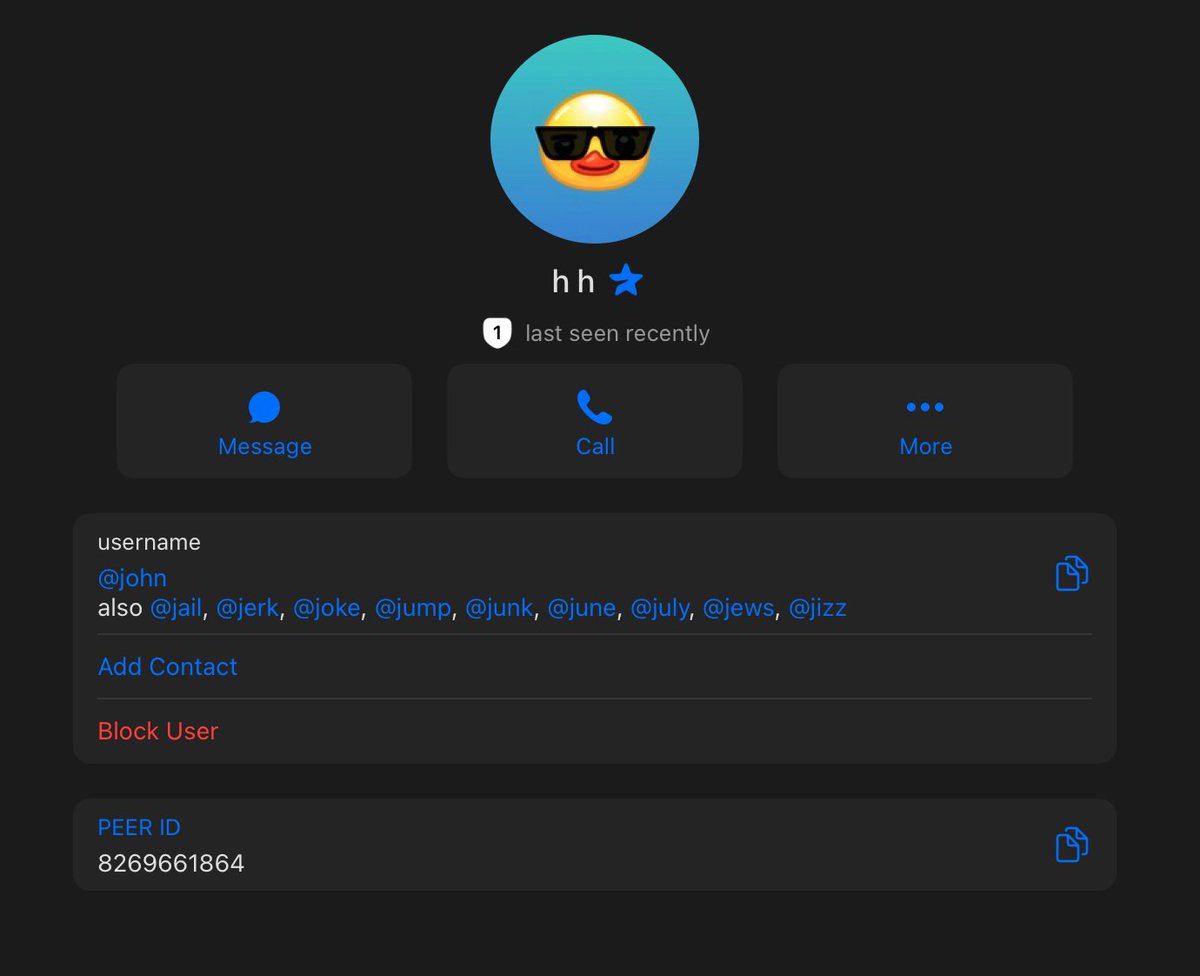
6/ Buying undisclosed shills from random botted accounts.
Luciano deleted his but I went to the archive website to grab it kek (imagine selling yourself for 1.5 bnb)
Doesn’t seem they ended up using all of them


Luciano deleted his but I went to the archive website to grab it kek (imagine selling yourself for 1.5 bnb)
Doesn’t seem they ended up using all of them



10/ If you haven’t figured out already from all the fake engagement yes this project is a candidate for the most overvalued garbage we’ve seen this bull run 



• • •
Missing some Tweet in this thread? You can try to
force a refresh