
Julie Zhou's, "The Making of a Manager" had a big impact about how I think about management.
One of the key lessons is that managers should focus on three areas to achieve a high multiplier effect: purpose, people, and process.
Let's apply that lesson to make a #SOC manager..
One of the key lessons is that managers should focus on three areas to achieve a high multiplier effect: purpose, people, and process.
Let's apply that lesson to make a #SOC manager..
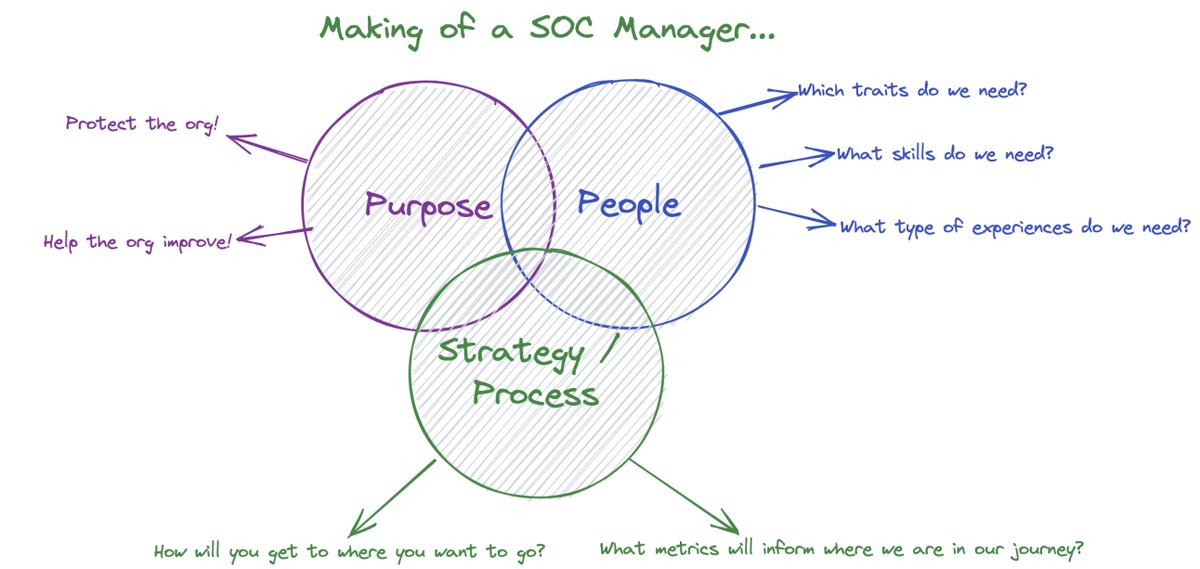
Purpose: Be clear with your team about what success looks like - and create a team and culture that guides you there. Go through the exercise of articulating your teams purpose.
The "purpose" we've aligned on at Expel in our SOC: protect our customers and help them improve.
The "purpose" we've aligned on at Expel in our SOC: protect our customers and help them improve.
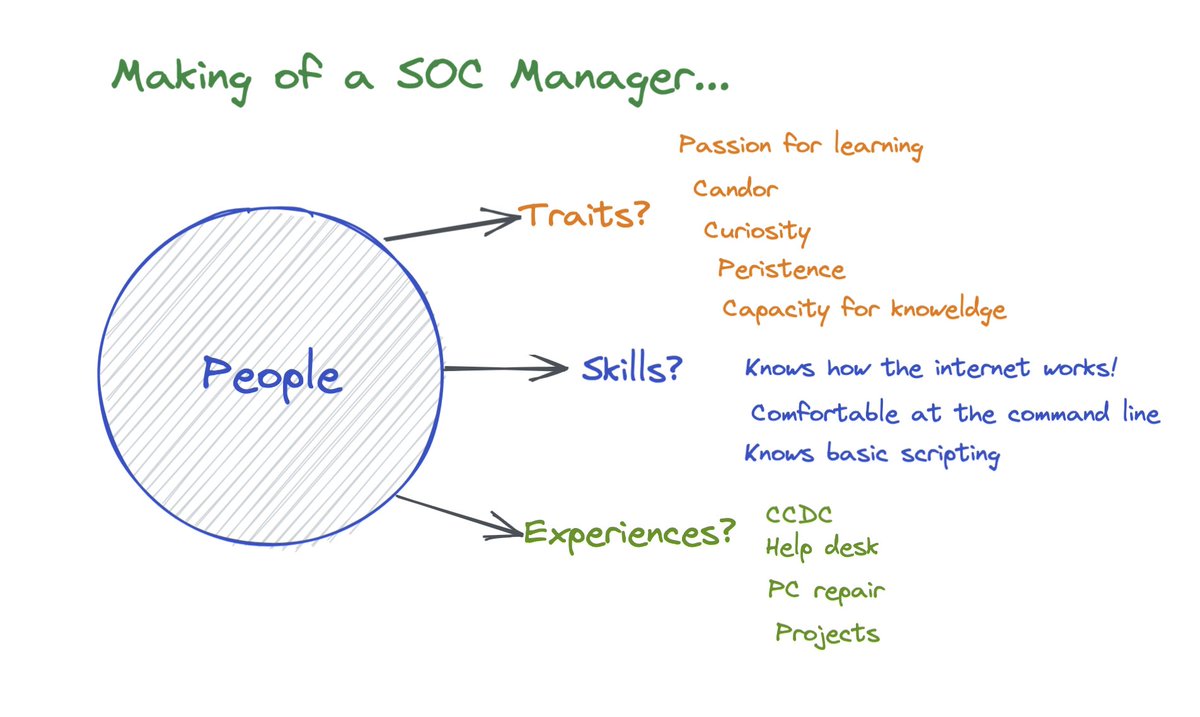
People: To get to where you want to go, what are the traits, skills, and experiences you need to be successful?
Traits (who you are)
Skills (what you know)
Experiences (what you've encountered/accomplished)
When we hire new SOC analysts, traits >> skills.
Traits (who you are)
Skills (what you know)
Experiences (what you've encountered/accomplished)
When we hire new SOC analysts, traits >> skills.
Process: How will you get to where you want to go? What do we need to do to achieve our outcome? And what metrics will inform us where we our in our journey?
Remember, to always keep your purpose in mind. And process !=bureaucracy. It's learning + iterating again and again.
Remember, to always keep your purpose in mind. And process !=bureaucracy. It's learning + iterating again and again.

• • •
Missing some Tweet in this thread? You can try to
force a refresh





