We've been tracking DEV-0537 since 2021 (overlaps: Lapsus$, UNC3661). Here's a comprehensive 🆕 BLOG 📰 covering observed TTPs: microsoft.com/security/blog/…
#MSTIC and Defender threat intel collab
➕#DART 👻 incident response team experience from the trenches [1/3]
#MSTIC and Defender threat intel collab
➕#DART 👻 incident response team experience from the trenches [1/3]
The blog highlights varied initial access vectors and a slew of [inconsistent?] end goals: data theft, extortion, chaos...
One way to interpret "this actor's TTPs and infrastructure are constantly changing" is that they are loosely-organized (see:

One way to interpret "this actor's TTPs and infrastructure are constantly changing" is that they are loosely-organized (see:
https://twitter.com/ItsReallyNick/status/1394483035156983808) [2/3]
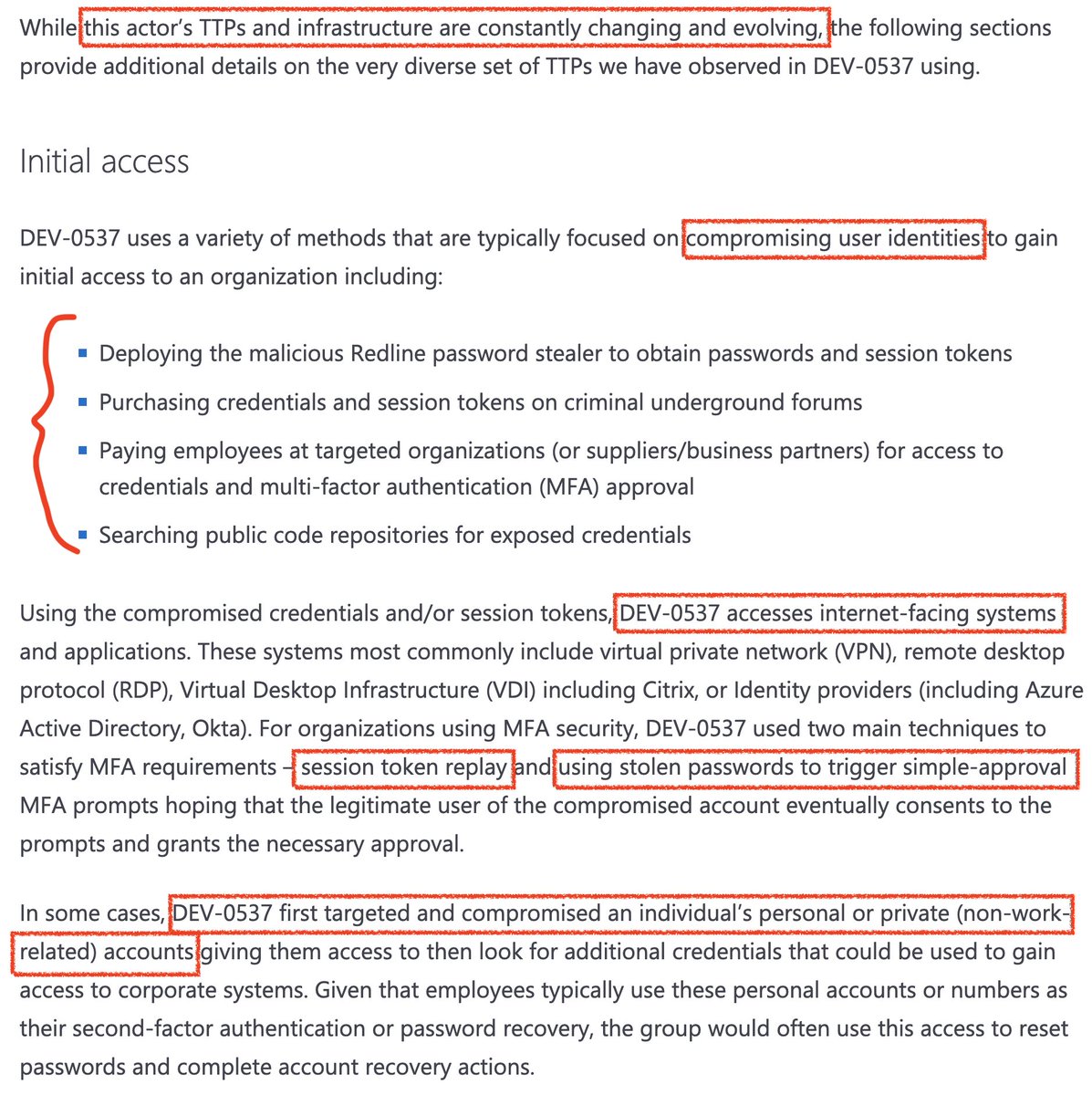

DEV-0537 / Lapsus$ shows that 𝘢𝘵𝘵𝘢𝘤𝘬𝘦𝘳𝘴 can be creative opportunists and still be successful.
Luckily, the same goes for 𝘥𝘦𝘧𝘦𝘯𝘥𝘦𝘳𝘴.
Use this opportunity to strengthen your security controls to protect far beyond this threat actor [3/3] microsoft.com/security/blog/…

Luckily, the same goes for 𝘥𝘦𝘧𝘦𝘯𝘥𝘦𝘳𝘴.
Use this opportunity to strengthen your security controls to protect far beyond this threat actor [3/3] microsoft.com/security/blog/…


Many specific techniques shared if you read closely enough. For example, this DEV-0537 behavior:
• New-TransportRule
• BlindCopyTo
Was new to me, but we all benefit from community contributions.
#MicrosoftSentinel detection added by @duzlov in May 2020: github.com/Azure/Azure-Se…

• New-TransportRule
• BlindCopyTo
Was new to me, but we all benefit from community contributions.
#MicrosoftSentinel detection added by @duzlov in May 2020: github.com/Azure/Azure-Se…


• • •
Missing some Tweet in this thread? You can try to
force a refresh