
1/ Another day, another Sin.
Today's #3: Ignoring or misinterpreting AV alerts.
If I had received a dime for every time I mentioned Florian's cheat sheet, I wouldn't have to work anymore. 😂
🧵 #CyberSecurity
Today's #3: Ignoring or misinterpreting AV alerts.
If I had received a dime for every time I mentioned Florian's cheat sheet, I wouldn't have to work anymore. 😂
🧵 #CyberSecurity
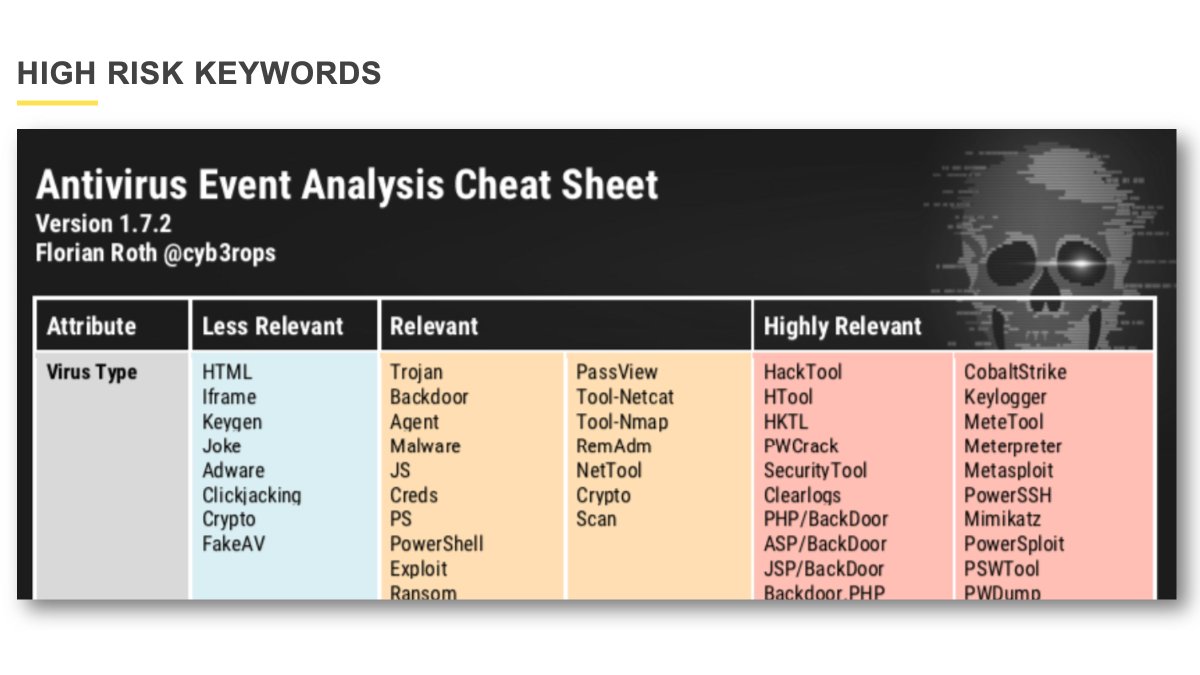
2/ Seriously: The cheat sheet is excellent, especially the part with the "Highly Relevant" keywords.
Newest version here:
nextron-systems.com/2022/02/06/ant…
Newest version here:
nextron-systems.com/2022/02/06/ant…
3/ For example, the following text in the picture below was sent from an external SOC to a customer. According to Windows Defender, among other things, Mimikatz was detected.
On a DC.
But Defender can handle it on its own.
Please run a full scan.
On a DC.
But Defender can handle it on its own.
Please run a full scan.

4/ OK.
5/ If the alert occurs on a server (or DC!) under a path that is also relevant (according to the cheat sheet), I tell my customers not to think twice and call an IR company for a deeper analysis (if they don't have the in-house resources).
6/ Another example: These alerts stem from a client - but the client was restaged without a forensic investigation. 

7/ But if CS is detected on a computer, at least in my opinion, a deeper analysis is necessary to see if a lateral movement originating from this computer has already taken place, if credentials or other data have been stolen, collect further IOCs and check them in the network...
8/ The quick re-installation of a computer destroys significant traces that are enormously important for forensics or hunting in the network.
AV alarms, in particular, can be a warning sign that a TA is active inside the network, as we repeatedly see in our IR cases.
🍀
AV alarms, in particular, can be a warning sign that a TA is active inside the network, as we repeatedly see in our IR cases.
🍀
• • •
Missing some Tweet in this thread? You can try to
force a refresh











