1\ #ThreatHunting for APT abuse of Exchange
APT Exchange abuse has been a common theme with techniques ranging from:
> Compiled DLL OWA backdoors
> .req webshells
> EWS / Legacy auth abuse
> Log / File deletion
TL;DR below or check out the full blog 👇👇
inversecos.com/2022/07/huntin…
APT Exchange abuse has been a common theme with techniques ranging from:
> Compiled DLL OWA backdoors
> .req webshells
> EWS / Legacy auth abuse
> Log / File deletion
TL;DR below or check out the full blog 👇👇
inversecos.com/2022/07/huntin…

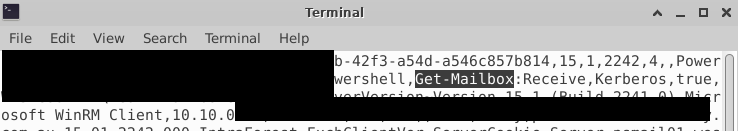
2\ EWS and other legacy auth is commonly abused by APT groups (when enabled).
Check MSExchange Management.evtx log for EWS abuse.
Look for cmdlets like (more cmdlets in blog)
> New-MailboxExportRequest
> Remove-MailboxExportRequest
> Search-Mailbox
> Set-Mailbox
Check MSExchange Management.evtx log for EWS abuse.
Look for cmdlets like (more cmdlets in blog)
> New-MailboxExportRequest
> Remove-MailboxExportRequest
> Search-Mailbox
> Set-Mailbox

3\ Hunt IIS logs in Exchange for:
> Exploitation of unpatched vuln
> Webshell/owa backdoors being used
> Exfil
I've noted across engagements this happens in chunks via several extensions 7Z, TAR, RAR, PST, OST, CAB, ZIP). APTs will use several diff file types on one engagement
> Exploitation of unpatched vuln
> Webshell/owa backdoors being used
> Exfil
I've noted across engagements this happens in chunks via several extensions 7Z, TAR, RAR, PST, OST, CAB, ZIP). APTs will use several diff file types on one engagement

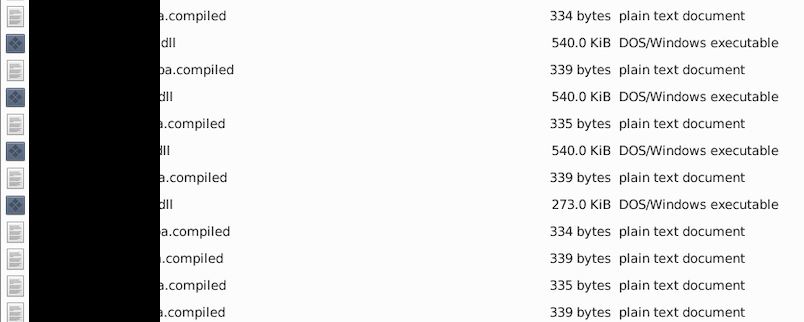
4\ Webshells can be compiled into a DLL or have aspx / req extension. They can also be injected into existing files.
Compilation can create a .compiled file in:
\Windows\Microsoft.NET\Framework64\<ver>\Temporary ASP.NET Files\root\<vers>\<ver>\
Compilation can create a .compiled file in:
\Windows\Microsoft.NET\Framework64\<ver>\Temporary ASP.NET Files\root\<vers>\<ver>\
5\ Webshell locations (more listed in blog):
C:\inetpub\wwwroot\aspnet_client\
C:\inetpub\wwwroot\aspnet_client\system_web\
C:\Program Files\Microsoft\Exchange Server\<vers>\ClientAccess\owa\bin\
C:\Program Files\Microsoft\Exchange Server\<vers>\ClientAccess\owa\auth\
C:\inetpub\wwwroot\aspnet_client\
C:\inetpub\wwwroot\aspnet_client\system_web\
C:\Program Files\Microsoft\Exchange Server\<vers>\ClientAccess\owa\bin\
C:\Program Files\Microsoft\Exchange Server\<vers>\ClientAccess\owa\auth\
6\ APTs can also modify the web config file located at:
C:\inetpub\wwwroot\web.config
This is commonly done to enable settings for OWA & other configuration changes
C:\inetpub\wwwroot\web.config
This is commonly done to enable settings for OWA & other configuration changes
7\ Review other critical logs on Exchange like:
> MAPI
> EWS
> CAS (logs Activesync and OWA)
> PowerShell http logs (logs the cmdlets issued)
C:/Program Files/Microsoft/Exchange/<ver>/Logging/HttpProxy/<name above>
> MAPI
> EWS
> CAS (logs Activesync and OWA)
> PowerShell http logs (logs the cmdlets issued)
C:/Program Files/Microsoft/Exchange/<ver>/Logging/HttpProxy/<name above>
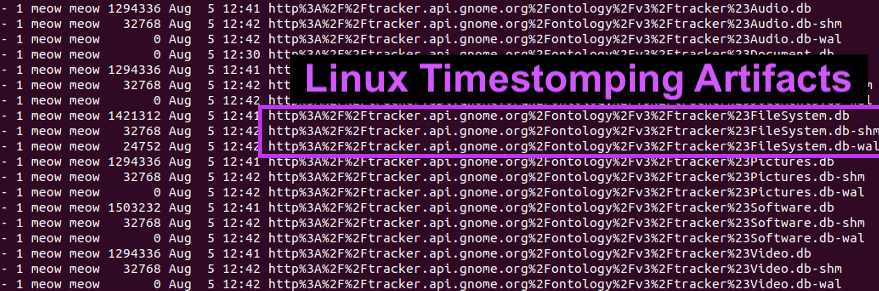
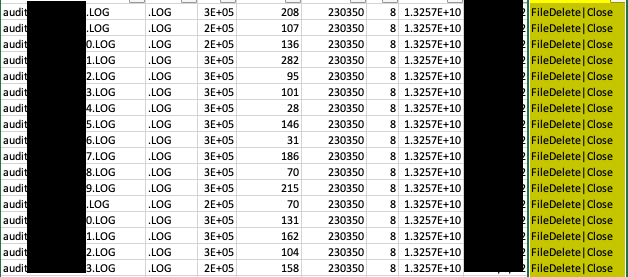
8\ APT file deletion happens all the time.
In one case, the APT deleted 4k various logs including IIS, PowerShell http and other important things.
Webshell deletion/deletion of attack tools etc is all common practice.
Make sure you parse the $J for this.
In one case, the APT deleted 4k various logs including IIS, PowerShell http and other important things.
Webshell deletion/deletion of attack tools etc is all common practice.
Make sure you parse the $J for this.
9\ I will add more hunting areas you can look at to this blog, as I have thought of a few more things but I ran out of time T_T But I hope this helps <3
• • •
Missing some Tweet in this thread? You can try to
force a refresh