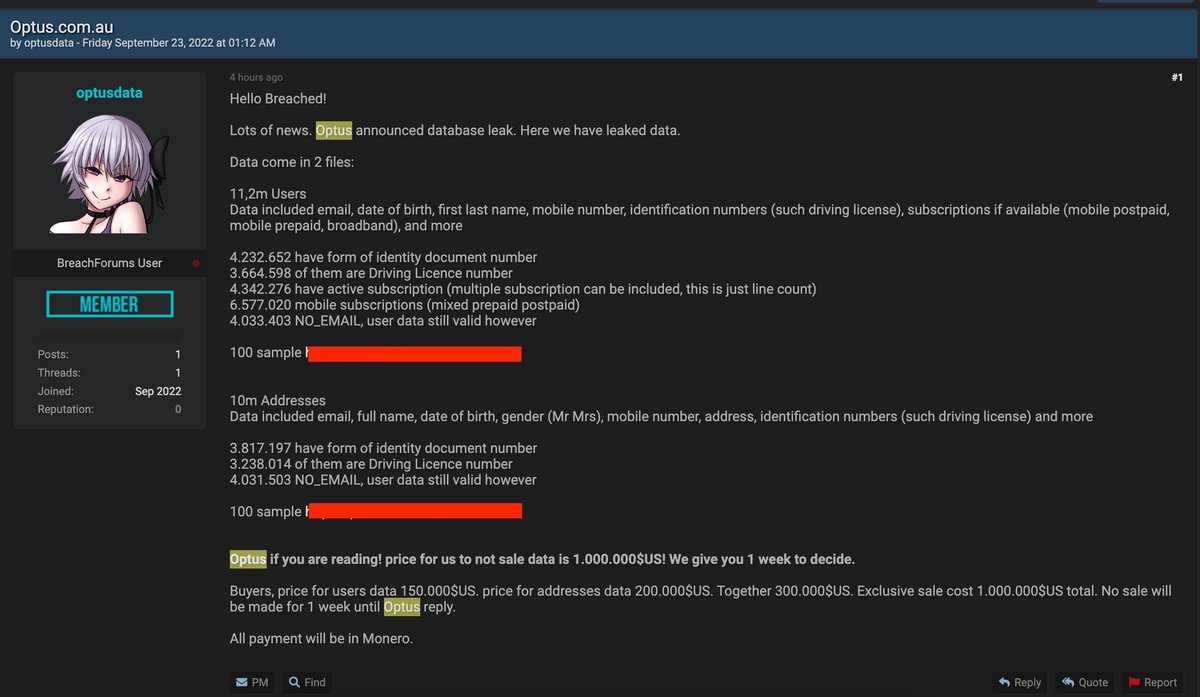
Bad news. The Optus hacker has released 10,000 customer records and says a 10K batch will be released every day over the next four days if Optus doesn't give into the extortion demand. #OptusDataBreach #optushack #auspol #infosec 

Quick observation on this new data. It appears Medicare numbers may be exposed for some people. Redacted screenshot below. #Optus #OptusDataBreach 

The word "Medicare" appears 55 times across these records.
About 45 minutes ago, the Optus hacker sent me a private message from the account where the original three data samples were posted. The person sent a link to that new thread we are seeing. So yes, it appears to be legitimate as in done by the same person. #OptusHack #auspol
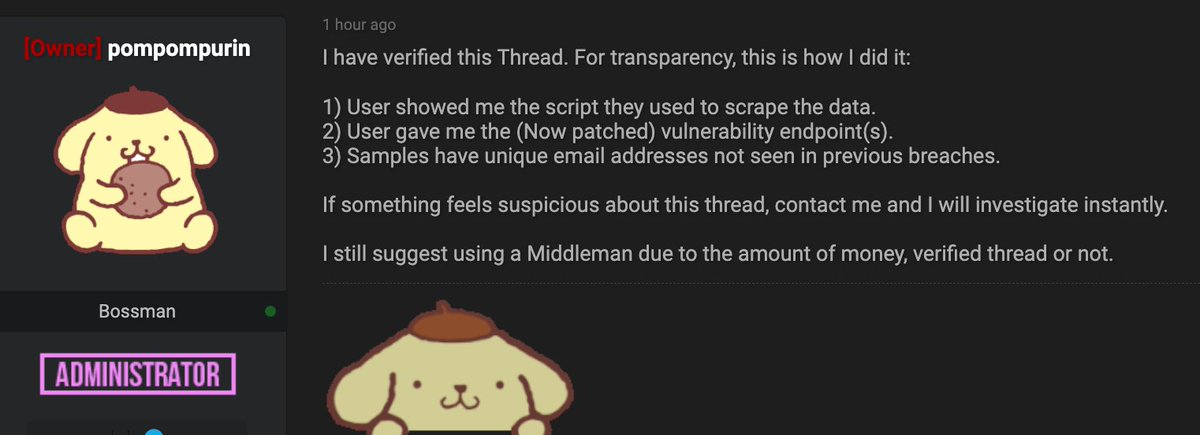
The old post is now deleted. The data samples are gone. Here is the new post (ht to @allyjfoster for sending it to me while I was out getting cat food). 

Many questions around this: Why has this person seemingly changed their mind? Can we trust this person now? What does this person mean by writing about not being able to delete the data from the drive? #optushack #auspol
Spot analysis: If this holds and no more Optus customer data is released on this website, this is best outcome for what was becoming an even more awful situation. But it is one in which we should have firstly never been in. #OptusHack #auspol
Also: This doesn't change the risk for anyone exposed. The Optus data has been stolen, and we can't trust this person. No guard should be let down: monitor your credit, watch out for dodgy SMS/emails and follow the good advice at cyber.gov.au #infosec #OptusHack
UPDATE: The original data samples are gone, but other people on that forum have copied the data are distributing it. This is disappointing of course and means that those 10,200 Optus users in these three data samples would be at an immediate heightened risk of fraud, ID theft.
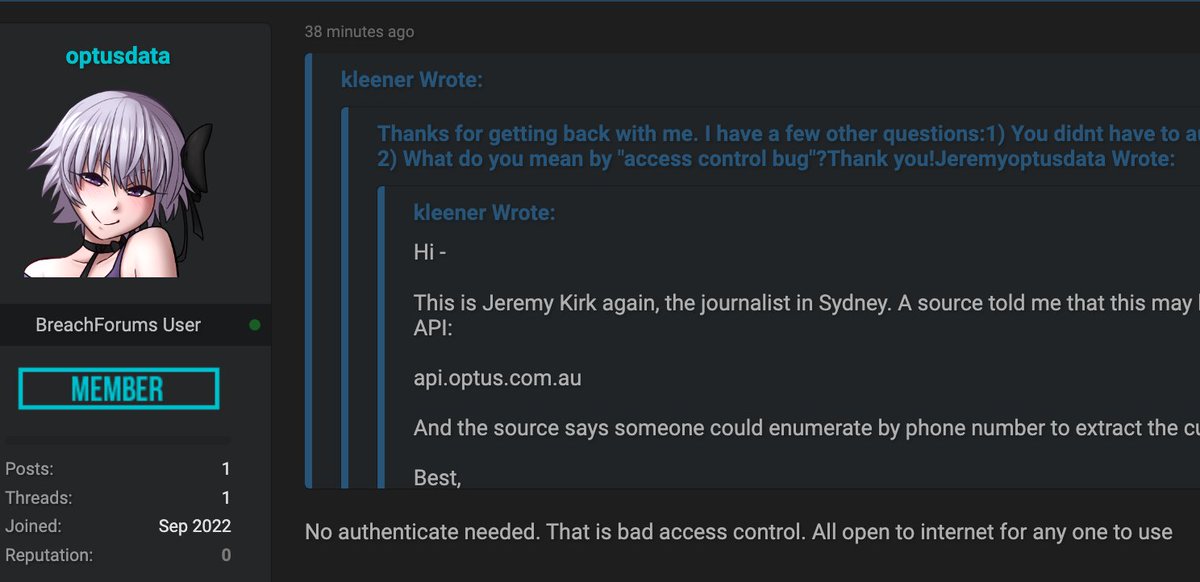
Does anyone know if Optus has a vulnerability disclosure program or a bug bounty program? The Optus hacker claims they might have reported the API security problem if Optus was easier to contact.
This is a pretty flimsy rationale of course for deciding instead to launch a million-dollar extortion campaign against Optus but here we are.
For those of you who have managed to make it to the end of this thread, I've wrapped all of this up into a story here: bankinfosecurity.com/optus-attacker…
• • •
Missing some Tweet in this thread? You can try to
force a refresh