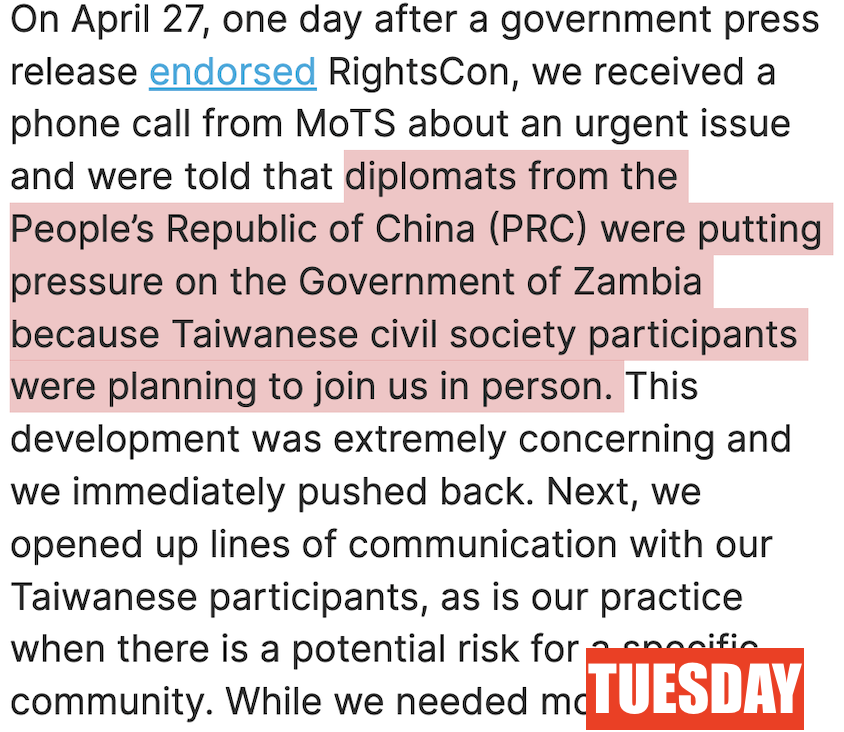
BREAKING: journalists & human rights defenders hacked with #Pegasus in 🇲🇽#Mexico.
Years *after* spyware scandals & new President's promise that abuses were over.
THREAD 1/
Report by @R3Dmx ejercitoespia.r3d.mx
We @citizenlab did forensic validation: citizenlab.ca/2022/10/new-pe…

Years *after* spyware scandals & new President's promise that abuses were over.
THREAD 1/
Report by @R3Dmx ejercitoespia.r3d.mx
We @citizenlab did forensic validation: citizenlab.ca/2022/10/new-pe…
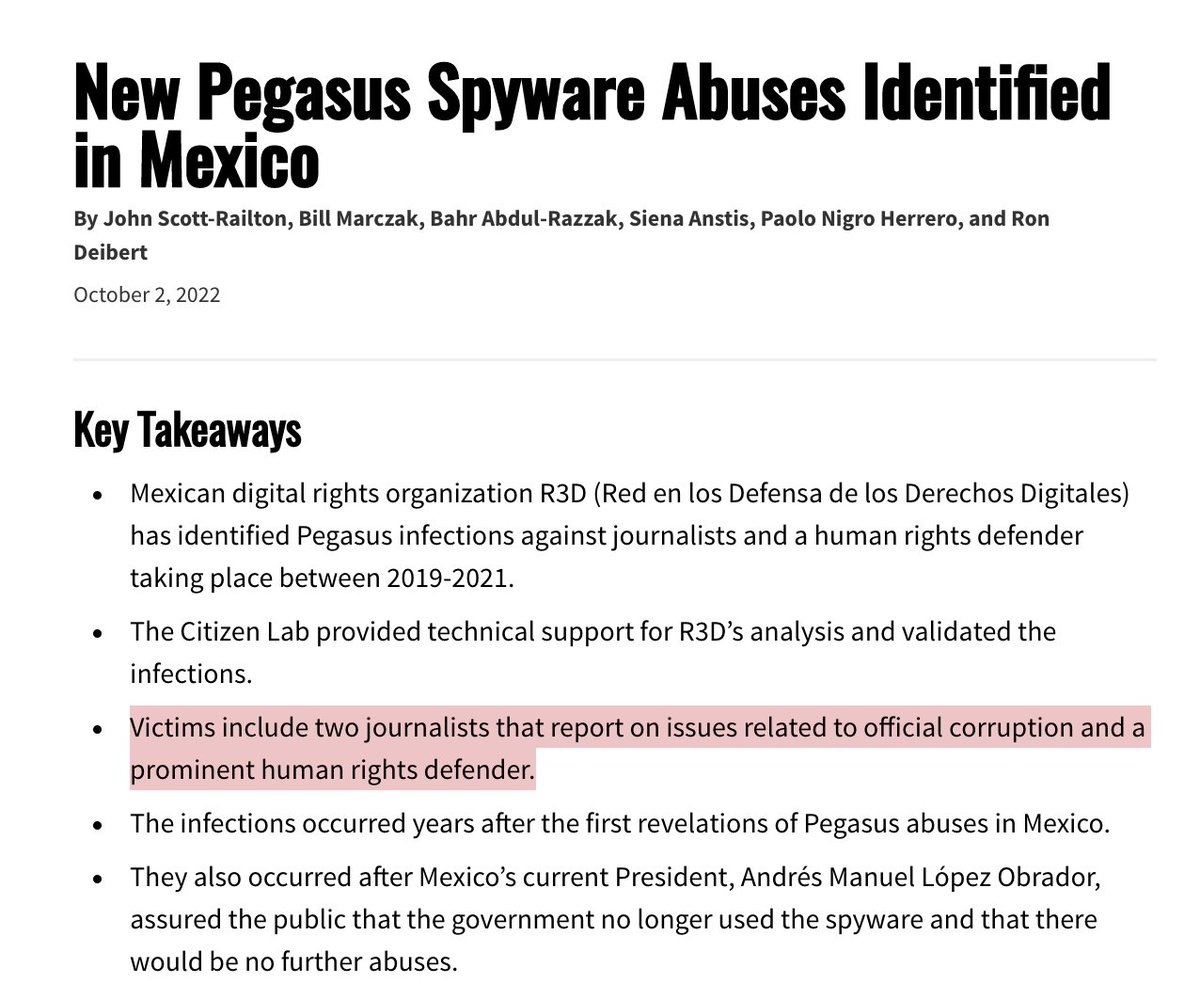

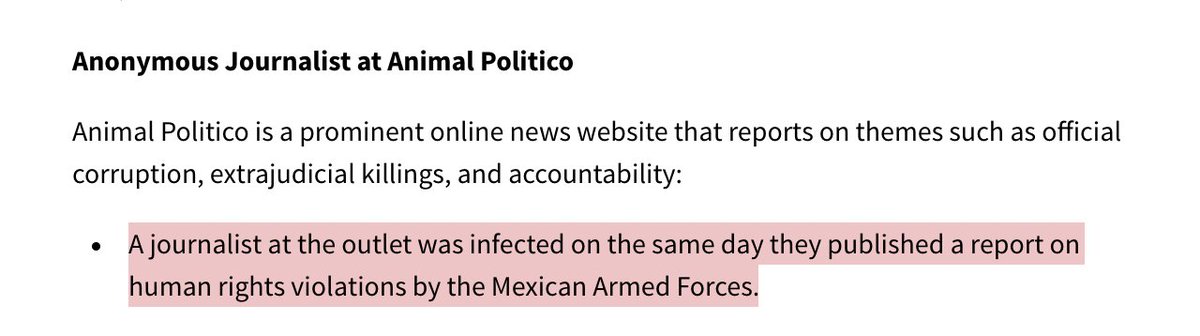
2/ Per @R3Dmx, #Pegasus victims were infected while working on:
❌Connections between Los Zetas Cartel & Mexican Army
❌Official misconduct in investigations into #Ayotzinapa forced disappearances
❌Human rights violations by Mexican Armed Forces.
Chilling.


❌Connections between Los Zetas Cartel & Mexican Army
❌Official misconduct in investigations into #Ayotzinapa forced disappearances
❌Human rights violations by Mexican Armed Forces.
Chilling.


3/ Mexico was first rocked by #Pegasus scandals in 2017 under President @EPN.
We @citizenlab, @R3Dmx @socialtic & @article19org had found dozens of abuse cases.
When Pres. @lopezobrador_ took office, he promised hacking abuses were a thing of the past...

We @citizenlab, @R3Dmx @socialtic & @article19org had found dozens of abuse cases.
When Pres. @lopezobrador_ took office, he promised hacking abuses were a thing of the past...

4 Mexico's #Pegasus scandals didn't stop.
The #PegasusProject also revealed that scores in the circle of @lopezobrador_ had been potentially selected for targeting while @EPN was in office.
Including now-President AMLO's wife & children.
The #PegasusProject also revealed that scores in the circle of @lopezobrador_ had been potentially selected for targeting while @EPN was in office.
Including now-President AMLO's wife & children.

5/ Mexico has been one of the *most* notorious cases of #Pegasus spyware abuses.
NSO Group has has been confronted about this. For years.
Mexico's new president, touched himself by spyware abuses prior to entering office... had promised it was over.
Yet here we are.
NSO Group has has been confronted about this. For years.
Mexico's new president, touched himself by spyware abuses prior to entering office... had promised it was over.
Yet here we are.
6/ Yet again, journalists & human rights defenders of intense interest to the Mexican government got hacked.
Chillingly, some of their work was clearly of intense interest to cartels, too.
#Mexico has seen *half a decade* of abuses like this.
Chillingly, some of their work was clearly of intense interest to cartels, too.
#Mexico has seen *half a decade* of abuses like this.

7/ I urge you to read @R3Dmx's full report. Here's their thread on the cases.
https://twitter.com/R3Dmx/status/1576709050641059840
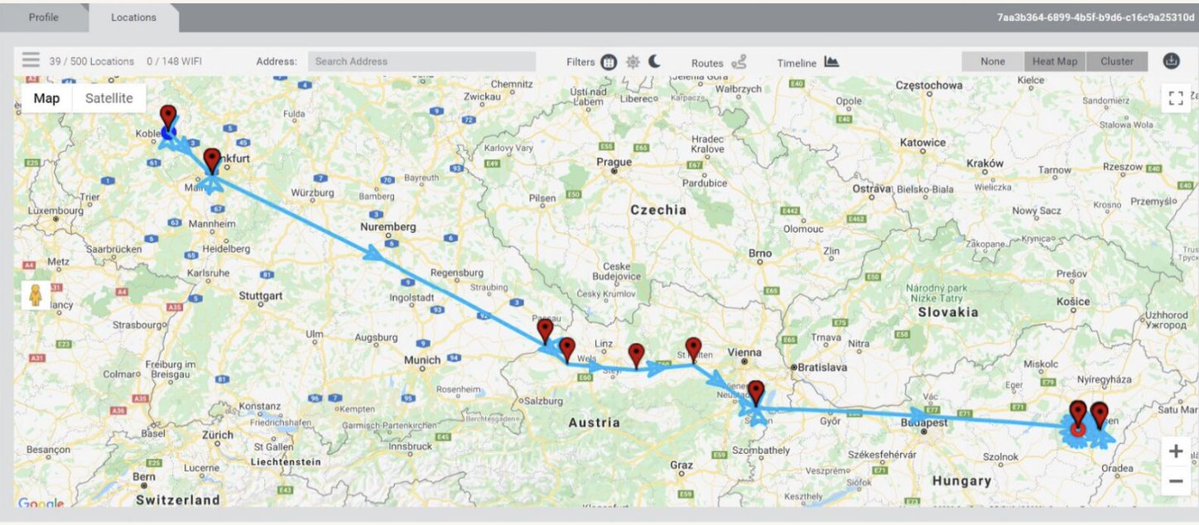
8/ Another key find via @R3Dmx: Mexico did recent business with companies linked to prior #Pegasus contracts👇👇
Despite making strenuous efforts to deny any such business.
Despite making strenuous efforts to deny any such business.
https://twitter.com/R3Dmx/status/1576709260570165249
9/ A key detail: while previous Pegasus cases @citizenlab investigated in #Mexico involved finding SMS messages and 1-click attacks... these latest cases were zero-click attacks.
No action was required on the part of the victims to be infected.


No action was required on the part of the victims to be infected.



10/ Of course NSO has a response that is not serious.
https://twitter.com/jsrailton/status/1577039481861197824
• • •
Missing some Tweet in this thread? You can try to
force a refresh