
2/ A running print spooler service on domain controllers is still a relatively common finding in our AD assessments, even though an attack path via spooler service and unconstrained delegations have been known for years. [1]
Screenshot below from #PingCastle (@mysmartlogon)
Screenshot below from #PingCastle (@mysmartlogon)

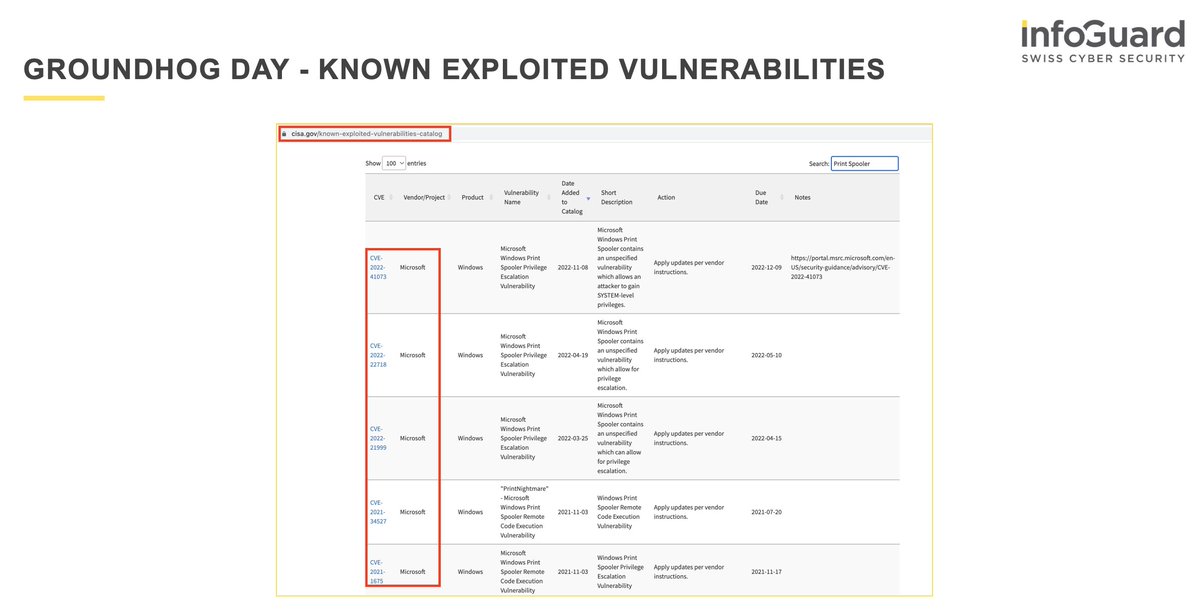
3/ Apart from the (older) attack technique with unconstrained delegations (see above), the printer spooler has had various critical vulnerabilities over the last two years. [3] 
4/ In a recent incident response investigation, the attacker attempted to exploit the PrintNightmare (CVE-2021-34527) vulnerability.
https://twitter.com/malmoeb/status/1628850749458329600
6/ Disable the print spooler service on domain controllers if possible to reduce the attack risk in case of an active attacker in the network.
7/ Additionally, the corresponding Windows patches (as an example for the LPE via PrintNightmware) must be rolled out and installed quickly across the board.
8/ References:
[1] adsecurity.org/?p=4056
[2] github.com/m8sec/CVE-2021…
[3] cisa.gov/known-exploite…
[1] adsecurity.org/?p=4056
[2] github.com/m8sec/CVE-2021…
[3] cisa.gov/known-exploite…
• • •
Missing some Tweet in this thread? You can try to
force a refresh



















