1/ #Velociraptor has covered hunting for malicious WMI Event Consumers for some time. [1]
However, Velociraptor does not provide an eradication hunt for malicious WMI Event Consumers out of the box.
🧵 #CyberSecurity
However, Velociraptor does not provide an eradication hunt for malicious WMI Event Consumers out of the box.
🧵 #CyberSecurity
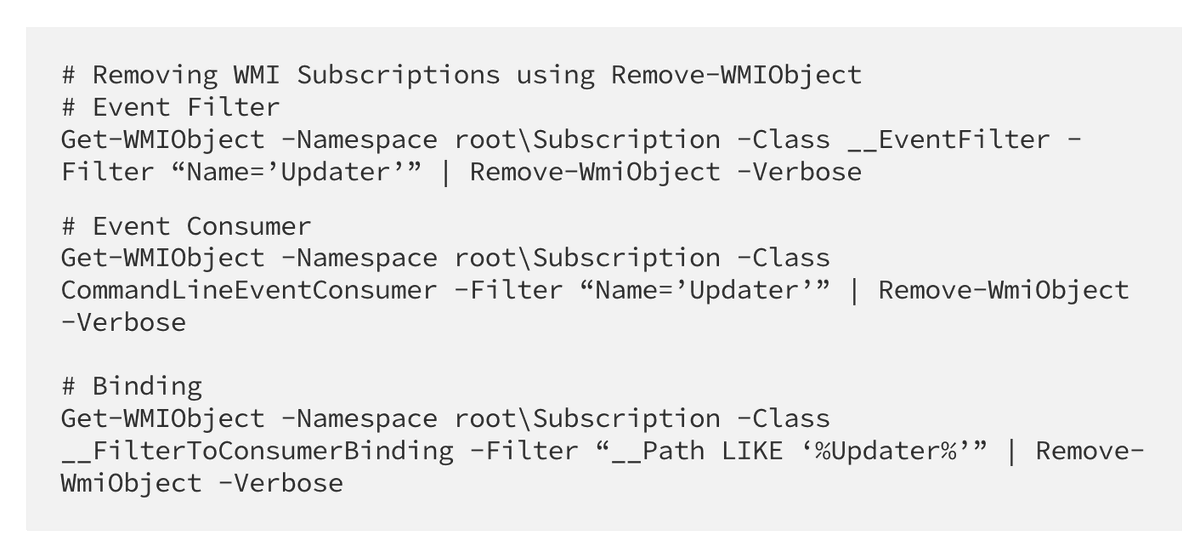
2/ @threatpunter wrote a detailed blog about WMI persistences and how to remove them.
"The simplest method to remove the entry from the WMI database is to use Autoruns. Launch Autoruns as an administrator and select the WMI tab to review WMI-related persistence." ✂️
"The simplest method to remove the entry from the WMI database is to use Autoruns. Launch Autoruns as an administrator and select the WMI tab to review WMI-related persistence." ✂️

• • •
Missing some Tweet in this thread? You can try to
force a refresh