🈹 Stop buying #pepedao / #pipipump / #bobcoin, owner can rug you.
Scammer deployed >67 malicious tokens. These contracts are obfuscated and designed to bypass @GoplusSecurity & @Token_Sniffer's rugpull analysis.
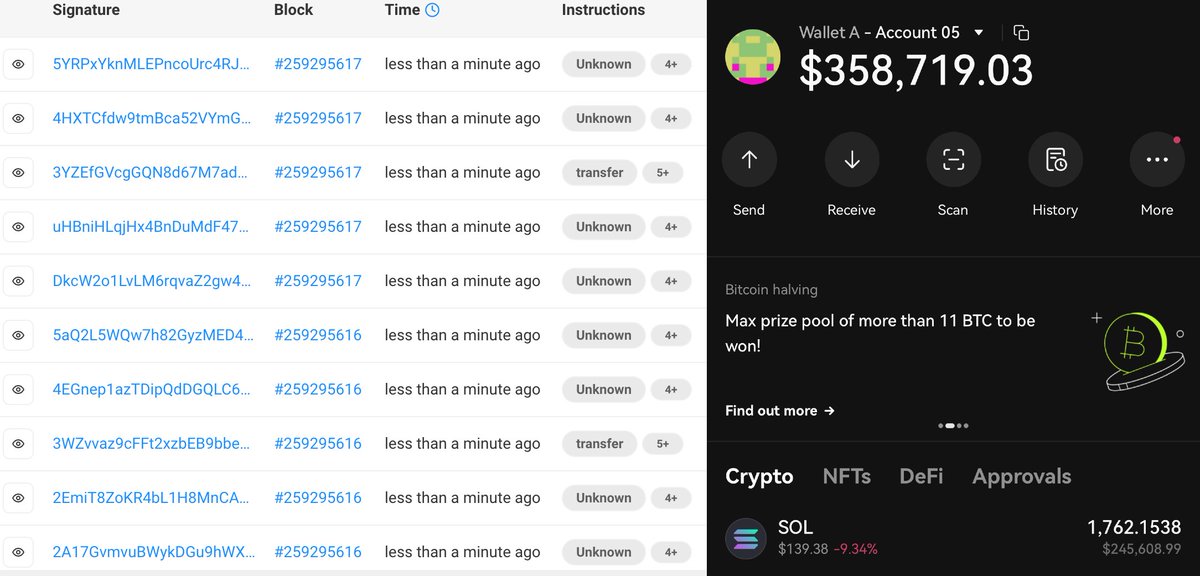
~$300k funds have already been rugged.
#ScamAlert #rugpull twitter.com/i/web/status/1…
Scammer deployed >67 malicious tokens. These contracts are obfuscated and designed to bypass @GoplusSecurity & @Token_Sniffer's rugpull analysis.
~$300k funds have already been rugged.
#ScamAlert #rugpull twitter.com/i/web/status/1…

@GoplusSecurity @Token_Sniffer So, what's going on?
1. The attacker uses "oowner" to define the owner so that analysis considers the contract has no owner -- really benign in the eye of static analysis! twitter.com/i/web/status/1…
1. The attacker uses "oowner" to define the owner so that analysis considers the contract has no owner -- really benign in the eye of static analysis! twitter.com/i/web/status/1…
@GoplusSecurity @Token_Sniffer 2. The code for rug pull is inside "transfer" and "Approve" functions, very unconventional.
3. The attacker can only get infinite tokens by transferring tokens to themselves. Analysis by security companies misses this case and considers the token to have a constant total supply.
To list a few false negatives
gopluslabs.io/token-security…
gopluslabs.io/token-security…
@GoplusSecurity, you may want to take a look.
gopluslabs.io/token-security…
gopluslabs.io/token-security…
@GoplusSecurity, you may want to take a look.
There are >1000 (deployers and market makers) addresses involved in this scam with different funding sources (@binance / @SimpleSwap_io, @aztecnetwork, @TornadoCash).
@binance @SimpleSwap_io @aztecnetwork @TornadoCash attacker just took $78k profit from #pepedao and created a new scam token:
etherscan.io/token/0xf533d9…
etherscan.io/token/0xf533d9…

• • •
Missing some Tweet in this thread? You can try to
force a refresh