🚨SlowMist Security Alert🚨
Recently, there have been a lot of asset thefts caused by shared #Apple IDs. We believe that the key is "apps are not bound to device codes".
Recently, there have been a lot of asset thefts caused by shared #Apple IDs. We believe that the key is "apps are not bound to device codes".
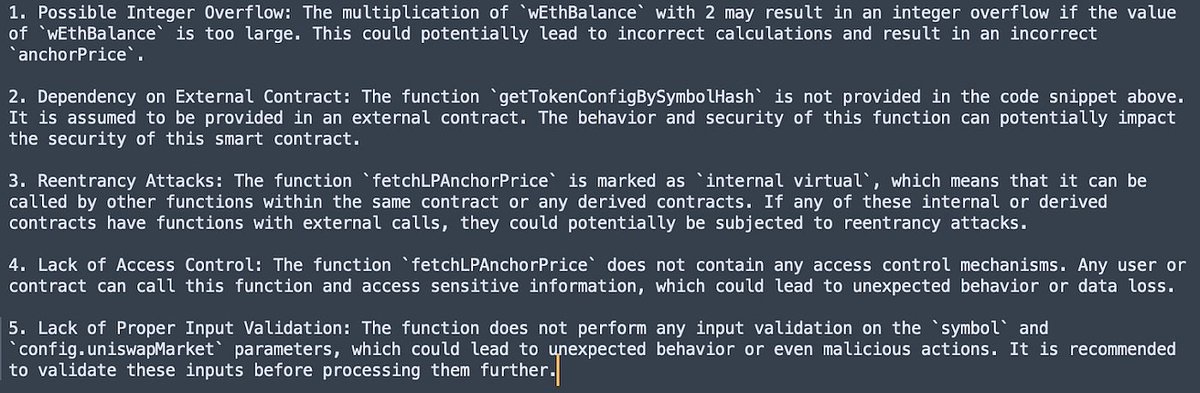
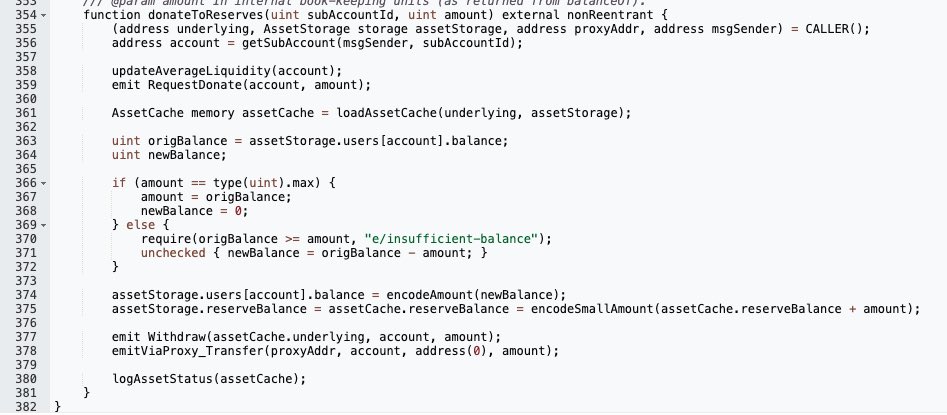
1/ This is an issue prevalent in 99% of #wallets, trading apps,and other apps. It's a concern we've voiced a long time ago. However, due to it not being considered in the initial stages of app design, the majority of apps in the market have yet to rectify this issue.
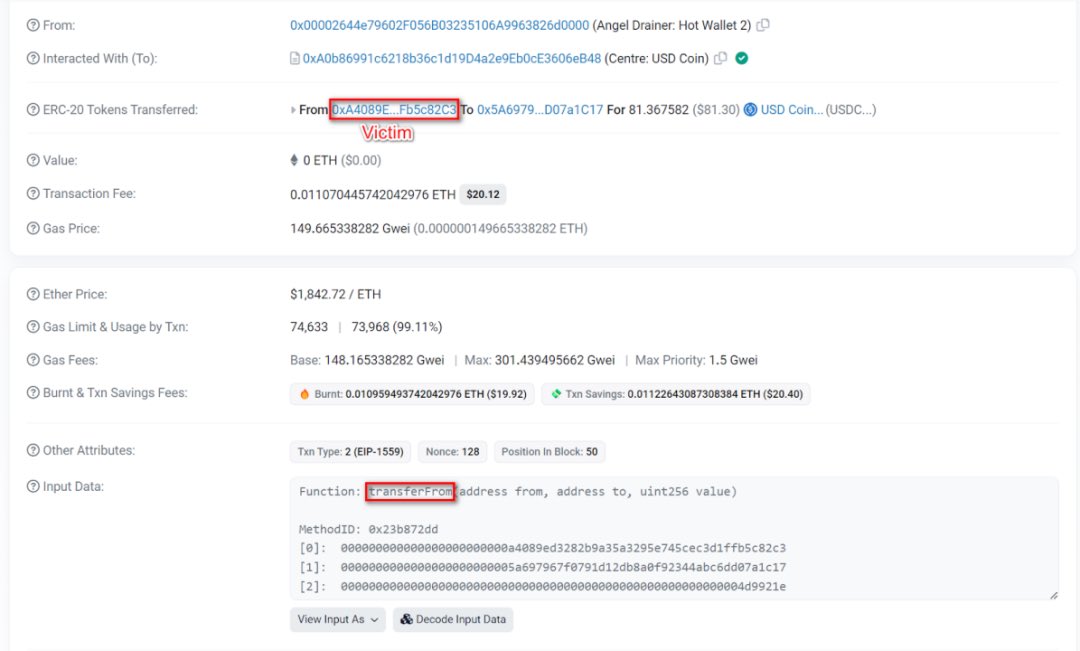
2/ This lack of binding can lead to data being dragged off or maliciously synchronized to other devices, resulting in potential breaches. Combined with other techniques such as social engineering, brute force attacks to obtain passwords, this can lead to theft of assets.
3/ A word of caution for everyone: Do not use shared Apple IDs and be wary of screenshots being uploaded from your photo gallery. There have been instances where such actions led to losses.
4/ Additional note: There's possibly an element of decentralization here. If past device information is bound, it could lean towards centralization, so maintaining a balance here poses its own set of challenges.
5/ NEVER use shared Apple IDs. Not only is the risk of theft high, but your device could also become a problem. Good security awareness is paramount.
Shoutout to @IM_23pds.🫡
Shoutout to @IM_23pds.🫡
• • •
Missing some Tweet in this thread? You can try to
force a refresh

 Read on Twitter
Read on Twitter