Transparency: deleted thread about an article on how CN propaganda likely decontextualized & amplified a video of the Dalai Lama.
Because, though context matters, missing from that discussion is that it's also always ok to question the behavior of people w/authority. 1/
Because, though context matters, missing from that discussion is that it's also always ok to question the behavior of people w/authority. 1/
2/ And that "you misunderstood" is so commonly used to dismiss real allegations... that calling out China's deliberate decontextualization (and longstanding attempts to erase) Tibetan culture... without also front-ending this reality didn't strike a good balance.
3/ For those seeking context, Tibet's government in exile, as well as the Dalai Lama, have been subjected to relentless attacks and propaganda by China.
Much of it targeting a western audience.
It is part of a relentless drumbeat of repression. hrw.org/video-photos/i…
Much of it targeting a western audience.
It is part of a relentless drumbeat of repression. hrw.org/video-photos/i…
4/ Another more recent component of China's propaganda strategy around Tibet and other groups?
Influencers.
It is darkly ironic that they appear on YouTube, which is blocked within China.
aspi.org.au/report/frontie…


Influencers.
It is darkly ironic that they appear on YouTube, which is blocked within China.
aspi.org.au/report/frontie…



5/ Tibetans, the government in exile, and the Dalai Lama himself are the longstanding targets and victims of concerted repression by China.
And China is constantly experimenting with new tactics to censor and block their voices.
reuters.com/article/china-…
And China is constantly experimenting with new tactics to censor and block their voices.
reuters.com/article/china-…

6/ China has also been exceptionally active on platforms like #Twitter.
Some of this activity includes amplifying & promoting government narratives about minority groups.
With Twitter's blocking efforts gone, expect loads more...
(Pic 2021)
blog.twitter.com/en_us/topics/c…
Some of this activity includes amplifying & promoting government narratives about minority groups.
With Twitter's blocking efforts gone, expect loads more...
(Pic 2021)
blog.twitter.com/en_us/topics/c…

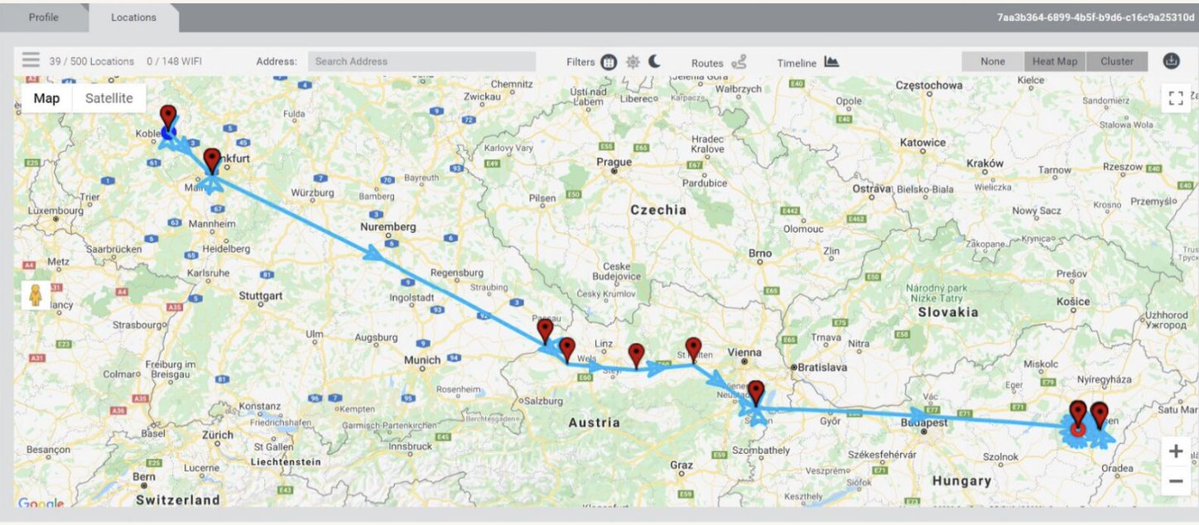
7/ Chinese efforts to shape the discourse aren't just limited to pushing propaganda narratives about minority groups.
Researchers have found evidence of networks targeting specific individuals, like female Asian journalists, for intense attacks.
axios.com/2022/06/03/chi…
Researchers have found evidence of networks targeting specific individuals, like female Asian journalists, for intense attacks.
axios.com/2022/06/03/chi…

8/ And it's not just bot accounts. An account of an individual who has worked for Chinese state-run media quickly showed up in the replies to my original tweets... repeatedly harassing and insulting people.
9/ The fact that you find as many headlines about Tibet is no accident.
China's efforts to prevent you from hearing Tibetan news, voices, context and perspectives extend far offline... and far outside China's borders.
codastory.com/authoritarian-…



China's efforts to prevent you from hearing Tibetan news, voices, context and perspectives extend far offline... and far outside China's borders.
codastory.com/authoritarian-…




10/ Repression in Tibet (which is ruled by the #CCP) is *extreme* and seems designed to erase Tibetan identity & culture.
The Dalai Lama and Tibet's Central Tibetan Administration (government in exile) are based in Dharamshala, India.
freedomhouse.org/country/tibet/…



The Dalai Lama and Tibet's Central Tibetan Administration (government in exile) are based in Dharamshala, India.
freedomhouse.org/country/tibet/…




• • •
Missing some Tweet in this thread? You can try to
force a refresh