Documentary photographer, old creaky hacker. Co-author of @OWASP ASVS standard. Blackhat/Brucon Review Board & Co_chair UK Gov Cyber Security Advisory Board
How to get URL link on X (Twitter) App


 Needless to say, with the football on, I delved deep into understanding it a bit more
Needless to say, with the football on, I delved deep into understanding it a bit more


 where, in essence, the idea was to prioritize patches by expressing the connectivity of various vulnerabilities on a network with a QUBO and then solving this with quantum annealing.
where, in essence, the idea was to prioritize patches by expressing the connectivity of various vulnerabilities on a network with a QUBO and then solving this with quantum annealing.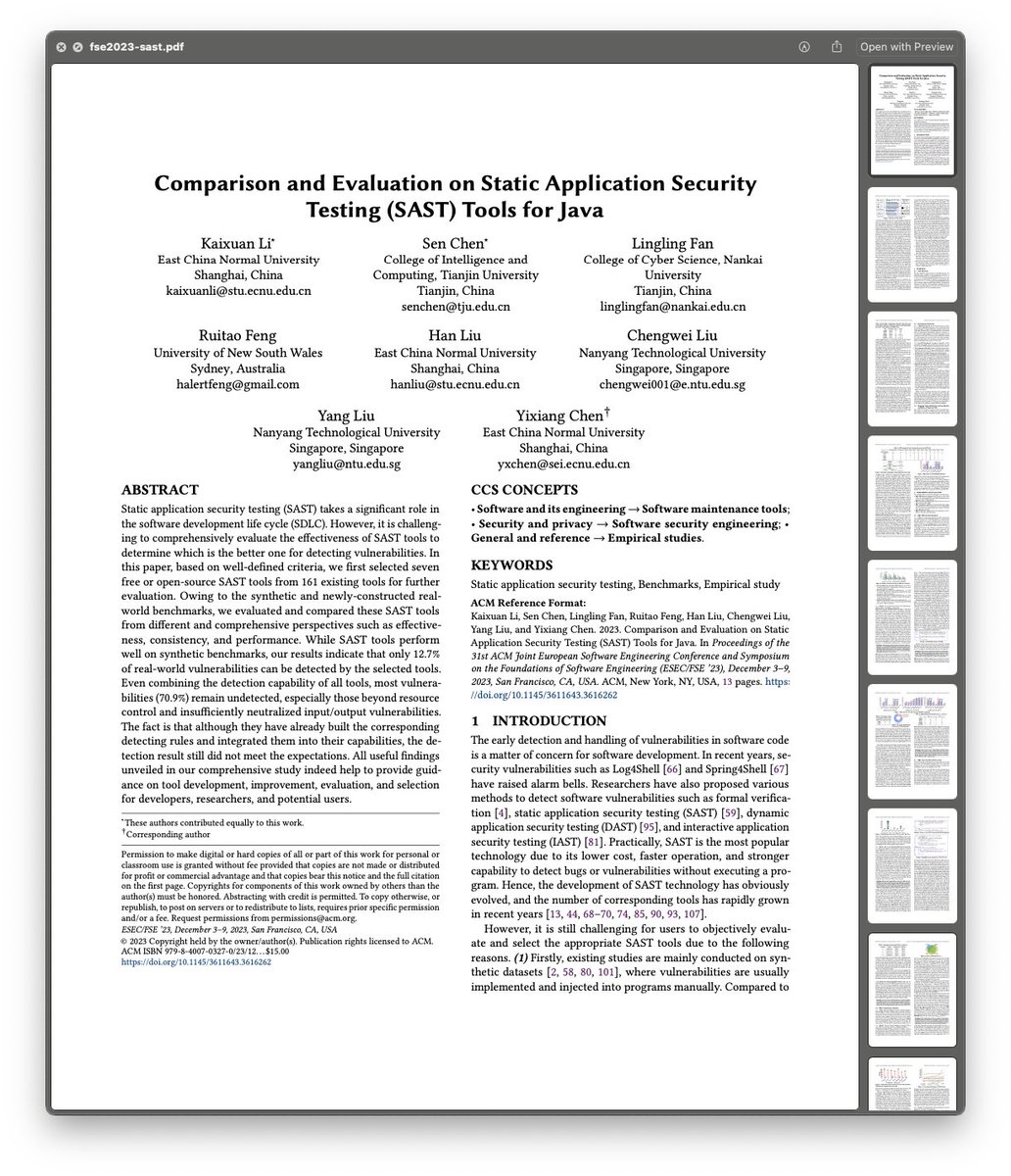
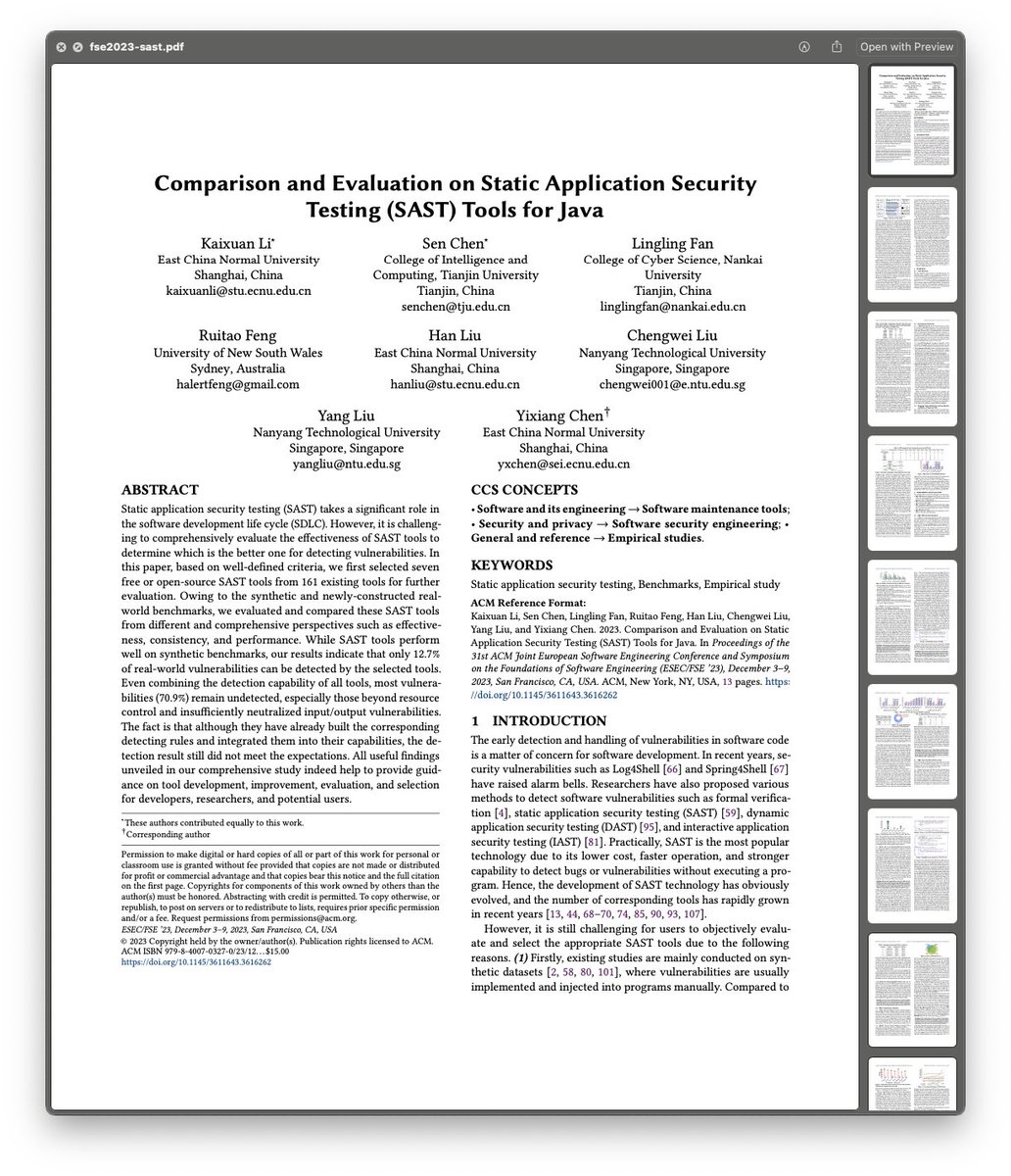 First up, what did they use and what did they benchmark it against?
First up, what did they use and what did they benchmark it against? 



 First up it’s pretty cool. My views on the pervasive nature of the tracking industry are not something I’ve hidden away: it’s an ugly industry with no real oversight, so any efforts to put a finger in their eye is one to applaud
First up it’s pretty cool. My views on the pervasive nature of the tracking industry are not something I’ve hidden away: it’s an ugly industry with no real oversight, so any efforts to put a finger in their eye is one to applaudhttps://twitter.com/swiftonsecurity/status/1666258511557271554The daily routine used to be monitor checkpoint FWs and add new rules to stop silly attempts at scanning Solaris, adding rules to allow apache to talk to oracle and so on. Then Cisco came out with this box that meant we could use a handful of IPv4 and then rfc1918 in our DC



 I mean, HELO
I mean, HELO 





 Second menu option testing. Chicken laksa curry learned from our time living in Singapore. We struggle to get a proper laksa here in London so time to change that.
Second menu option testing. Chicken laksa curry learned from our time living in Singapore. We struggle to get a proper laksa here in London so time to change that. 






 As expected with such a compelling body of work, his first book is sold out and I'm a bit gutted but you snooze and you lose.
As expected with such a compelling body of work, his first book is sold out and I'm a bit gutted but you snooze and you lose. 

 For all that effort, they got awarded $1750
For all that effort, they got awarded $1750