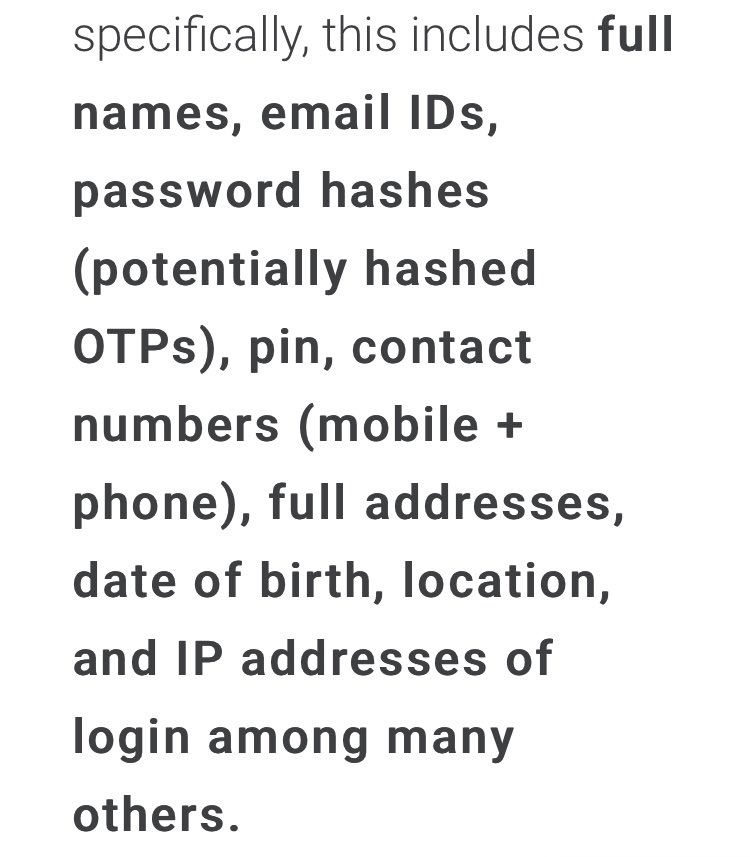
Damn, 15GB SQL database including passwords!
BigBasket faces potential data breach; details of 2 crore users put on sale on dark web financialexpress.com/industry/sme/b…
BigBasket faces potential data breach; details of 2 crore users put on sale on dark web financialexpress.com/industry/sme/b…
The DB has user type for staff, superusers, last login IP, full address, details of order, and many many datasets. This is not a simple user table, it’s has all operational details of #BigBasket 



@AuCyble says the breach occurred possibly on Oct 14th, and they detected (discovered, perhaps) on Oct 30th, and disclosed it to @bigbasket_com on Nov 1st, after validating the data is real.
@bigbasket_com doesn’t seem to have any capability to detect it themselves. It’s been a week they got notified by @AuCyble. Yet there’s no direct communication from them about breach of my personal data from their custody, despite being their customer for years.
Many others on Twitter are confirming that so far they haven’t received any sort of communication or email by @bigbasket_com on data breach.
Needless to say, if you have re-used the @bigbasket_com password on other sites, change them all immediately.
Also pray to god and keep your fingers crossed, that criminals don’t steal your identity and/or cause you trouble by misusing the uncommon food orders and personal details disclosed in the breach.
Among other activities in incident handling, what @bigbasket_com should have done:
1. Communicate to all customers 2. reset all current authentications
3. trigger email to forcing customers to reset the password #BigBasketBreach
1. Communicate to all customers 2. reset all current authentications
3. trigger email to forcing customers to reset the password #BigBasketBreach
They certainly haven’t done #1 & 3.
Neither did they reset currently logged-in and authenticated session.
I could go till the Payment page on my @bigbasket_com app.
(Had to trim top part of video to hide my address, despite being sold somewhere on dark web)
Neither did they reset currently logged-in and authenticated session.
I could go till the Payment page on my @bigbasket_com app.
(Had to trim top part of video to hide my address, despite being sold somewhere on dark web)
hope @haveibeenpwned @troyhunt gets hold of this dump.
No word by @bigbasket_com on breach of my personal data. But marketing emails continue. 

• • •
Missing some Tweet in this thread? You can try to
force a refresh