Whenever I talk about an Android app sending data to Asian countries, some folks go crazy.
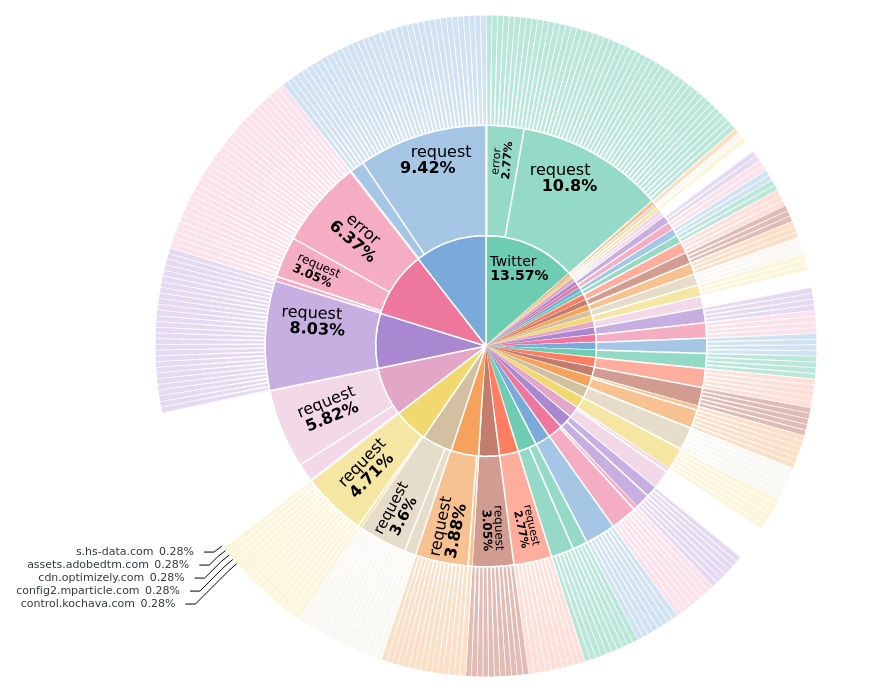
Let me comfort you: If you are a European user, like me, most apps communicate to US servers as shown below (2h capture ... DJI, AliExpress, Gojek etc).
What? Not to US?? Let me help you!
Let me comfort you: If you are a European user, like me, most apps communicate to US servers as shown below (2h capture ... DJI, AliExpress, Gojek etc).
What? Not to US?? Let me help you!

My issue is simply that I am using a German DNS-Server, which might be a bit biased when it comes to resolving a DNS host to the best suited server.
So lets resolve with DNS over TLS from @Cloudflare
Hmm ... still so much US-traffic, even from Asian apps?
So lets resolve with DNS over TLS from @Cloudflare
Hmm ... still so much US-traffic, even from Asian apps?

Okay, my fault ... I am still using an European source IP (Germany).
So let me change this, too, by using a VPN exit in Japan!
Damn, even more requests are directed to US, now.
Sorry, I cannot help you - your data will always end up in US ... unless you install Camera360 😉
So let me change this, too, by using a VPN exit in Japan!
Damn, even more requests are directed to US, now.
Sorry, I cannot help you - your data will always end up in US ... unless you install Camera360 😉

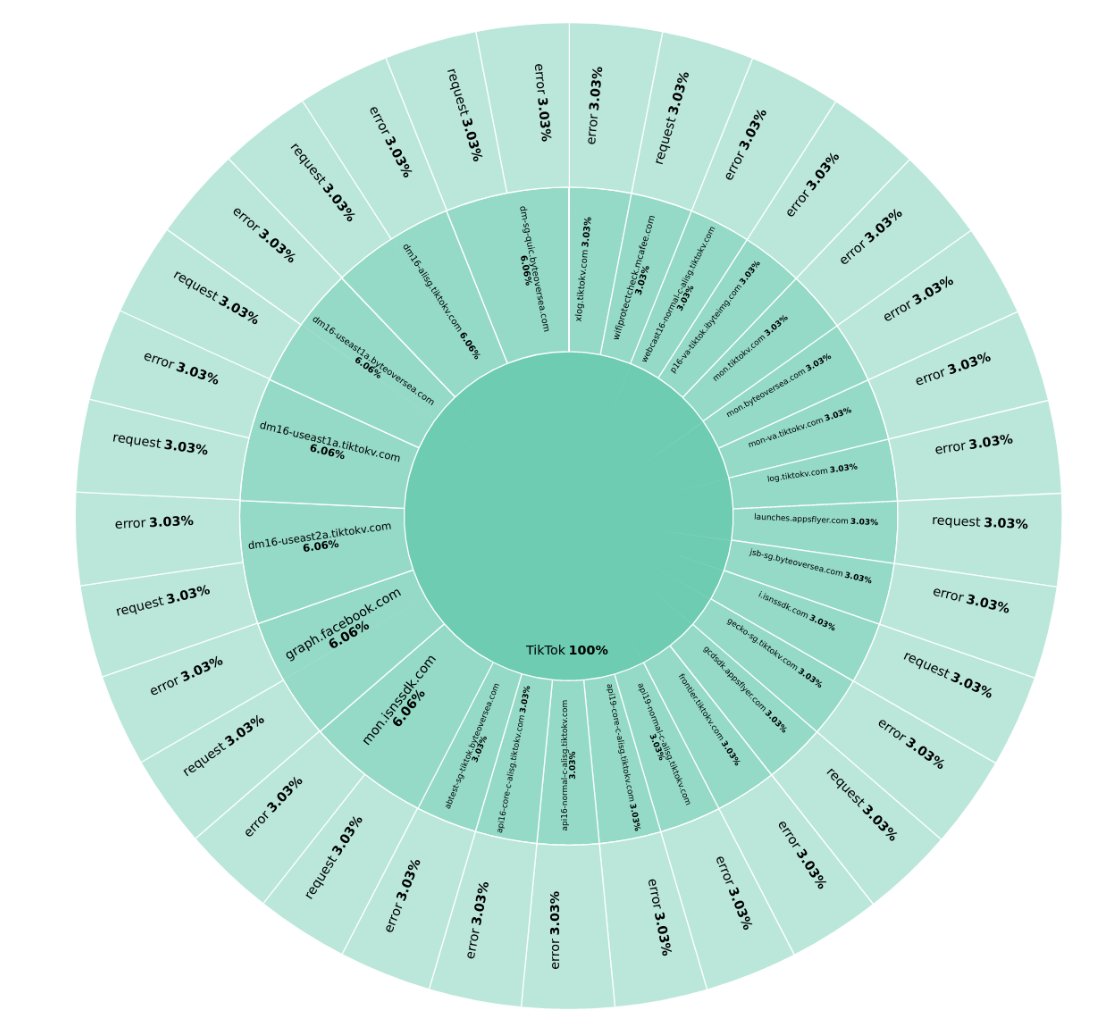
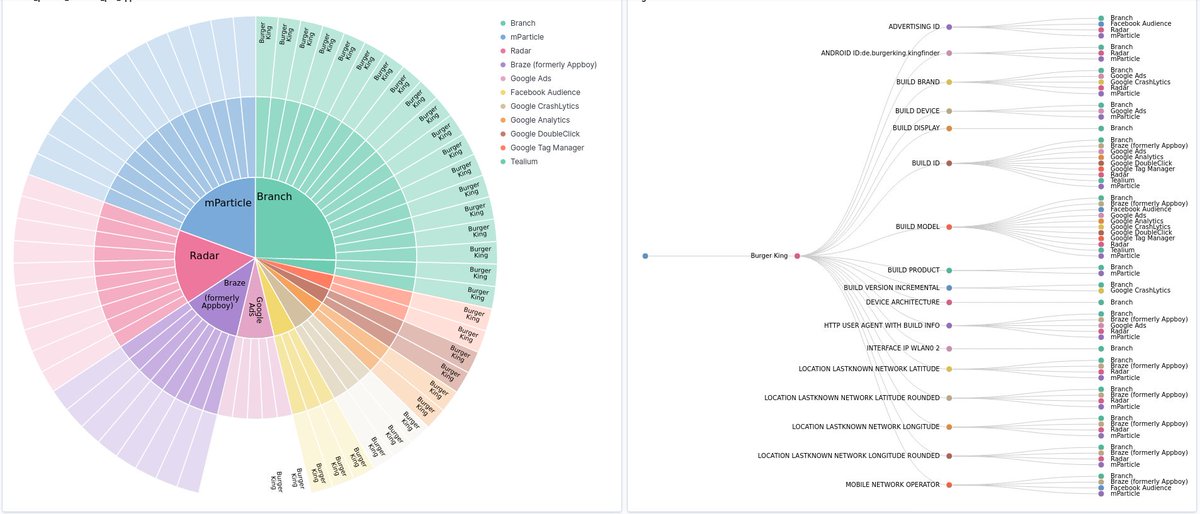
A bit more insights: Here are the hosts which changed their country (while I changed my appearance like described above).
Excuse the bad visualization, had no better option because of data aggregation order.
Excuse the bad visualization, had no better option because of data aggregation order.

• • •
Missing some Tweet in this thread? You can try to
force a refresh