#CrowdStrike have produced fascinating research into #SUNSPOT malware, which was used to implant the SUNBURST / SolarWinds backdoor.
Here are my Threat Hunting tips to:
➡️ Find the malware on disk
➡️ Find the persistence
➡️ Decrypt the log files
➡️ Find if it's running
👇
Here are my Threat Hunting tips to:
➡️ Find the malware on disk
➡️ Find the persistence
➡️ Decrypt the log files
➡️ Find if it's running
👇
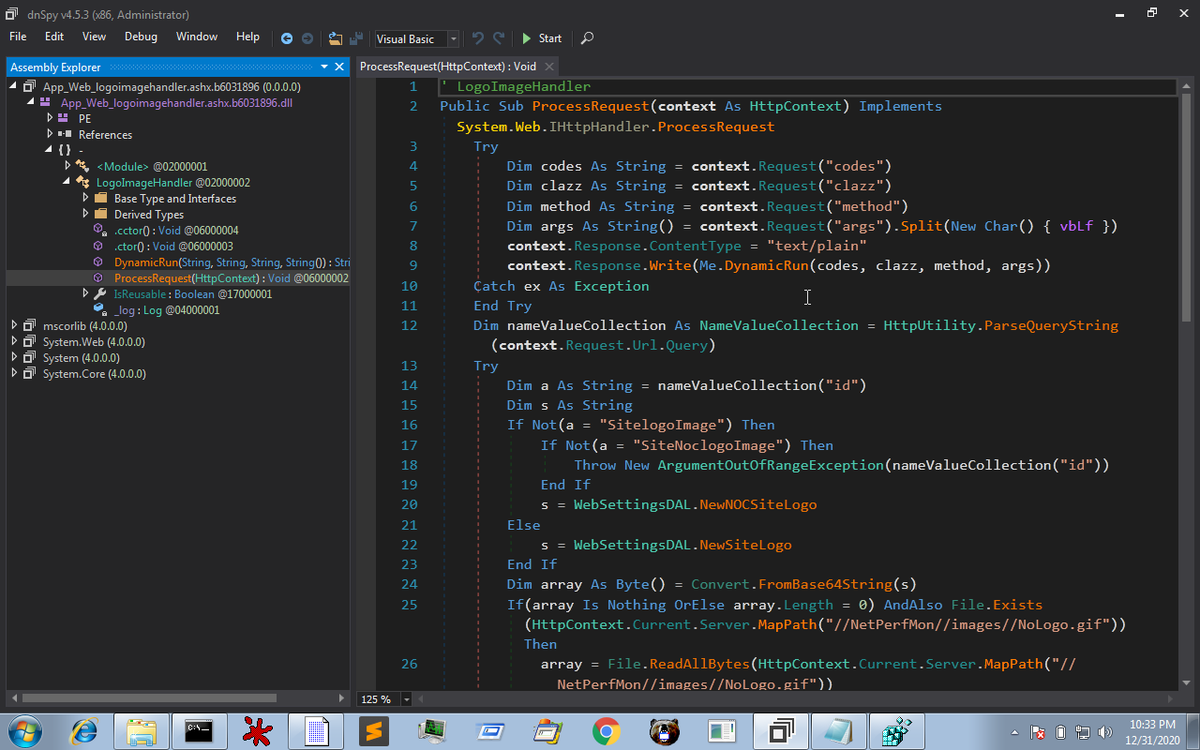
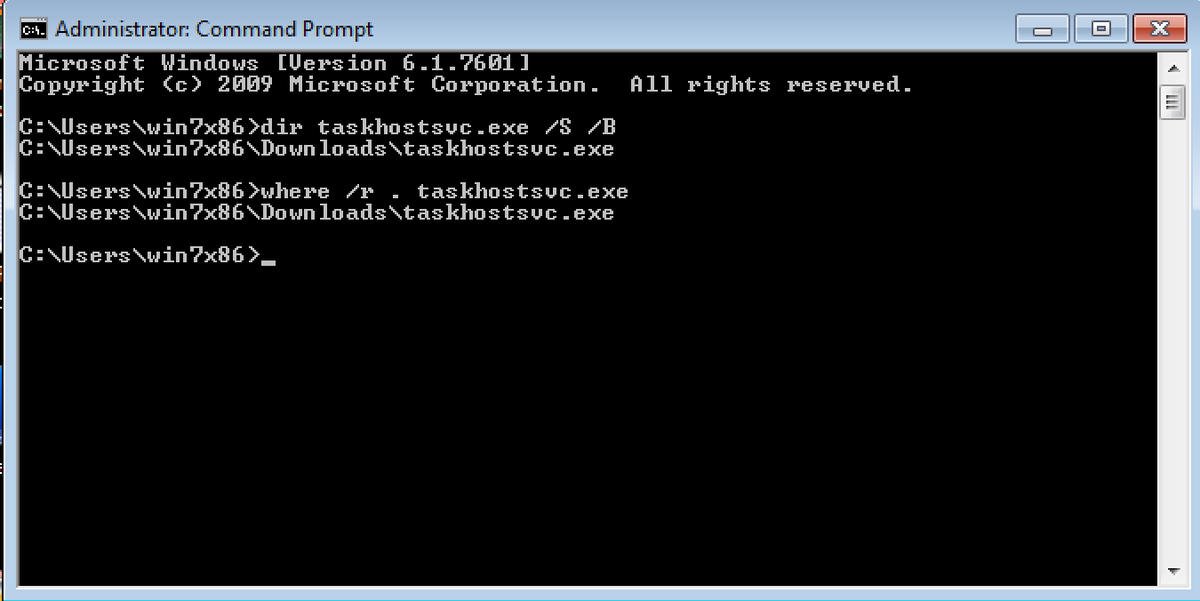
The malware exists on disk as taskhostsvc.exe
You can use the following commands to look for files on Windows
dir taskhostsvc.exe /S /B
where /r . taskhostsvc.exe
You can use the following commands to look for files on Windows
dir taskhostsvc.exe /S /B
where /r . taskhostsvc.exe
SUNSPOT used a scheduled task set to execute when the host boots
You can find Scheduled Tasks so many ways; two methods are to use Autoruns (from sysinternals) or browse the registry:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree

You can find Scheduled Tasks so many ways; two methods are to use Autoruns (from sysinternals) or browse the registry:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Schedule\TaskCache\Tree


SUNSPOT creates an encrypted log file at the following location:
C:\Windows\Temp\vmware-vmdmp.log
Check for the presence of file using techniques above, and decrypt the file using CyberChef
C:\Windows\Temp\vmware-vmdmp.log
Check for the presence of file using techniques above, and decrypt the file using CyberChef

Finally, the malware was known to use a Mutex to ensure it only runs one instance at a time.
You can use Handle from sysinternals to identify all mutexes on the endpoint and couple it with findstr to identify entries of interest.
You can use Handle from sysinternals to identify all mutexes on the endpoint and couple it with findstr to identify entries of interest.

Note, this specific scenario is only really applicable to SolarWinds themselves, but the same techniques can be applied across usual threat hunting scenarios.
Original research from CrowdStrike.
crowdstrike.com/blog/sunspot-m…
Original research from CrowdStrike.
crowdstrike.com/blog/sunspot-m…
• • •
Missing some Tweet in this thread? You can try to
force a refresh